Every step documented before it happened. We knew the playbook. We were ready.
2023 — First abuse reports
20+ reports filed through NameSilo's own portal
PhishDestroy submitted 20+ abuse reports about xmrwallet.com and operator-linked mirrors through NameSilo's abuse portal between 2023 and 2026. We hold every delivery receipt — confirmation pages, ticket IDs, automated acknowledgements. Independent researchers had been reporting the same domain for years. Based on archived victim threads and deleted accounts, the real number of reports NameSilo received is likely well over 100. They later claimed: "we had received no abuse reports."
2023–2025 — Years of research
Mapping the operator's suppression machine
Before publishing a single word, we spent years documenting how the operator kept a $20M+ theft operation alive for a decade. His strategy: delete everything, everywhere. What he couldn't delete — he buried.
Deletion: DMCA takedowns against Google, GitHub, domain registrars. Mass-reporting Trustpilot reviews (100+ removed). Filing abuse reports using government email addresses. Taking down YouTube analysis videos. Coordinated reporting on BitcoinTalk, Reddit, Twitter.
SEO burial: We nicknamed him "SEO Grandpa" because his second weapon was parasitic SEO. He ordered 50+ paid articles through Kwork, Freelancehunt, and more expensive intermediaries — all sponsored content placed on third-party sites to push victim complaints out of search results. His freelance orders, complete with article texts and link-building instructions, are still indexed on Google Drive in plain sight. When we got one sponsored article taken down, the host site publicly confirmed it was paid placement. He bought low-quality backlinks at scale, parasitizing the "xmrwallet" brand name built on theft.
The code theater: The operator publishes "open source" code on GitHub to appear legitimate. But the actual site is hosted on DDoS-Guard — a bulletproof hosting provider. If the code is honest, why use DDoS-Guard? Because the production code contains session_key exfiltration, encrypted payloads, and server-side TX construction that don't exist in the public GitHub repository.
We mapped the entire playbook. We knew exactly what would happen. We prepared for every step.
2023–2026 — Domain takedowns
We took down his escape domains. One by one.
The operator registered xmrwallet mirror domains across multiple registrars with 5–10 year registration periods — pre-paid escape routes for when domains got banned. Each clone was linked directly from the main site (all archived in Wayback Machine), hosted on IQWeb / DDoS-Guard, with identical code hashes across every mirror. We systematically reported and took them down, one after another, at different registrars. A "legitimate open-source wallet" does not need pre-registered escape domains across five registrars for a decade. Strange behavior for someone who was allegedly "compromised," isn't it? Perhaps the "hacker" was also kind enough to register backup domains years in advance and host them on bulletproof infrastructure.
February 16, 2026 — Operator's first email
"You are incorrect with your report"
The operator contacted us directly, demanding we remove our report:
"Hi, You are incorrect with your report. There is no phishing going on with xmrwallet.com, this is the official domain name for xmrwallet. We are an open source crypto wallet that is non-custodial, we don't store seeds or keys, everything is done in your browser locally. Please remove your report on us, thank you. N.R."
He claimed the site was working normally. He did not claim he was hacked. He told us to remove our report.
Screenshot →
February 2026 — Escalation
Story changes. Then come the threats.
When confronted with the technical evidence — server-side TX hijacking, session_key exfiltrating wallet addresses and private view keys, 8 PHP endpoints, Google Analytics tracking victims — the operator stopped claiming innocence:
"What they use is what they need."
Then came the threats. The operator was confident. He had his registrar. He believed he was untouchable — that we could be silenced like everyone before us. He even suggested we could be taken to court through the registrar. He was wrong about all of it.
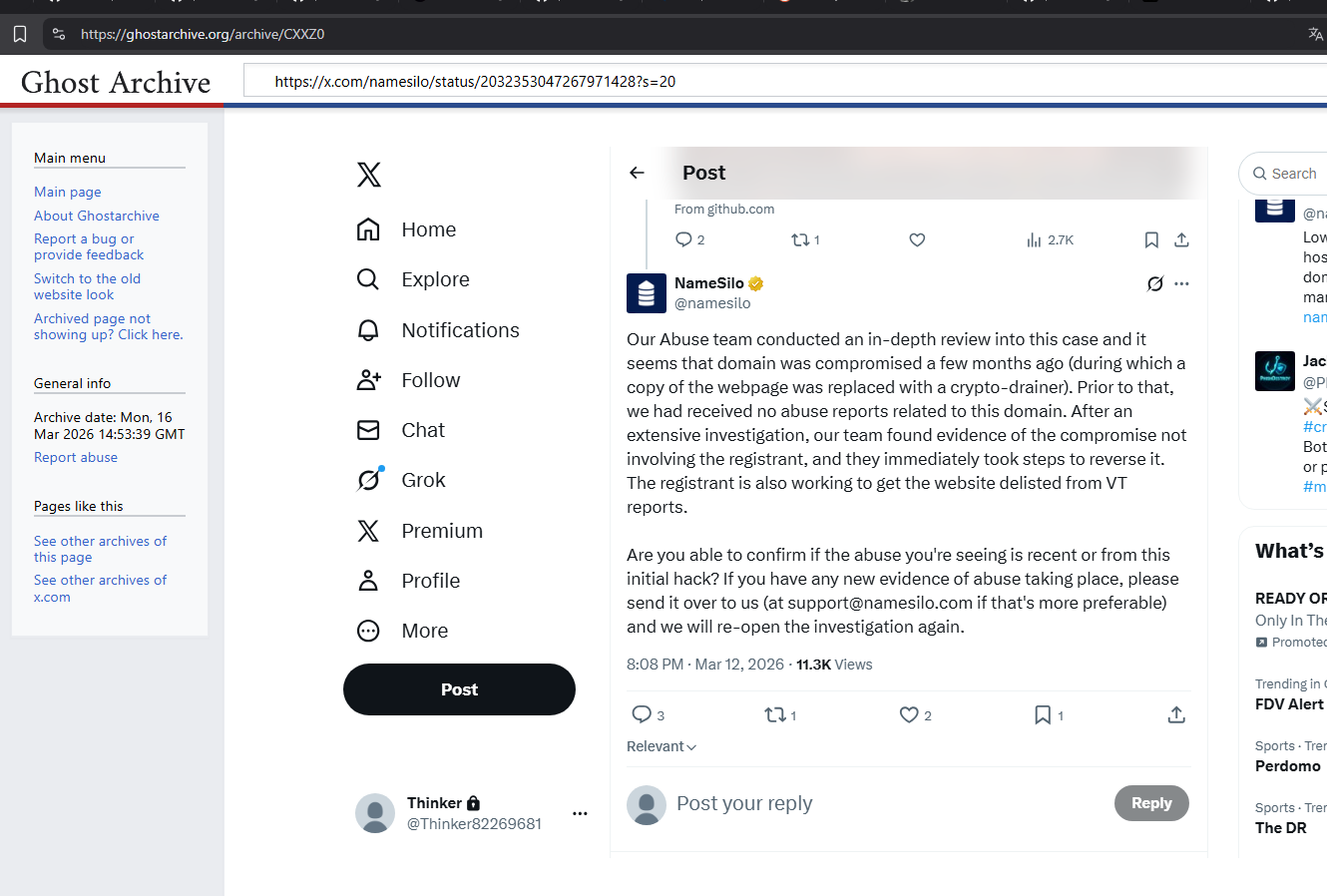
March 13, 2026 — NameSilo's public tweet
4 sentences. 4 verifiable lies.
NameSilo's official corporate account publishes a public defense of xmrwallet.com:
"Our Abuse team conducted an in-depth review... the domain was compromised a few months ago... Prior to that, we had received no abuse reports... [working with the registrant to remove the website from VT reports]."
Lie #1: "Compromised" — We have
SHA-256 hashes of the site code from before and after the alleged "compromise" window. The code never changed. The IP never changed. NameSilo invented this story. The operator himself never claimed compromise in his emails — he said the site was working normally.
Lie #2: "No abuse reports" — 20+ from us alone since 2023, with delivery receipts. Likely 100+ total from all reporters.
Lie #3: The operator was directly involved — he emailed us defending his code.
Lie #4: A registrar publicly committing to
remove VirusTotal detections for a known drainer. Not investigate. Not suspend. Help the scammer avoid detection.
Full debunking →
March 16, 2026 — Receipts published
@Phish_Destroy posts the rebuttals
Three rebuttals posted to Twitter, each citing the operator's own emails: "@NameSilo is lying", "@NameSilo is acting as press secretary for a $20M+ theft operation", and "Who is this operator to you?" Every tweet archived to Wayback Machine and GhostArchive within minutes of posting — before the lock came. We also tagged NameSilo under older threads from other researchers documenting xmrwallet going back to 2022.
March 18, 2026 — ICANN & law enforcement
Full case file submitted
Complete evidence package forwarded to ICANN Contractual Compliance and federal law enforcement. SHA-256 verified screenshots, archived tweets, email headers, operator communications, all delivery receipts for ignored abuse reports. Announced publicly on Twitter. This post appears to have triggered what came next.
Late March 2026 — Silenced
Gold Checkmark used to lock @Phish_Destroy
Days after the ICANN escalation, @Phish_Destroy is permanently locked. X Support: "Our support team has determined that a violation against inauthentic behaviors occurred." No tweet quoted. No rule cited. The signature of a human-agent decision via the paid Gold Checkmark live-support channel — concierge censorship you can buy.
April 15, 2026 — X contradicts itself
"No violation. Account restored." — Still locked.
On appeal, X Support:
"Our automated systems have determined there was no violation and have restored your account to full functionality." Subject:
"Your account has been restored." The account is still locked. The subscription is still billed. X's own automation cleared us. The Gold Checkmark override persists.
Screenshot →
April 2026 — Full suppression
Bing, DDoS, DMCA, content scrubbing
All phishdestroy.io results removed from Bing. DDoS traffic against phishdestroy.io correlated with NameSilo's abuse-tolerant infrastructure. DMCA requests filed against Google results. Coordinated reporting against GitHub repos, Medium articles, public mirrors. Every surface with a "report" button — weaponized.
May 2026 — This archive
IPFS + Ethereum Name Service. No "report" button.
Every takedown made the archive bigger. The operator and NameSilo occupy the same side. Both seem confident their arrangement will survive scrutiny. It won't. We are also aware that criminal cases related to xmrwallet are open in Europe. This archive will serve as evidence.