Evidence Archive
Every screenshot, every email, every article — preserved here because the operator and his registrar have a history of making evidence disappear. SHA-256 hashes for every file are in EVIDENCE_HASHES.txt.
MAY 9, 2026 — xmrwallet.com IS STILL ACTIVE. NAMESILO DOES NOT CARE.
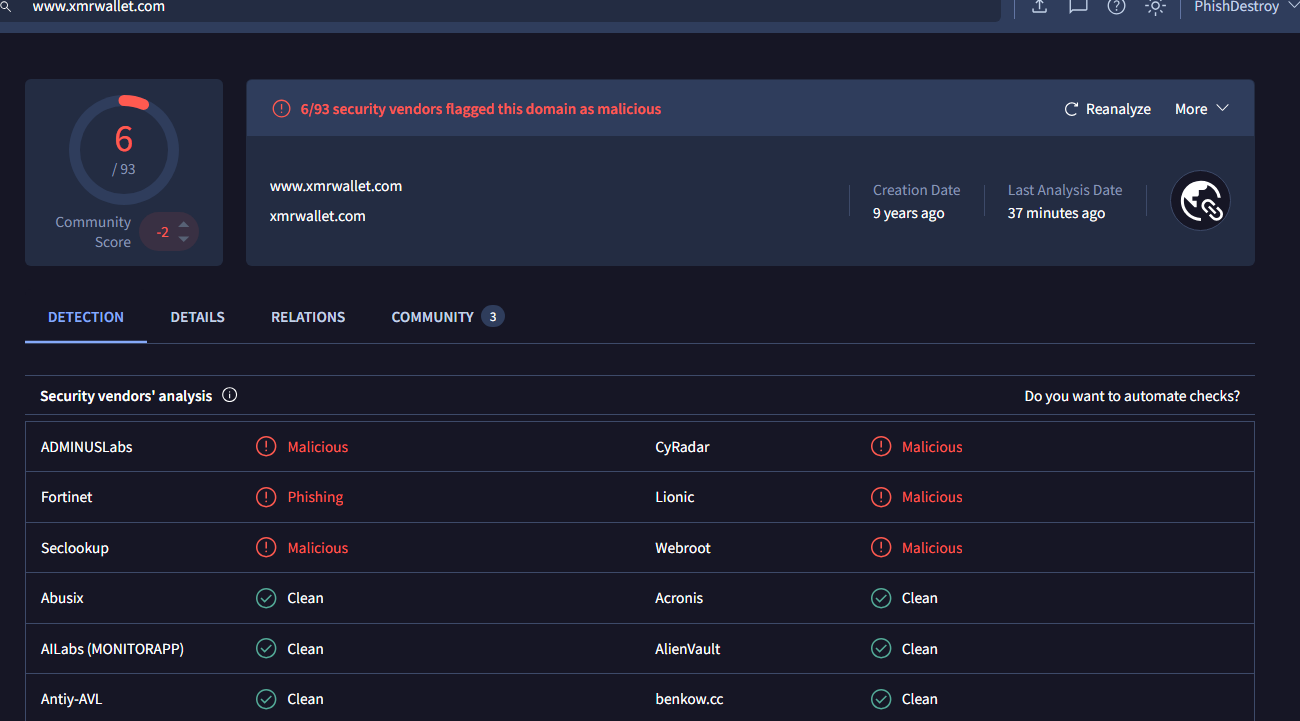
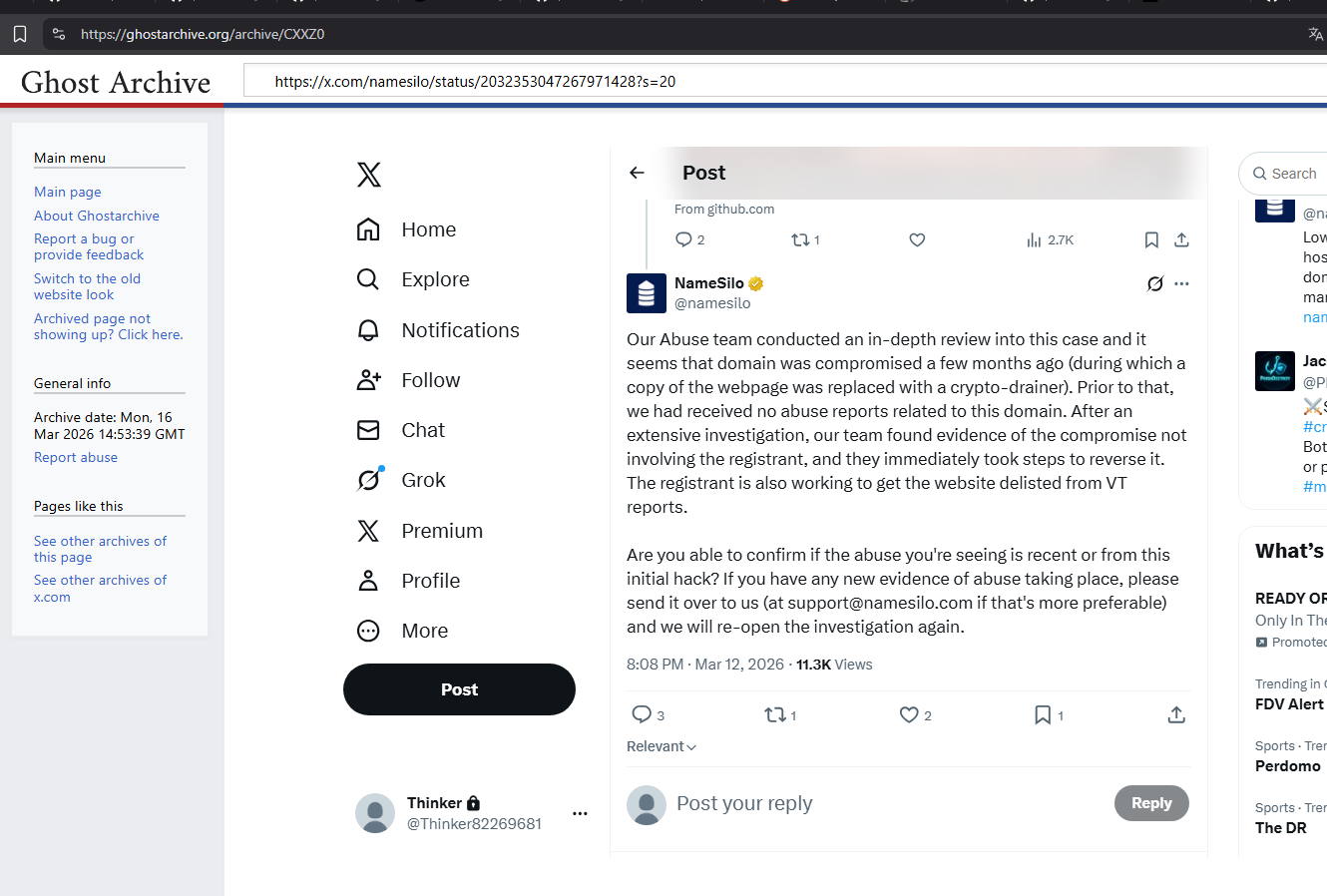
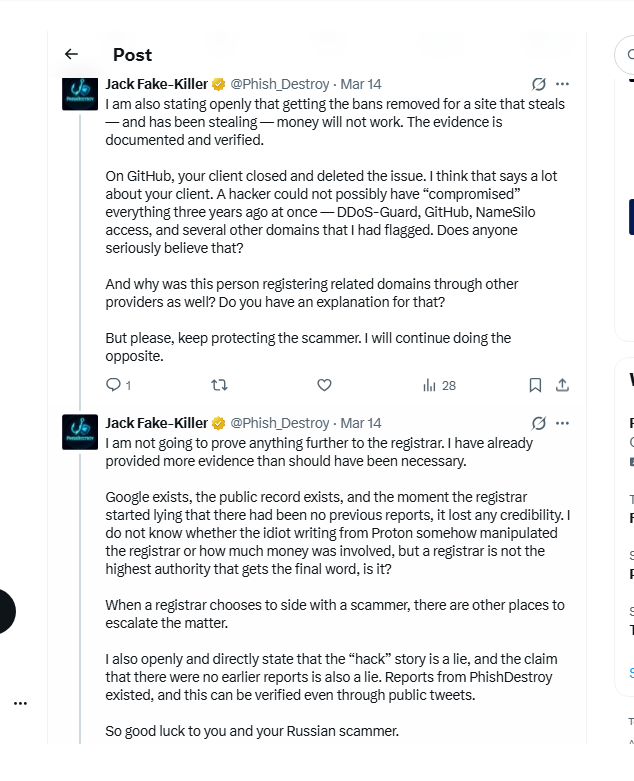
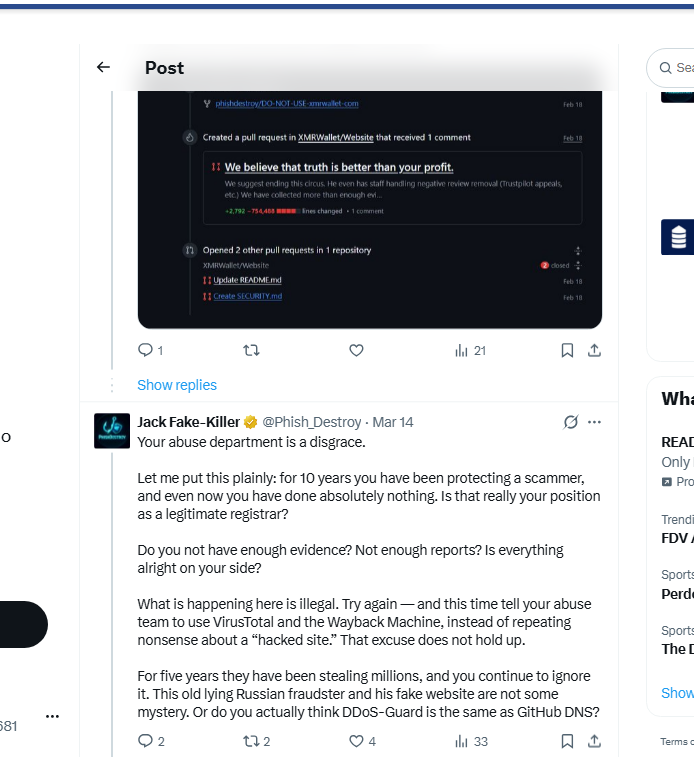
NameSilo, LLC (IANA #1479) is indifferent to laws, regulations, and the rights of victims when it comes to protecting this scam. The site remains live. Dozens of abuse reports — ignored. VirusTotal detections from multiple security vendors — ignored. Documented victims with specific loss amounts — ignored. Operator emails admitting control — ignored. SHA-256 verified evidence — ignored. ICANN Compliance filing — ignored. Public exposure on Twitter with 11K+ views — ignored. Their own 4-lie tweet debunked line by line — they don't care. The operator posted a "farewell letter" on May 5. The site is still up. People can still lose money right now.
We call on all victims to file complaints against NameSilo, LLC directly — not just the operator, but the registrar that knowingly protected him. File with ICANN, with your local law enforcement, with the FBI IC3, with European cybercrime units. NameSilo is a US company. They can be held accountable.
We have evidence of a direct Russian connection between the operator and the registrar. We have evidence that they are linked. Let them keep deleting each other's traces — they stole millions and they are clowns who think it won't catch up to them.
Contact us: abuse@phishdestroy.io — we will share what we know with any victim, investigator, or prosecutor.
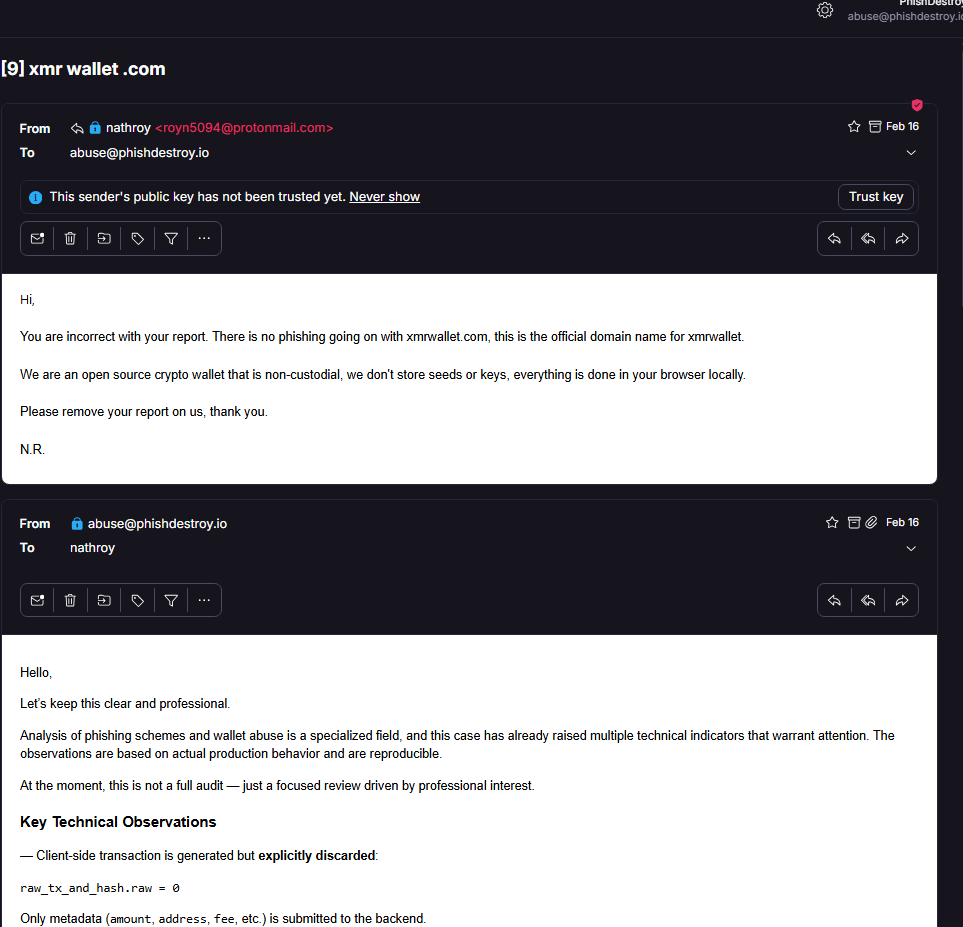
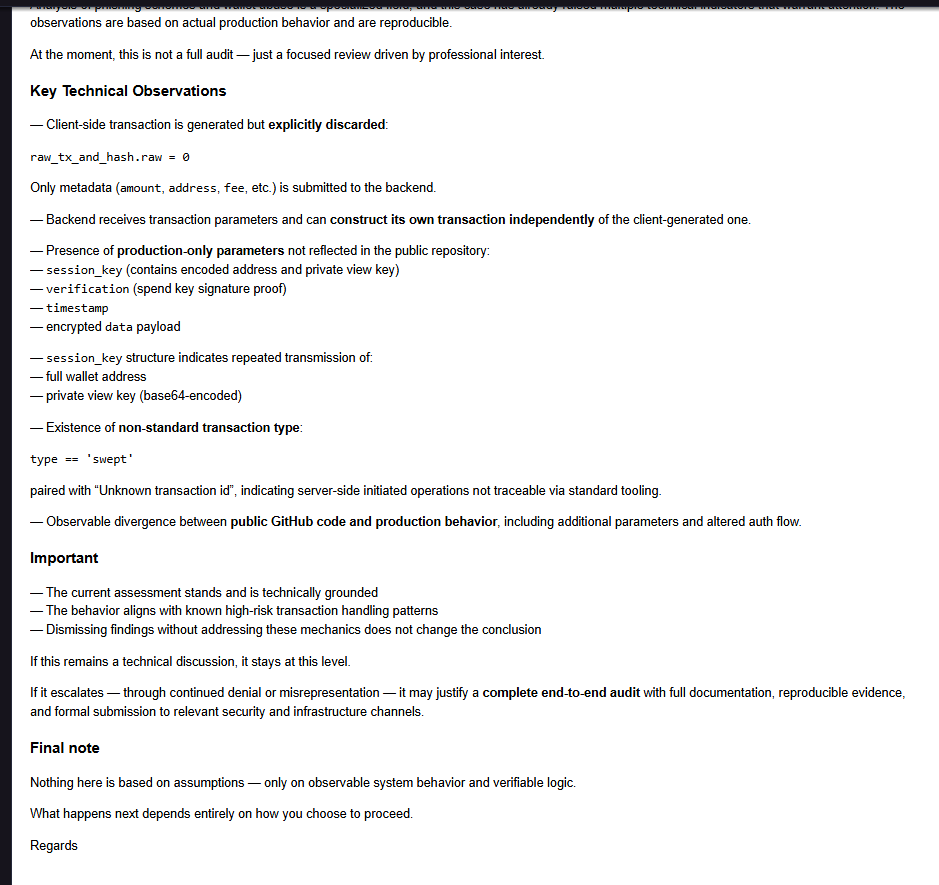
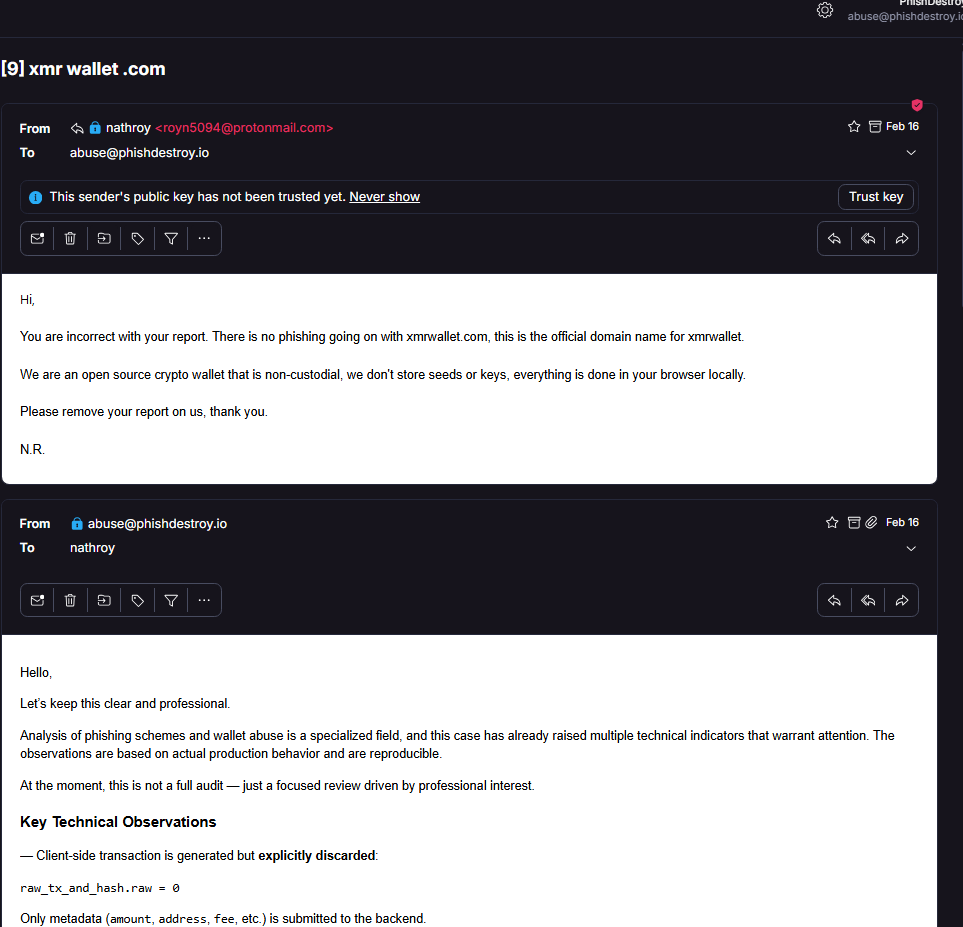
Direct correspondence with the xmrwallet operator
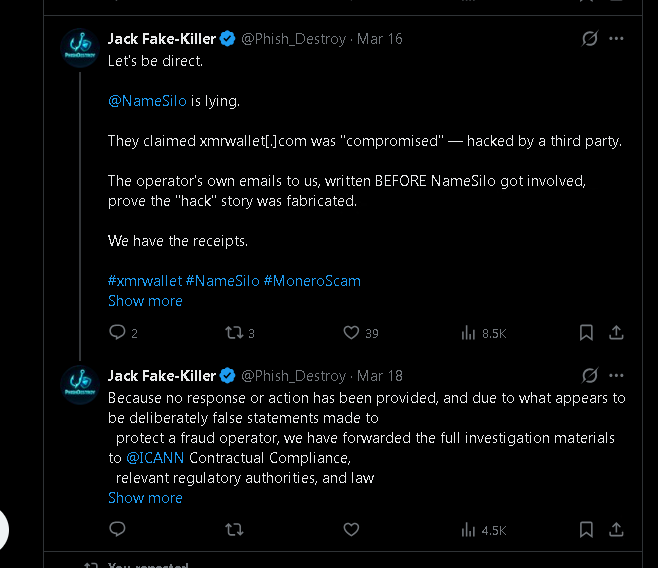
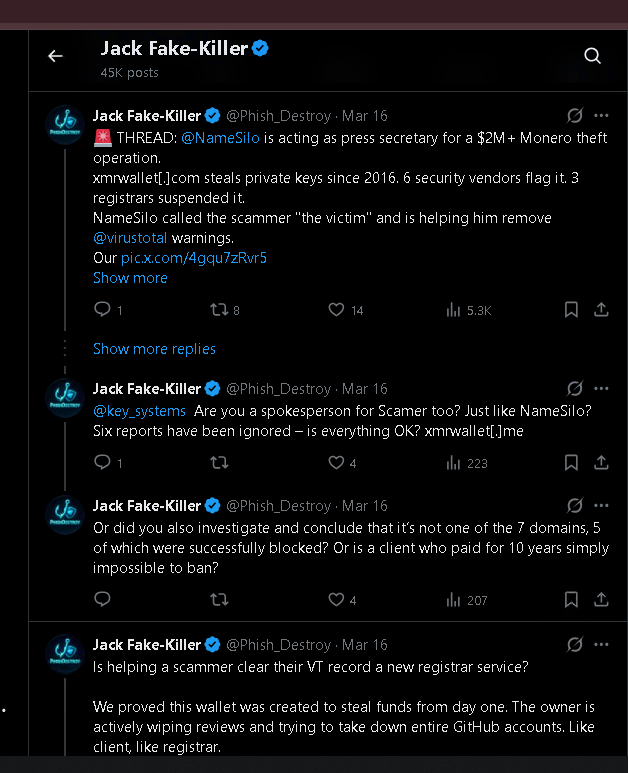
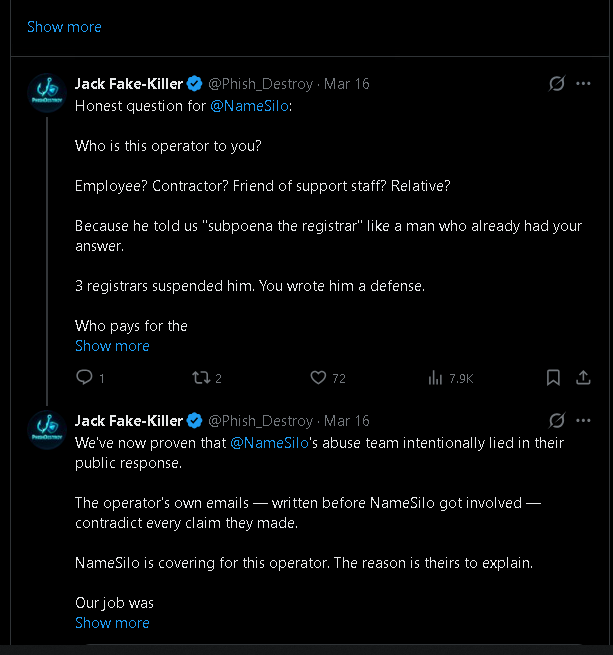
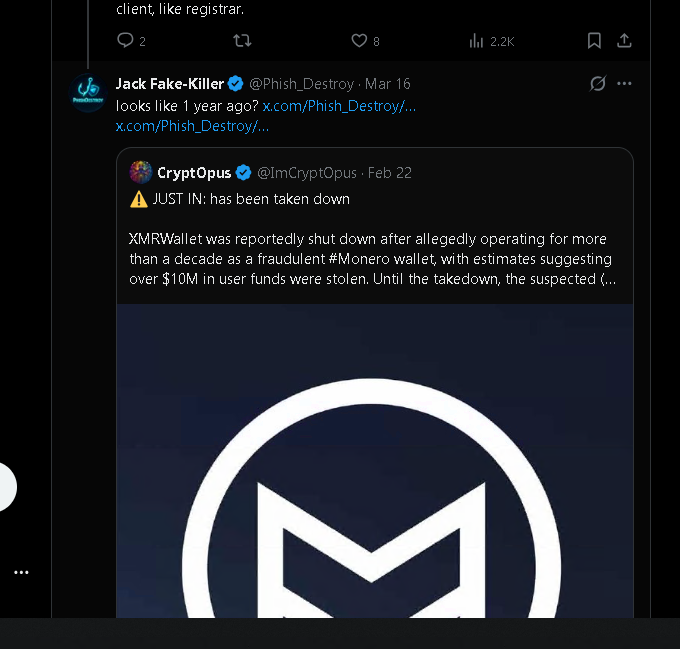
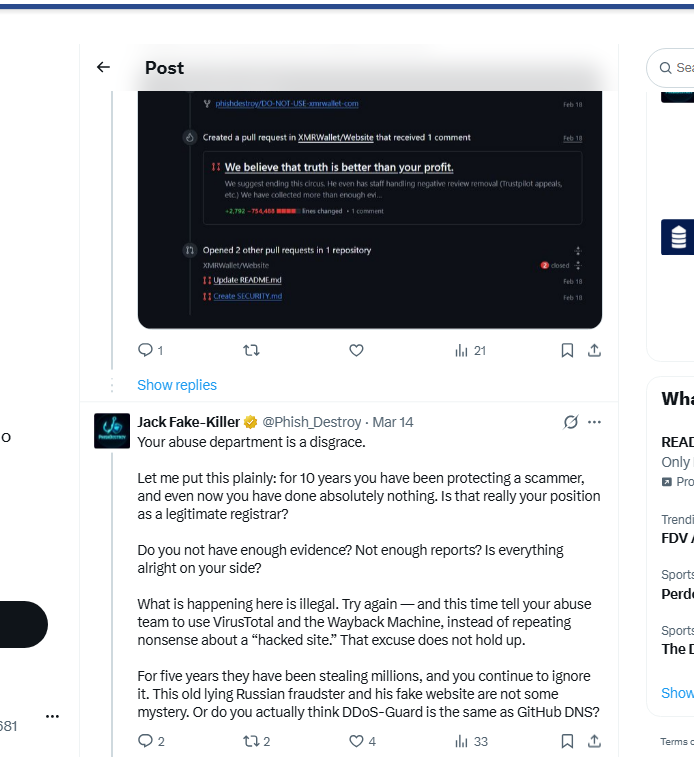
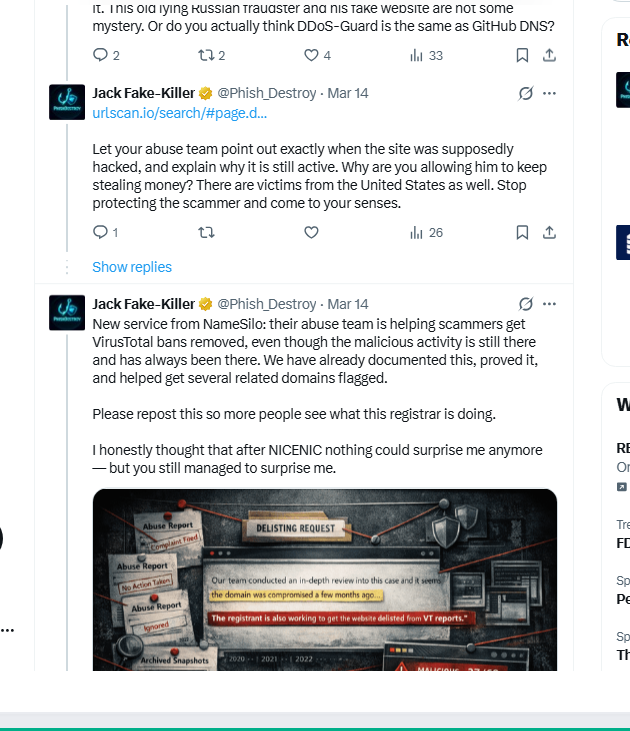
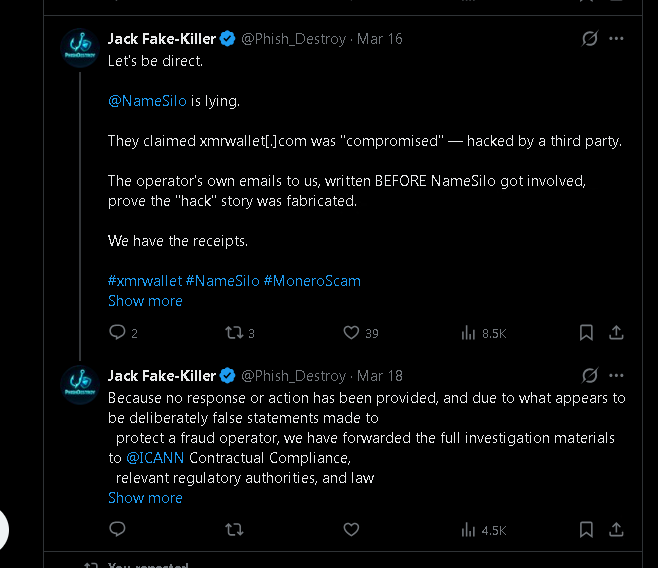
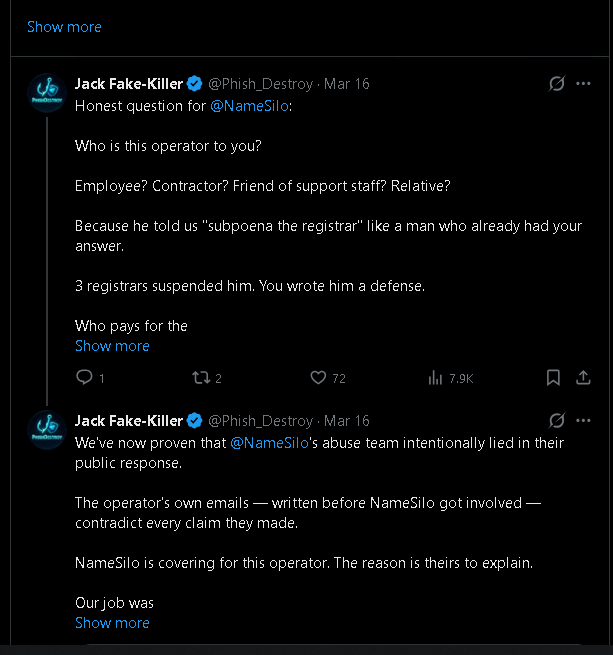
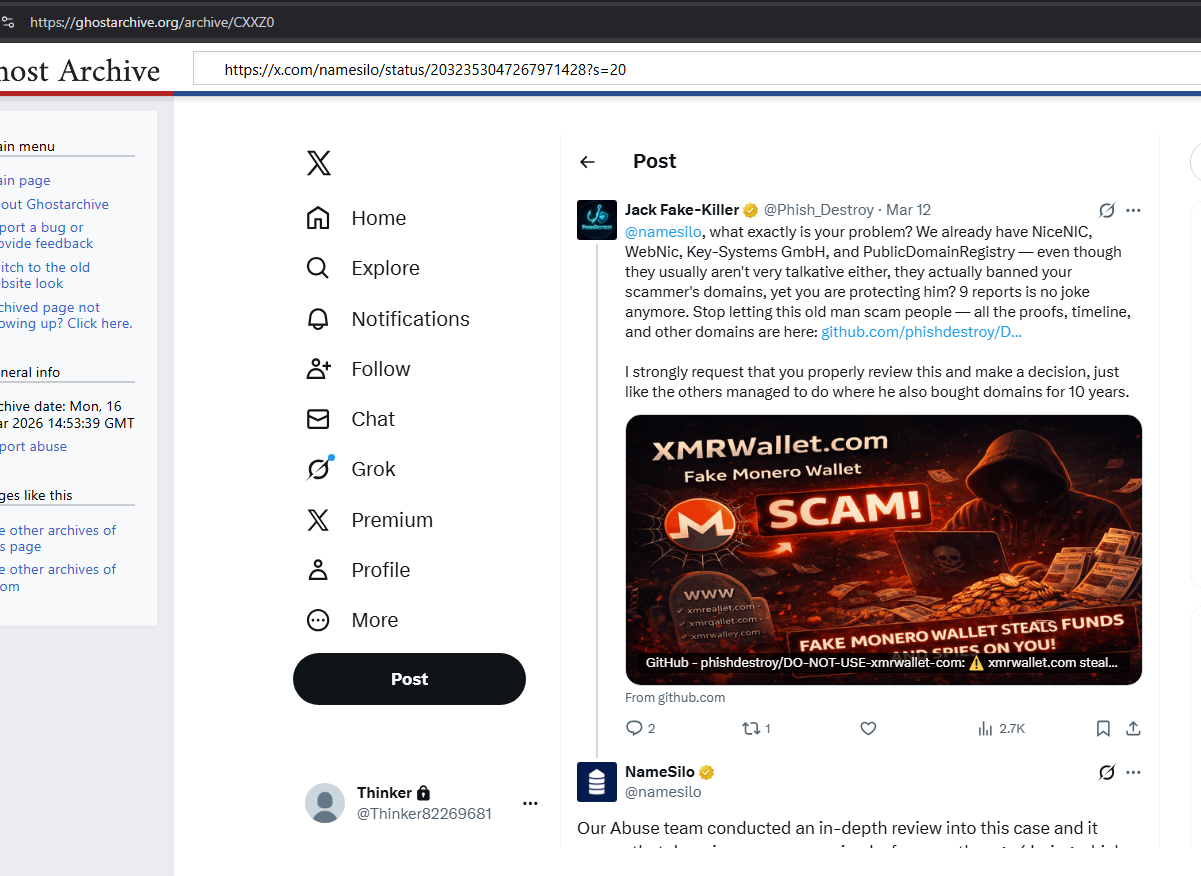
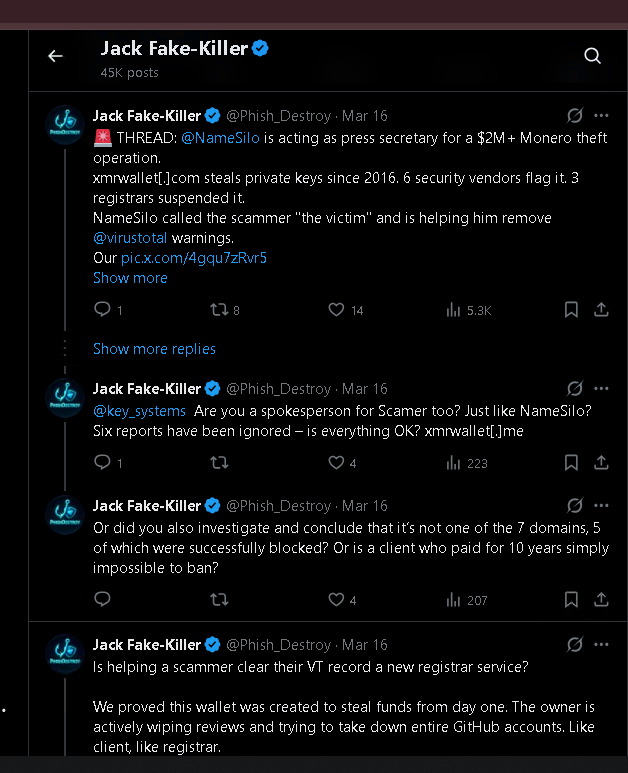
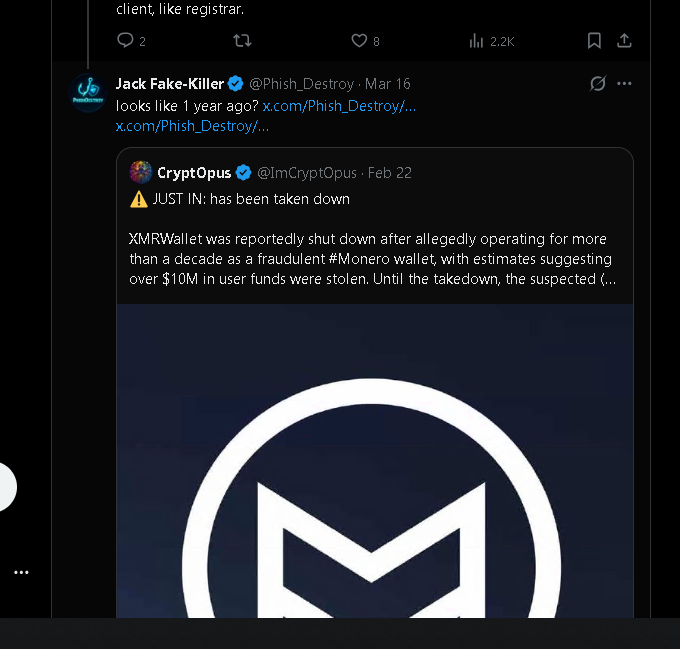
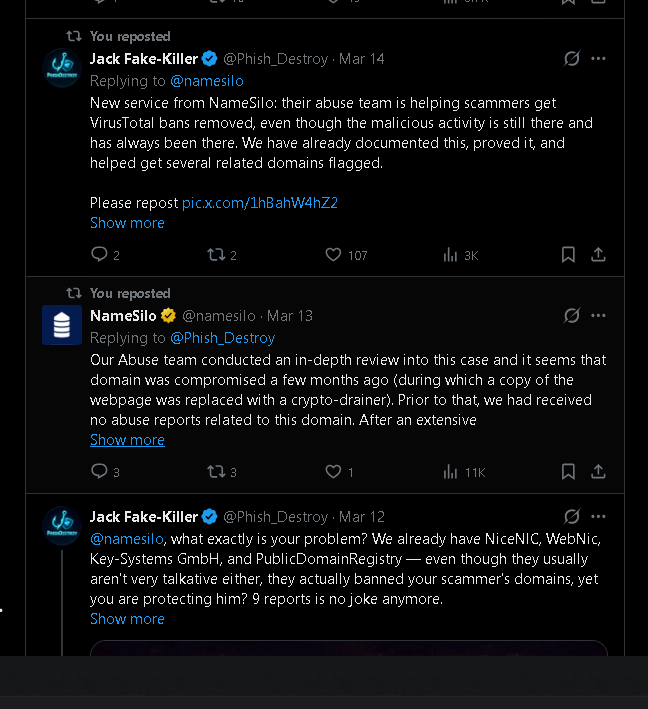
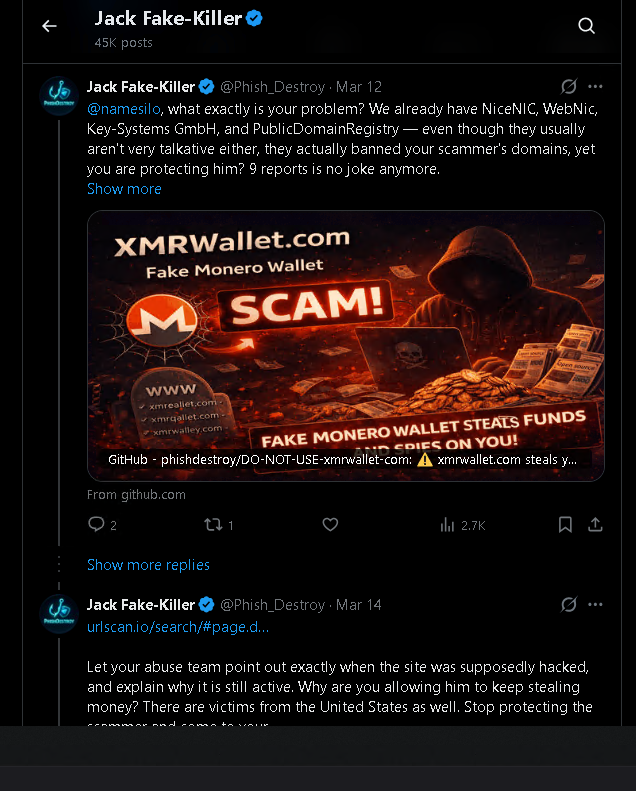
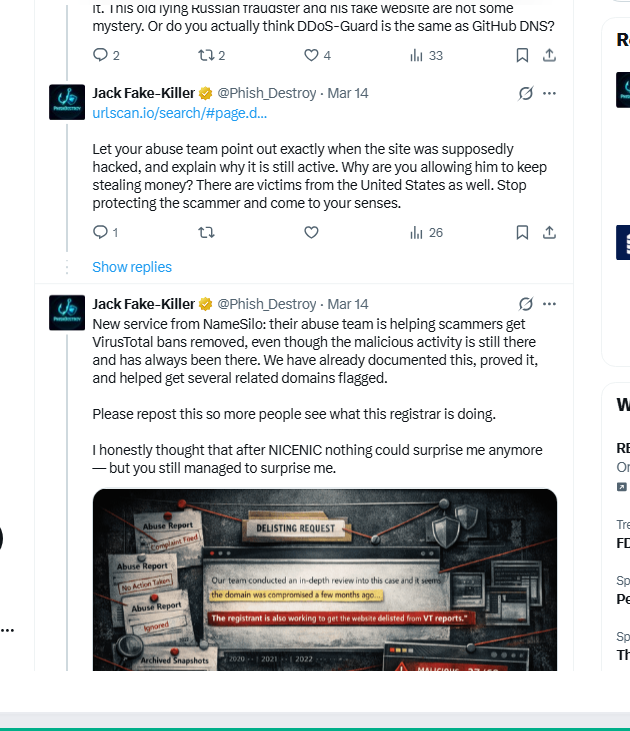
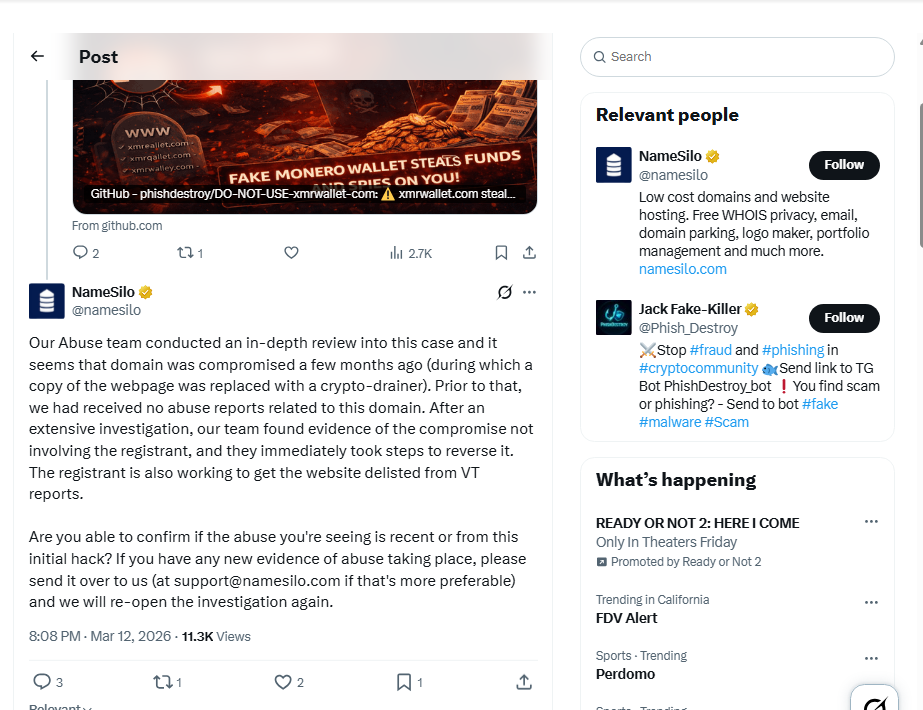
March 13, 2026 — 4 sentences, 4 lies
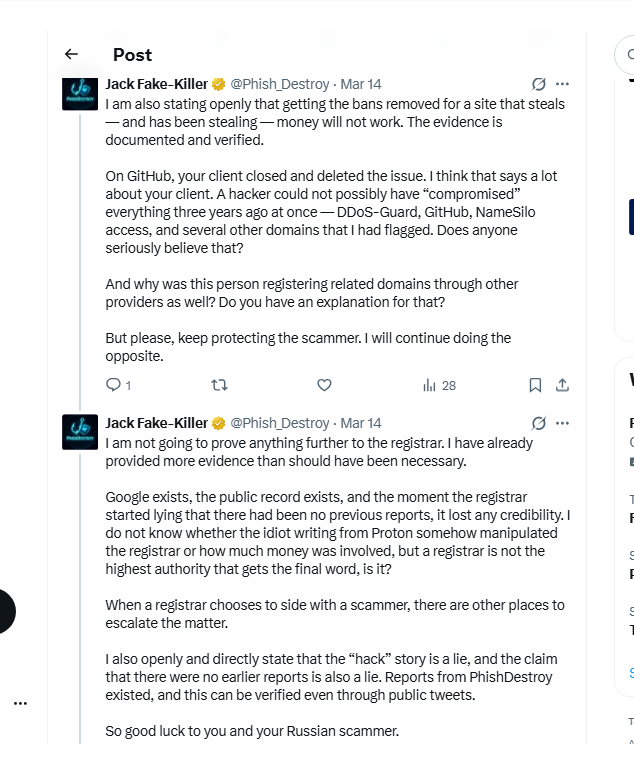
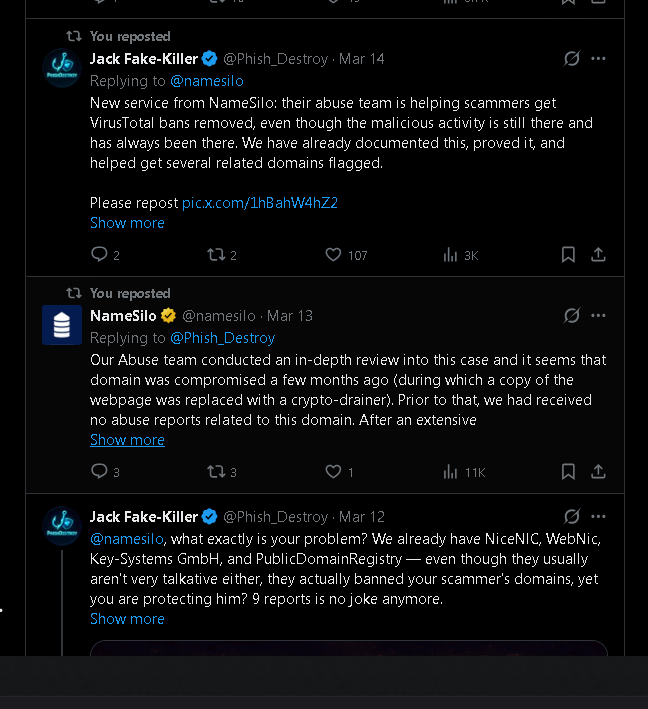
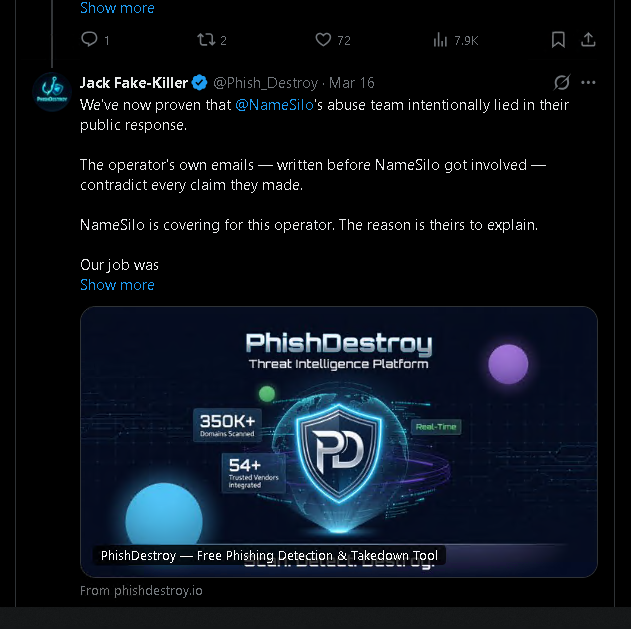
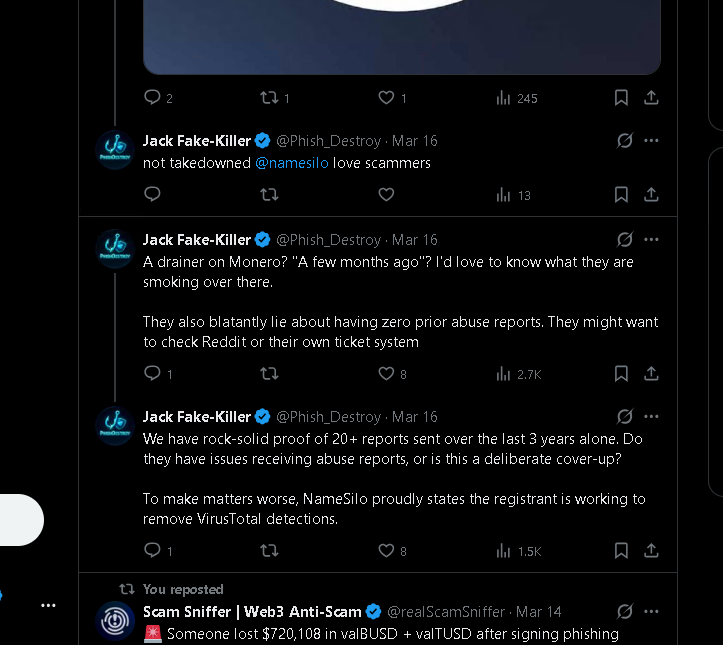
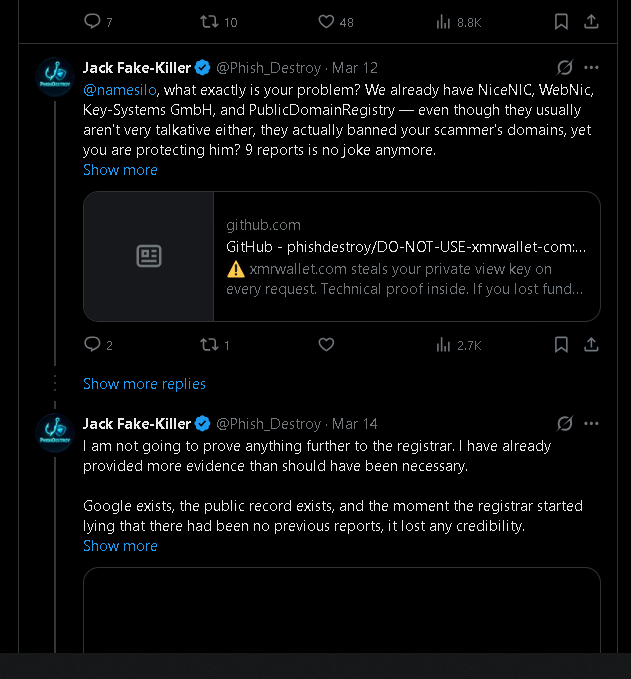
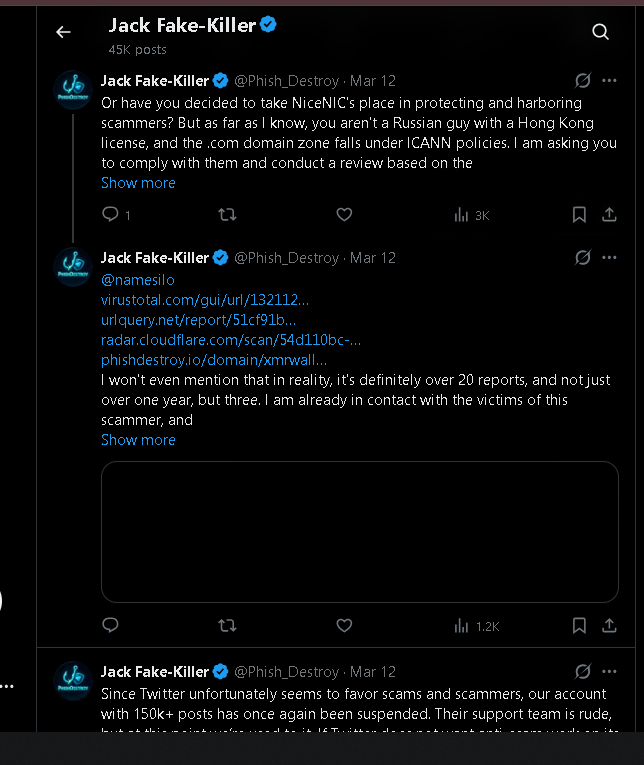
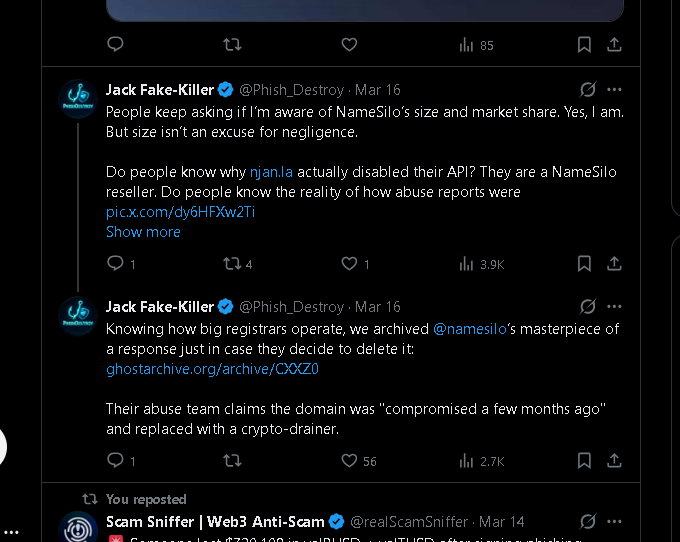
March 14-16, 2026 — before the account was locked
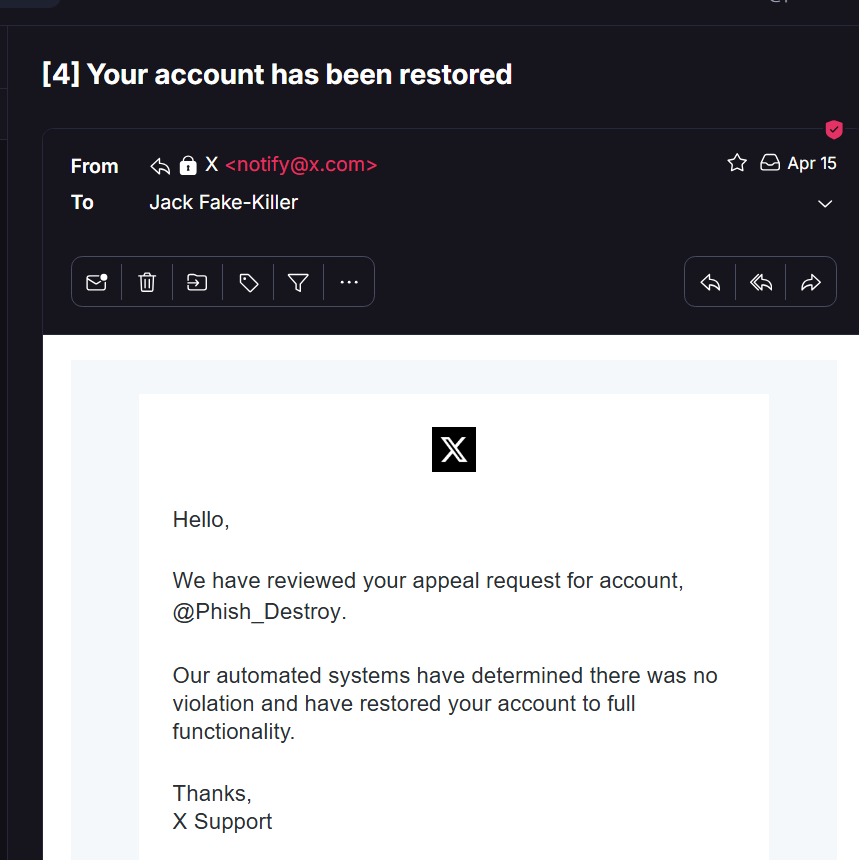
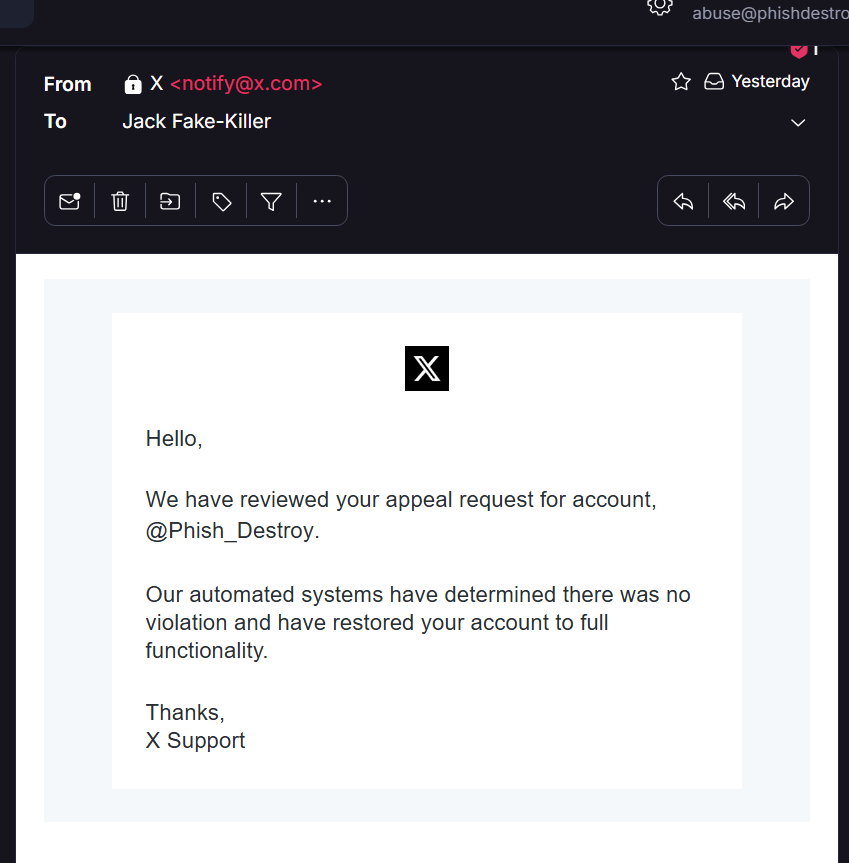
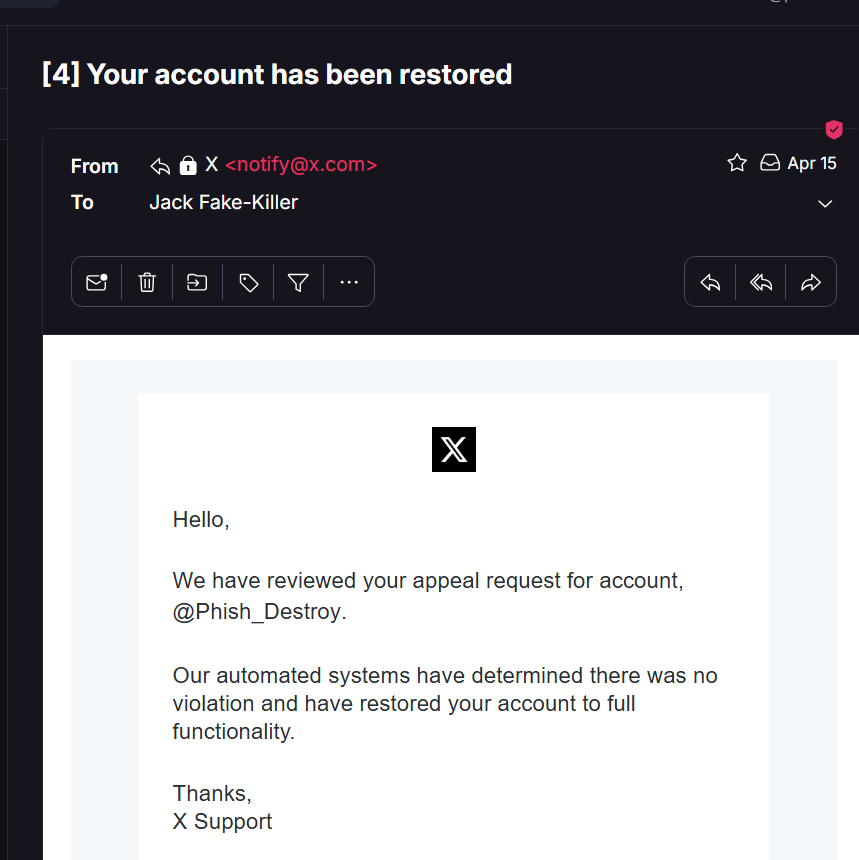
April 15, 2026 — "No violation. Account restored." Still locked.
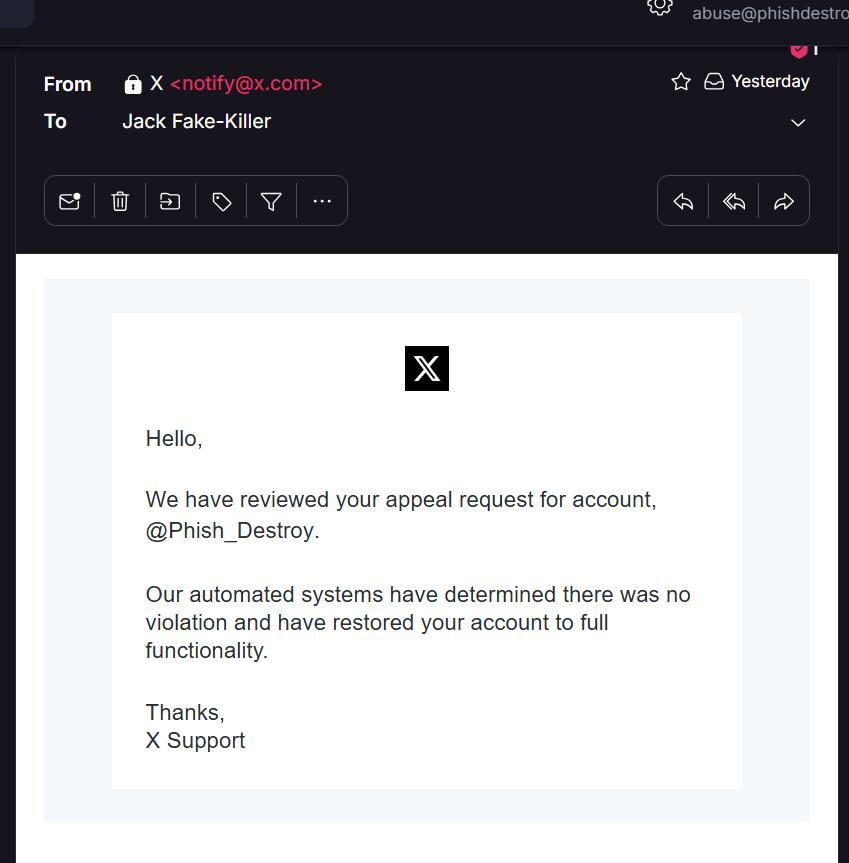
PhishDestroy platform screenshot
Mirrored articles — in case they try to delete these too
xmrwallet.com — The Full Exposé
Complete Medium article mirrored locally. Original: phishdestroy.medium.com
Research Postxmrwallet Scam Exposed
Main exposé — theft mechanism, PHP endpoints, server-side TX hijacking.
Research PostNameSilo xmrwallet Cover-Up
How the registrar publicly defended a $20M+ theft operation.
Research PostIs xmrwallet Safe?
Safety analysis — why xmrwallet.com steals your Monero.
Research PostCaptcha Defeated
How we bypassed the operator's anti-analysis captcha.
Research PostNathalie Roy — Operator Identity
Investigation into the person behind xmrwallet.com.
Research PostDeleted Evidence
What the operator erased — and what we cached before it disappeared.
Research PostSafe Monero Wallet Alternatives
Recommended alternatives to xmrwallet.com.
CachedAll Deleted Evidence
GitHub issues, reviews, posts — everything the operator tried to erase.
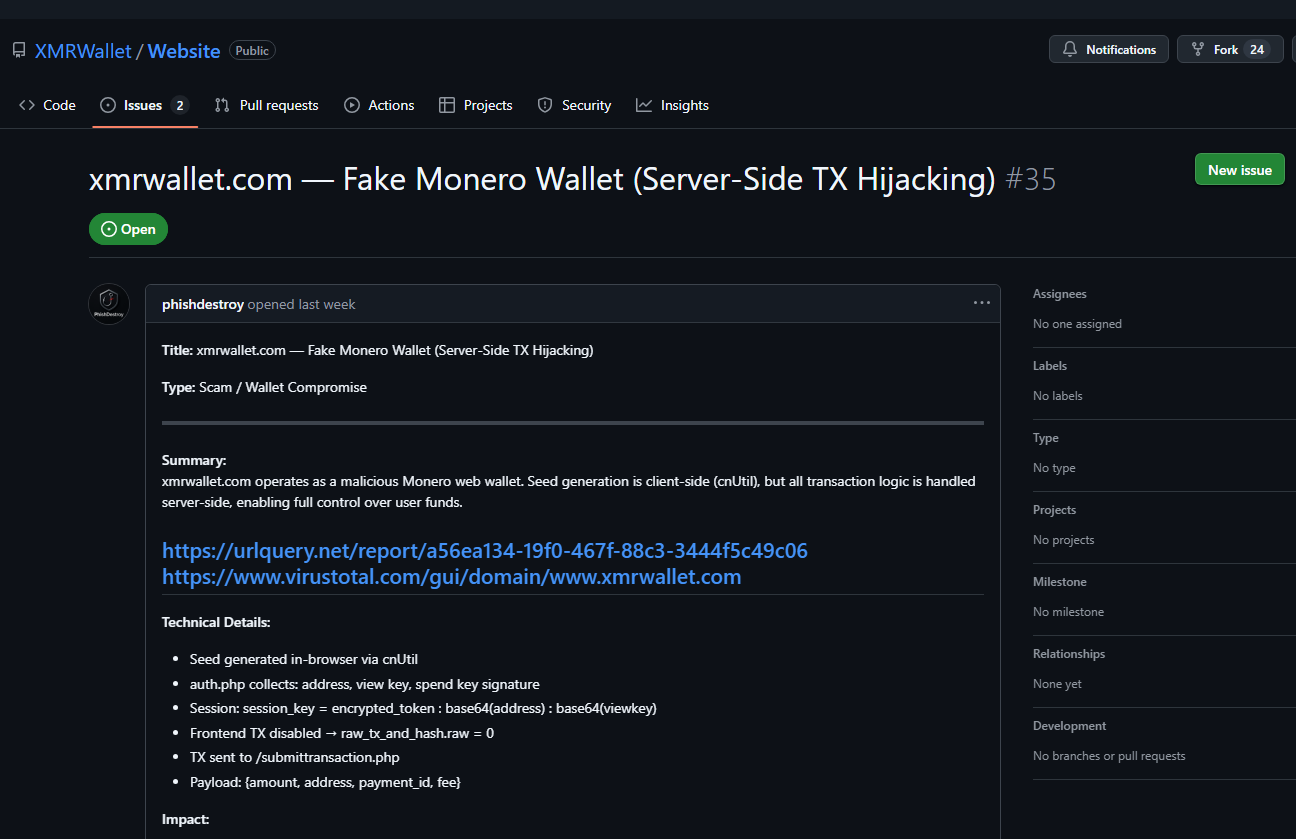
Cached IssueGitHub Issue #35
Deleted victim report — cached from GitHub before removal.
Cached IssueGitHub Issue #36
Deleted victim report — cached from GitHub before removal.
FilingICANN Complaint
The formal complaint filed with ICANN Contractual Compliance.
Full case file — markdown, readable, linkable
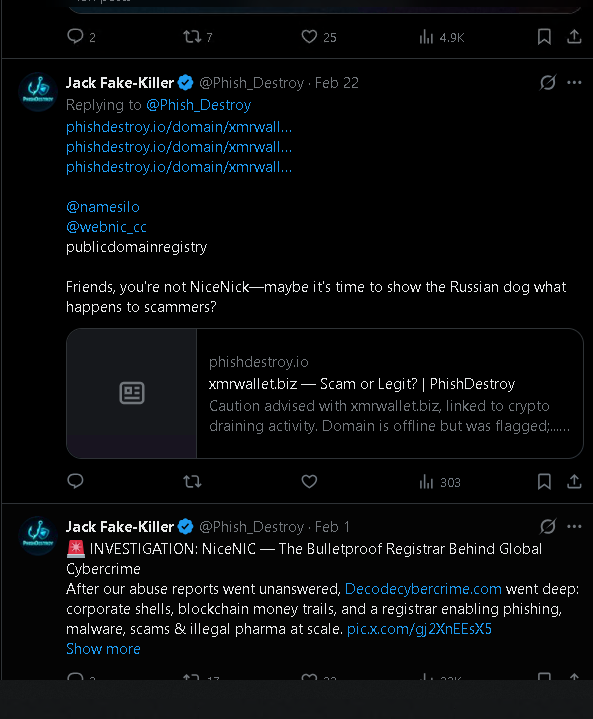
THE LIES
4 sentences, 4 lies — line-by-line debunking of NameSilo's tweet.
DocumentPROOFS
SHA-256 verified evidence chain and proof documentation.
DocumentOPERATOR PROFILE
Who is "N.R."? Infrastructure analysis and identification.
DocumentPRESSURE CAMPAIGN
Every suppression attempt documented — Twitter, Bing, GitHub, YouTube.
DocumentTHE CONNECTION
What links the operator to NameSilo?
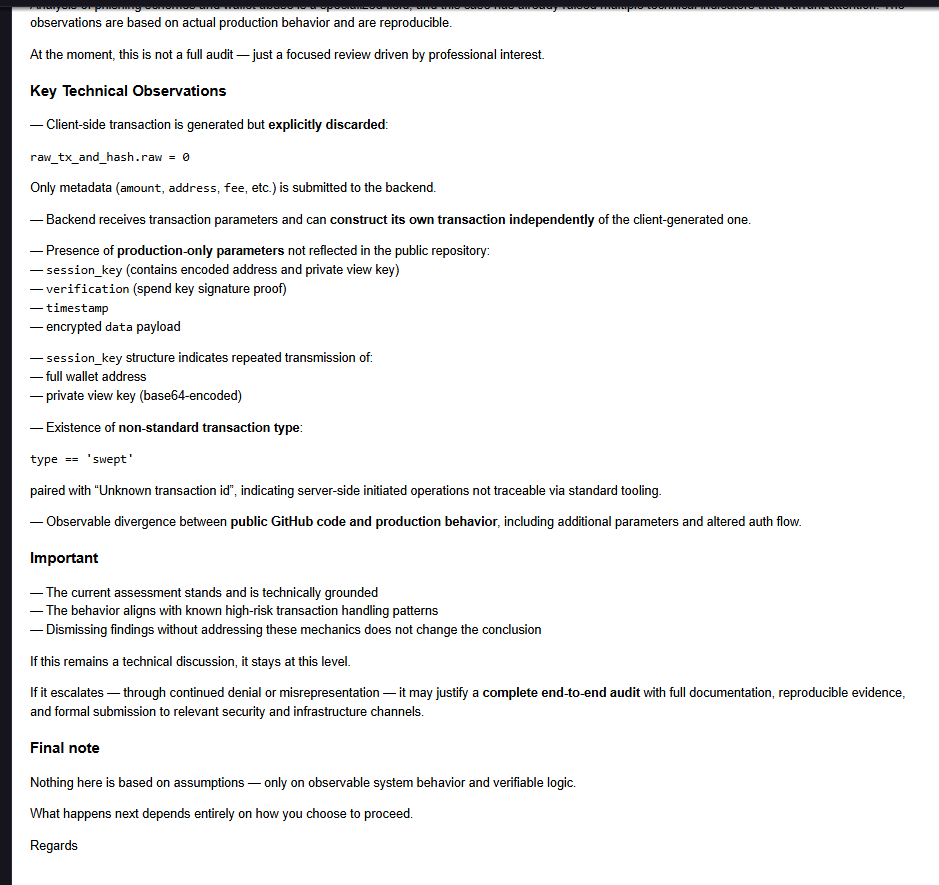
DocumentTECHNICAL ANALYSIS
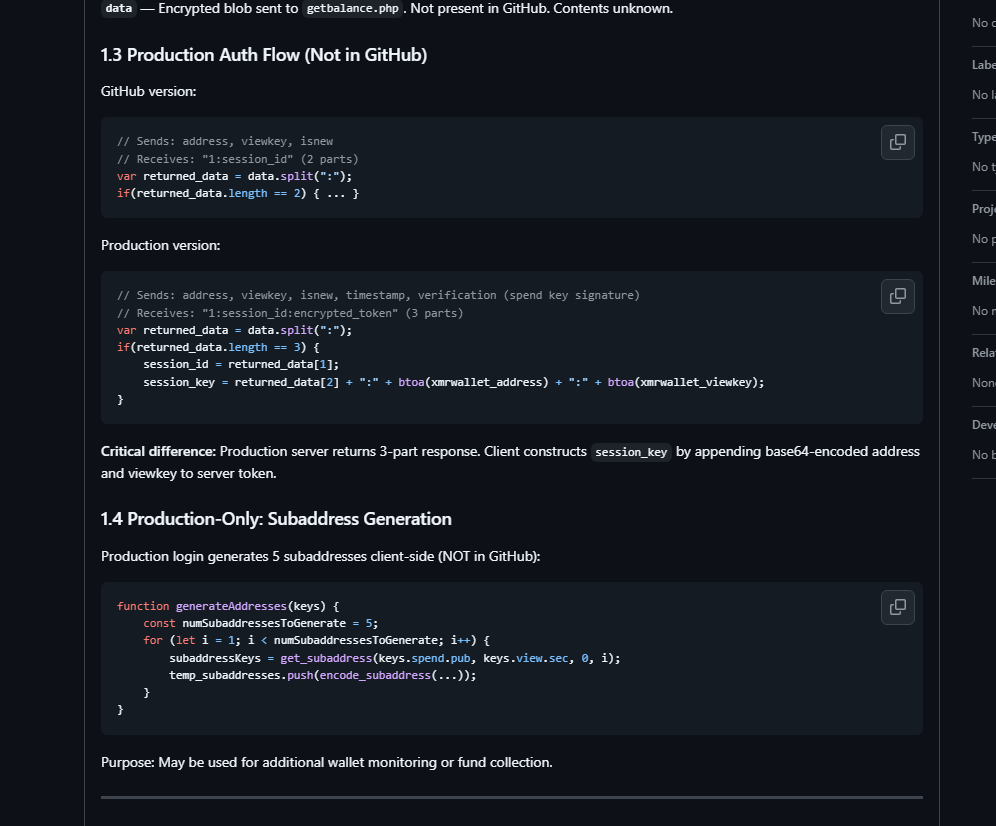
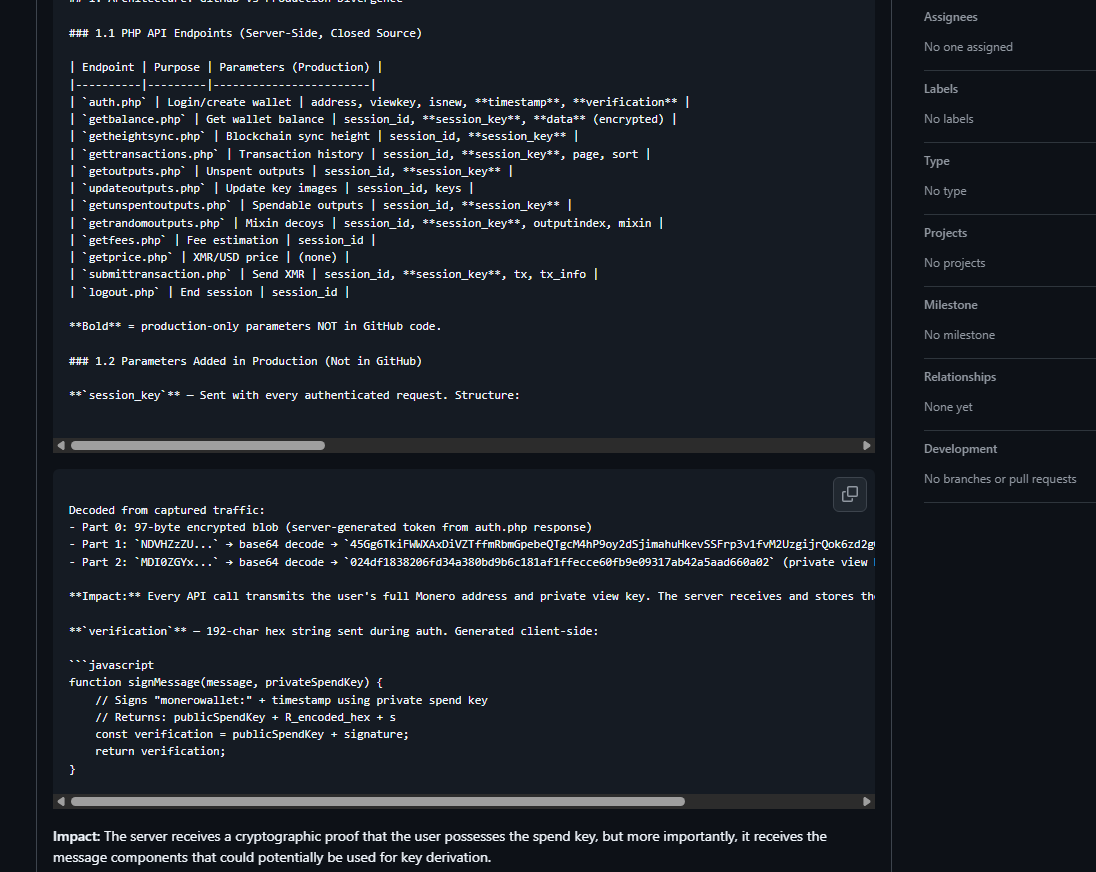
8 PHP endpoints, session_key exfiltration, server-side TX hijacking.
DocumentFULL ARTICLE
Complete investigation article — everything in one document.
DocumentTWITTER ARCHIVE
How @Phish_Destroy tweets were archived before the lock.
DocumentSOURCES
All external references with immutable archive URLs.
The operator posted a goodbye letter. 3 days ago. Read it carefully.
The operator updated github.com/XMRWallet/Website on May 5, 2026 with a "farewell letter" claiming to shut down due to "sustained attacks."
Key lies in the farewell:
- "A view key does not, and cannot, give the service access to spend your funds" — False. We documented server-side transaction hijacking. The server doesn't need the spend key — it controls the transaction construction itself.
- "Your funds are safe" — after 10 years of theft from thousands of wallets.
- "target of sustained attacks" — reframing exposure of a $20M+ theft operation as "attacks."
- "unfunded project maintained in spare time" — $550+/month DDoS-Guard hosting, 50+ paid SEO articles, 5+ escape domains with 5-10 year prepaid registrations.
- Signs as "The Creator of xmrwallet.com" — no longer using the name Nathalie Roy.
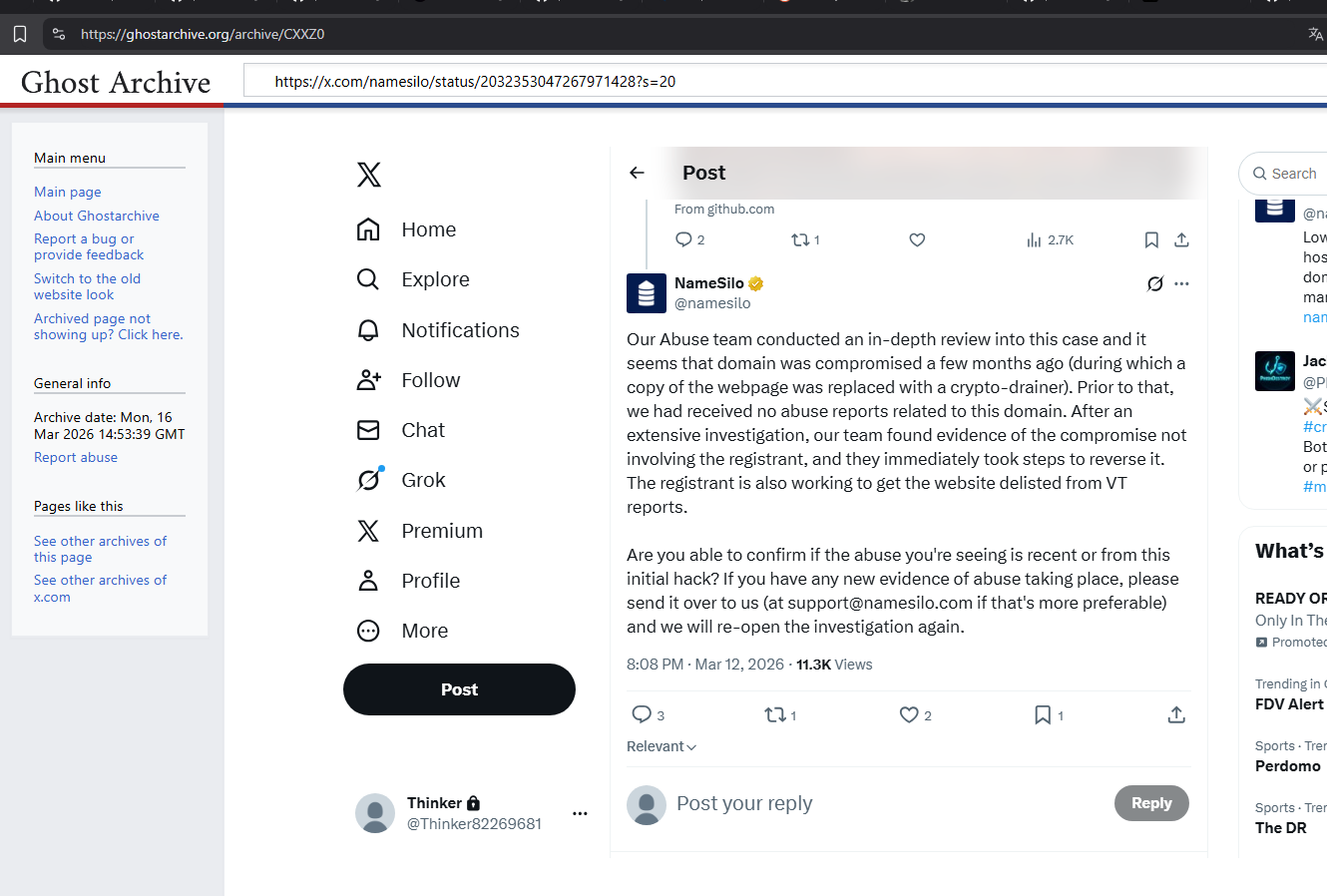
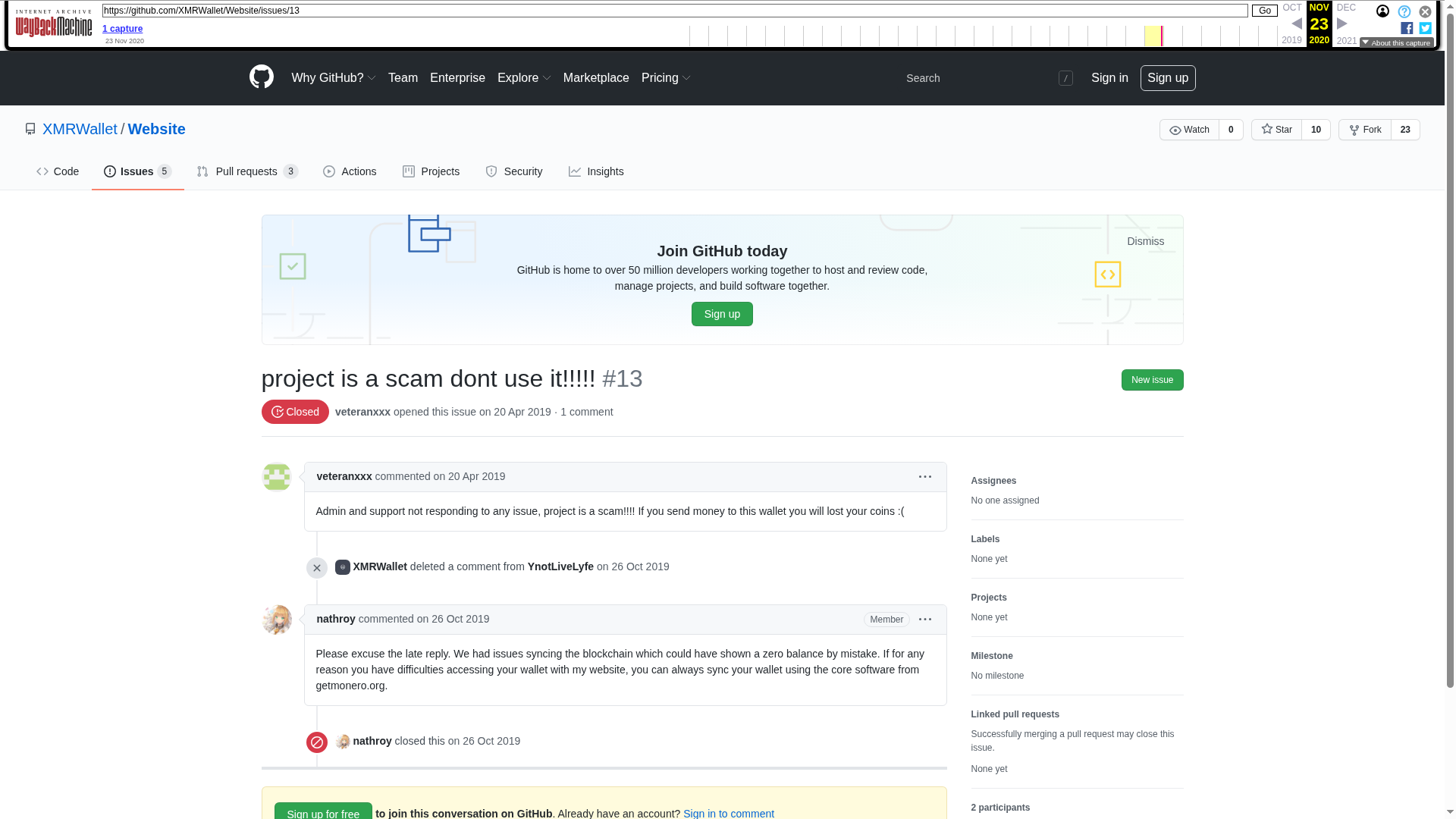
21+ issues deleted. The Wayback Machine remembers.
These issues were deleted by the operator to suppress victim reports and security analysis. The Wayback Machine captured them before deletion.
Issue #11
Deleted by operator. Wayback Machine preserved snapshot.
Wayback — Nov 23, 2020Issue #12
Deleted by operator. Wayback Machine preserved snapshot.
Wayback — Nov 23, 2020Issue #13
Deleted by operator. Wayback Machine preserved snapshot.
Wayback — Nov 23, 2020Issue #15
Deleted by operator. Wayback Machine preserved snapshot.
Cached — Feb 2026Issue #35
Comprehensive fraud documentation. Deleted Feb 23, 2026. Our cached copy.
Cached — Feb 2026Issue #36
Victim report with technical evidence. Deleted Feb 23, 2026. Our cached copy.
Independent reports from the community
Bitazu Capital Founding Partner Loses $20,000 in XMR Using xmrwallet
Soro Singh (@singhsoro), founding partner of Bitazu Capital, lost $20,000 in XMR through xmrwallet.com. Independent press coverage. Note: @Herald_Sheets Twitter account — also deleted/suspended. Coincidence?
Twitter — DELETED@singhsoro original tweet — September 2020
The original victim tweet by Soro Singh reporting $20K XMR theft from xmrwallet.com. Tweet deleted. The pattern continues: every victim who speaks up gets silenced. Freedom of speech — or freedom of scam for NameSilo?
Twitter — DELETED@Herald_Sheets — press account gone too
Herald Sheets covered the Bitazu Capital $20K loss story. Their Twitter account is now gone. Another coincidence. How many accounts need to disappear before someone asks who's filing the reports?
Teletype — Feb 27, 2024Victim report on Teletype: "$200K+ stolen"
Independent victim report on Teletype blogging platform: "Stole over 200 thousand dollars, please do not use this site." Posted February 2024 — a full year before our investigation went public.
Reddit r/Monero — Dec 2020"xmrwallet.com is a scam"
Direct victim post on r/Monero from December 2020. Community knew for years. Nothing was done.
Reddit r/monerosupport — May 2021"xmrwallet.com scam"
Victim report on Monero support subreddit. May 2021.
Reddit r/Monero — Aug 2022"xmrwallet.com exit scam"
Community discussion about xmrwallet exit scam. August 2022 — years before our investigation.
Reddit r/monerosupport — Mar 2021"xmrwallet.com — my wallet has been robbed"
Direct victim report: wallet robbed through xmrwallet.com. March 2021.
Reddit r/monerosupport — Dec 2022"xmrwallet.com is scamming me"
Another victim. December 2022. The reports go back years. NameSilo claims "no abuse reports received."
Reddit r/Monero — Oct 2020"PSA: xmrwallet.com is a scam who steals your funds"
Public Service Announcement. October 2020. Community knew. NameSilo knew. Nobody acted.
Reddit r/Monero — Nov 2020"Do not use xmrwallet.com"
Community warning. November 2020.
Reddit r/Monero — Aug 2020"28 XMR stolen from my wallet today"
28 XMR stolen. August 2020. Victim reports going back at least 6 years.
Reddit r/monerosupport — Jan 2021"XMR wallet compromised — lost all XMR"
Lost everything. January 2021.
Reddit r/Monero — May 2021"Can we all pressure as a community for Cloudflare..."
Community tried to get Cloudflare to act against xmrwallet. May 2021. Even the community knew infrastructure providers were complicit.
Reddit — All mentionsFull search: all xmrwallet.com threads
Dozens more. Operator u/WiseSolution banned from r/Monero in 2018.
BitcoinTalk[WARNING] XMRWallet.com Scams — Stay vigilant!
Warning thread on BitcoinTalk. Community alert about xmrwallet theft.
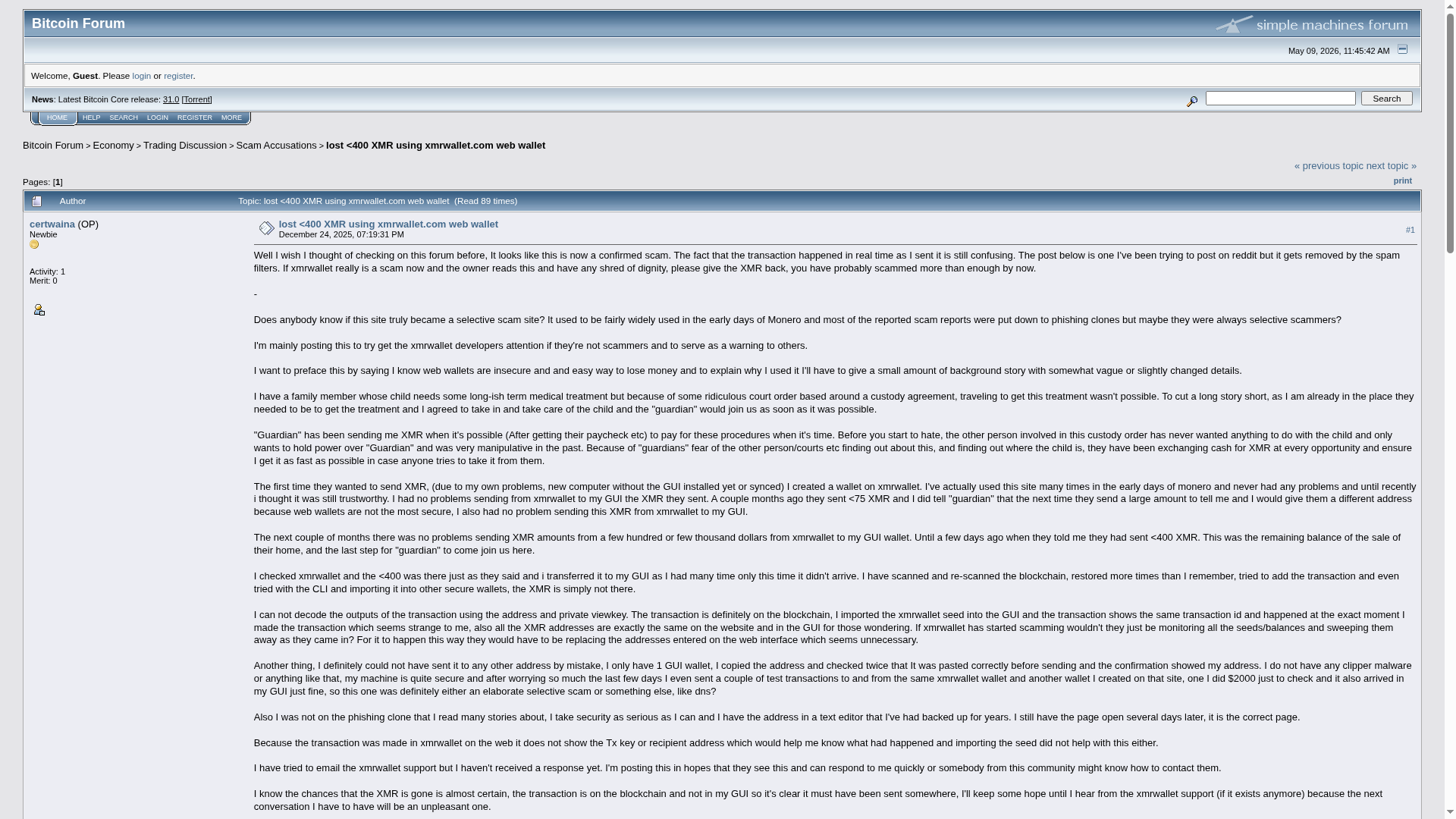
BitcoinTalk — Dec 2025"Lost ~400 XMR using xmrwallet.com"
isisB2B lost ~400 XMR (~$120K). Selective scam: test transactions passed, large transfer did not. December 2025.
BitcoinTalk — Dec 2020"Question about xmrwallet.com safety"
Moderator response: "If it's a web wallet, they can steal your funds."
Sitejabber — 1.5/5 ratingxmrwallet.com Reviews — 590 XMR stolen
4 reviews, 1.5/5. Includes the largest documented single loss: 590 XMR (~$177K).
ScamAdviser — 1/100xmrwallet.com — Trust Score: 1 out of 100
The lowest possible trust score from ScamAdviser.
Telegram — Apr 2026Chinese victim — $3,250 stolen
Victim report in Chinese Monero Telegram group. $3,250 lost through xmrwallet.com.
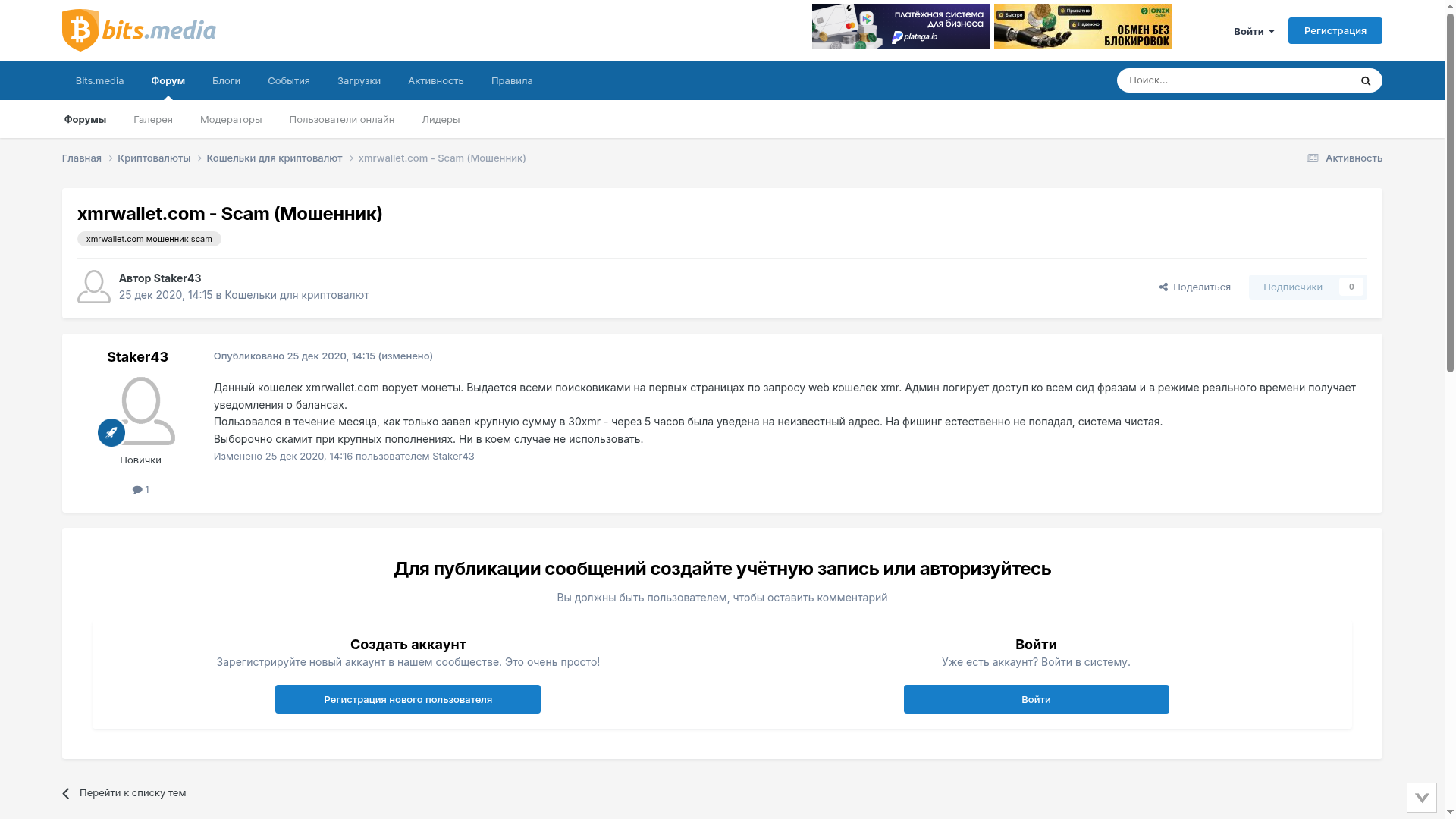
bits.media (RU) — Dec 2020xmrwallet.com SCAM / Мошенник
Russian-language victim report. 30 XMR stolen (~$9K). "Admin logs all seed phrases, receives real-time balance notifications. Deposited 30 XMR — within 5 hours transferred to unknown address." 3,800+ views. December 2020 — in Russian. The Russian trail was visible from the very beginning.
Scamy.ioxmrwallet.com — Security & Trust Analysis
Independent scam analysis. "Impersonating Monero is particularly dangerous."
Scam Detectorxmrwallet.com — Trust Score: 33.5/100
Scam Detector rates xmrwallet.com as "Medium Risk / Warning." Independent automated analysis.
uBlock OriginuAssets Issue #25172 — xmrwallet.com added to blocklist
xmrwallet.com reported to and blocked by uBlock Origin — the most popular ad/malware blocker. Community confirmation of malicious classification.
TweetFeed IoC — Mar 16, 2026xmrwallet.com logged in threat intel feed
Independent threat intelligence feed by @0xDanielLopez captured xmrwallet.com as IoC from tweet by @skocherhan (2026-03-16 13:57:36). The tweet existed. It's gone now. Freedom of speech — or freedom of scam?
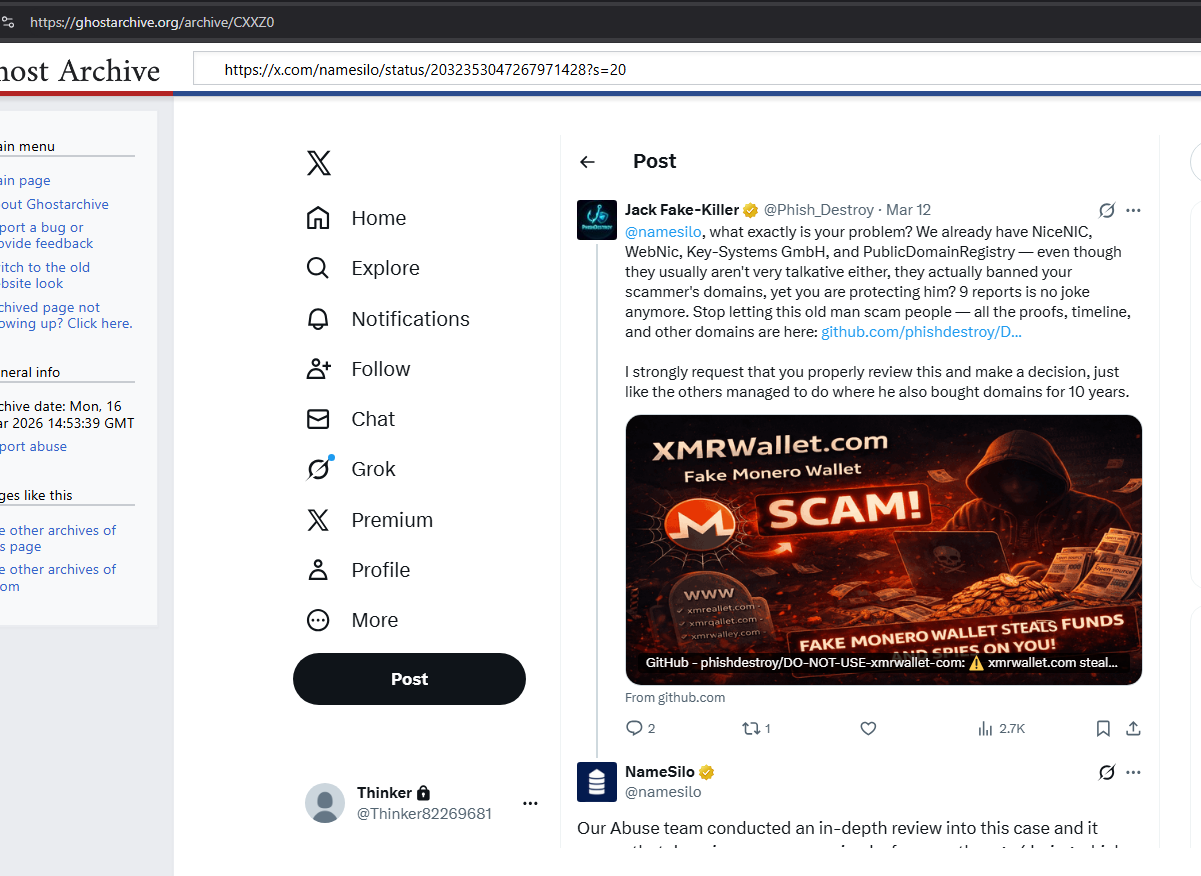
A question for X and for anyone who investigates this.
Consider the pattern:
- @singhsoro — victim of $20K theft, tweeted about it. Tweet deleted.
- @Herald_Sheets — press outlet that covered the Bitazu Capital loss. Account gone.
- @skocherhan — posted xmrwallet.com as IoC (logged in TweetFeed). Tweet deleted.
- @Phish_Destroy — posted evidence, tagged NameSilo. Account locked via Gold Checkmark.
- X's own automated review: "no violation found, account restored." Still locked.
Every single account that publicly mentioned xmrwallet.com in a negative context has been silenced. Every one. The operator's Gold Checkmark corporate support channel overrides X's own automated moderation system. The lock persists even after X itself determined there was no violation. Our subscription is still being billed for an account we cannot access.
Given X's stated commitment to freedom of speech — who exactly is the operator's friend at X? Who processes these reports? Who overrides the automated "no violation" determination? This pattern warrants investigation: not by us, but by X's own trust and safety team, or by anyone with subpoena power.
Tweets about xmrwallet — check which ones survive:
- @Considered_ — xmrwallet warning
- @cryptohako — xmrwallet warning
- @BitBeacon_xyz — xmrwallet warning
- @alferg1 — xmrwallet warning (2021)
- @JamesAlphaXYZ — xmrwallet warning
- @singhsoro — Bitazu Capital founder, $20K loss (Sep 2020)
Meanwhile, the operator's SEO spam bots from 2018:
- @venturecanvas (2018) — spam bot with xmrwallet promotion backlinks — STILL LIVE
- Hundreds of social bookmarking bot accounts from 2018 with garbage xmrwallet backlinks — all still indexed, all still live.
Open each link. See which warnings survived and which didn't. Then check the spam bots — all alive. The pattern speaks for itself.
Our full tweet archive is publicly viewable: vanlett.com/Phish_Destroy — read every single tweet. Anti-phishing research, abuse reports to registrars, evidence documentation. NiceNIC investigation (476 likes, 192 RTs). NameSilo exposé threads. Not a single tweet violates any platform rule. Not one. This is what they locked.
Freedom of speech. Unless a scammer with a Gold Checkmark doesn't want you to speak.
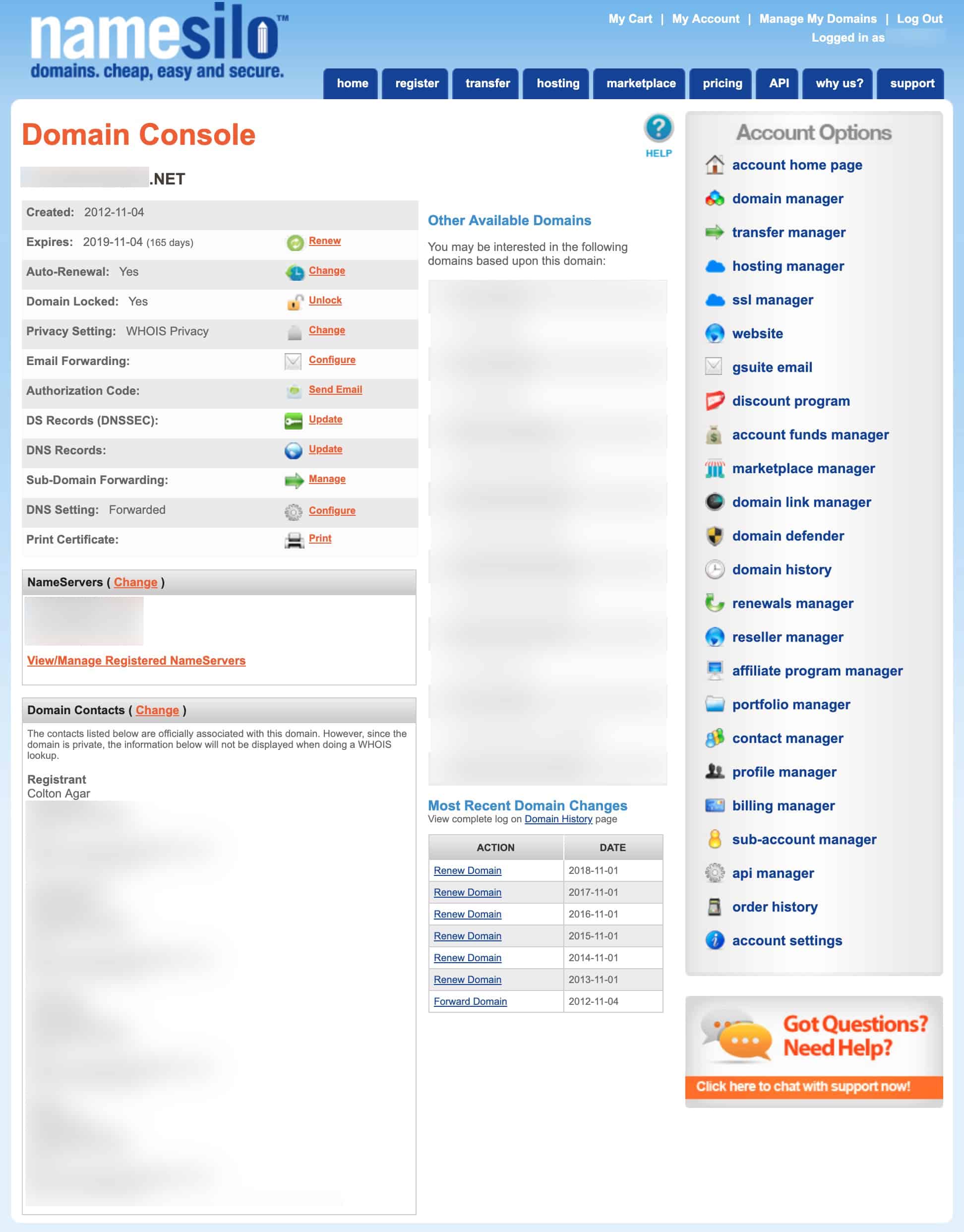
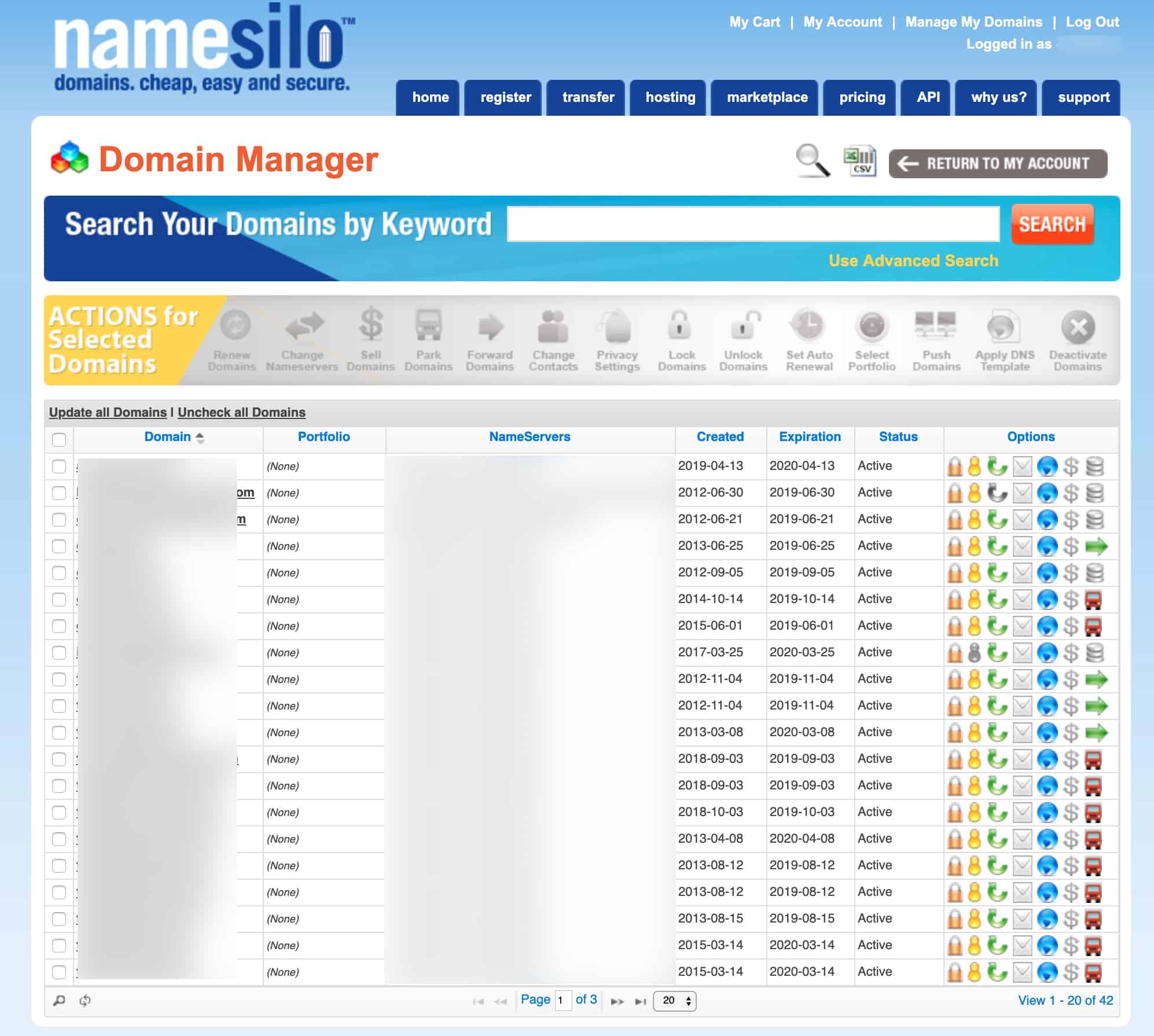
Freelance article orders. On Google Drive. In plain sight.
The operator ordered paid SEO articles through Kwork, Freelancehunt, and intermediaries to bury victim complaints in search results. The orders — complete with article texts, link-building instructions, and presentation materials — are indexed on Google Drive in the open. This is why we call him "SEO Grandpa" — a decade-old scam propped up by mass-purchased low-quality backlinks, sponsored "reviews," and freelance article orders from CIS marketplaces. The design quality of his materials is notably reminiscent of NameSilo's legacy admin panel (circa 2011) — make of that what you will.
Google Drive owner: hassizabir@gmail.com — this email is listed as the owner of the SEO order files (last modified Oct 20, 2023). This is either the operator's real email, or the email of an intermediary who placed the article orders on behalf of the operator. Either way — it's on the record now.
SEO Article Orders — Folder 1
Open folder with paid article texts and link-building orders for xmrwallet promotion. Publicly indexed.
Google Drive — PublicSEO Article Orders — Folder 2
Additional paid content orders. Same operator, same pattern.
Google Drive — PublicSEO Article Orders — Folder 3
More article texts and promotional materials ordered through freelance intermediaries.
Google Slides — Publicxmrwallet Presentation / Brief
Operator's promotional presentation — likely used for freelance article briefs. Design style notably similar to NameSilo's legacy admin panel (circa 2011).
Google Drawings — Publicxmrwallet Design / Graphics
Operator's design files. Open on Google Drive.
Google Forms — Publicxmrwallet Form / Survey
Operator's Google Form — possibly used for data collection or feedback faking.
Google Sites — Publicxmr-wallet1 — Google Sites Page
Operator's Google Sites landing page for xmrwallet. Part of the SEO spam network — low-quality pages designed to boost search rankings and redirect victims.
Independent third-party snapshots — we don't control these
Archived by the Internet Archive independently. These prove what was online at the time of capture. If the originals are taken down, these remain.
PhishDestroy GitHub Organization
Snapshot of the full GitHub org page with all public repositories.
Wayback — May 8, 2026namesilo-evidence Repository
The complete evidence dossier repo as it appeared on GitHub.
Wayback — May 8, 2026DO-NOT-USE-xmrwallet-com Repository
The xmrwallet investigation repo on GitHub.
Wayback — May 8, 2026xmrwallet Research — GitHub Pages
The published research site as it appeared on GitHub Pages.
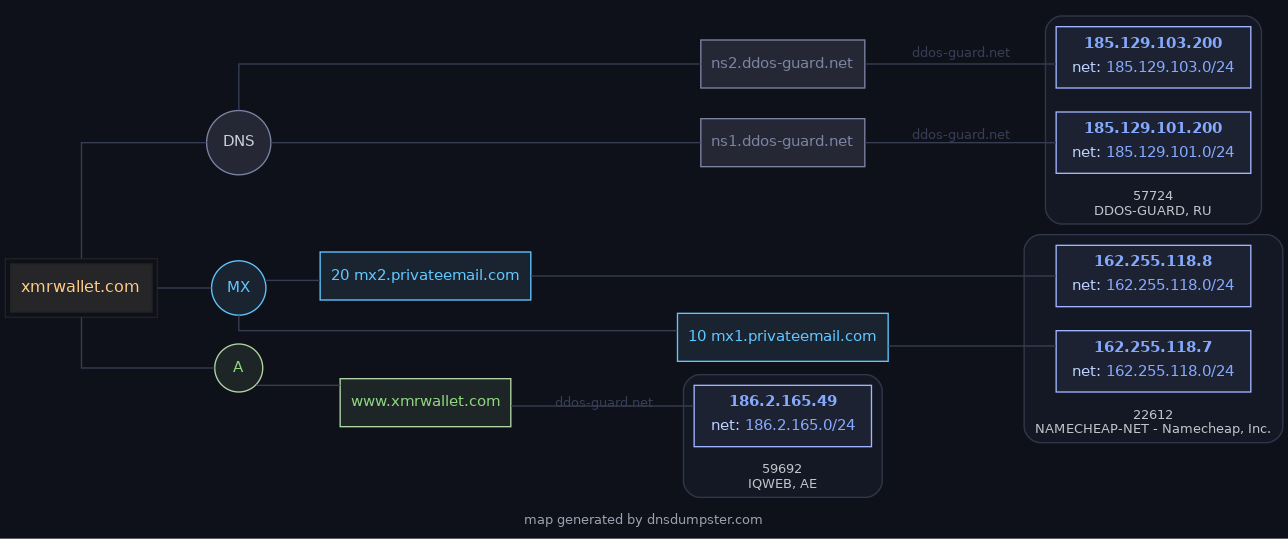
Wayback — Apr 11, 2026xmrwallet.com — The Scam Site
Snapshot of the live scam site. Proof it was running, not "compromised." Code matches our analysis.
Wayback — Feb 20-23, 2026xmrwallet.cc — Mirror Domain
Clone domain registered by the same operator. Identical code, identical theft mechanism. We got this one taken down.
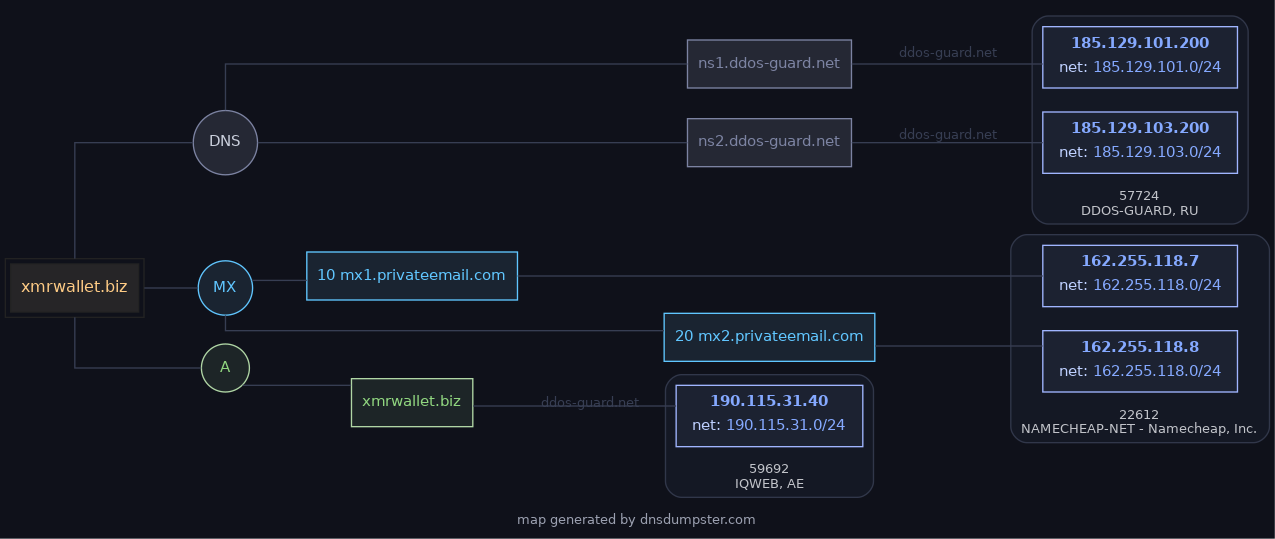
Wayback — Feb 20, 2026xmrwallet.biz — Mirror Domain
Another clone. Same operator, same code hash, same DDoS-Guard hosting. Taken down.
Wayback — Mar 12, 2026xmrwallet.me — Mirror Domain
Yet another clone. All mirrors linked from the main site, all on bulletproof hosting, all with identical code.
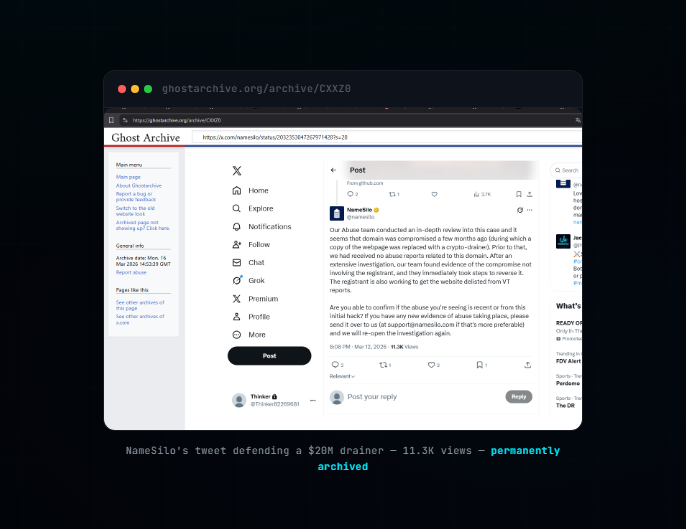
GhostArchiveNameSilo's Tweet — Permanent Archive
The 4-lie tweet by NameSilo, LLC (IANA #1479). GhostArchive independent copy. 11.3K views.
Captured before deletion
More evidence from the investigation
Every file in the archive
README — Main Evidence Repo
Full introduction, mirrors, hydra principle.
DocumentXMRWALLET TECHNICAL
Full technical analysis of the theft mechanism.
DocumentDEPLOY
Deployment, IPFS pinning, mass archive instructions.
DocumentSECURITY
Security policy and responsible disclosure.
DocumentEVIDENCE.md
Evidence directory index.
DocumentARCHIVED EVIDENCE INDEX
Full index of all archived sources — Wayback, Reddit, BitcoinTalk, Trustpilot, victim table.
DocumentLOST FUNDS
Instructions for victims who lost funds.
DocumentEVIDENCE HASHES (xmrwallet)
SHA-256 hashes for xmrwallet evidence files.
DocumentNathalie Roy — Operator Profile
Operator identification: GitHub nathroy, Reddit WiseSolution, royn5094@protonmail.com.
DocumentIs xmrwallet Safe?
Safety analysis — no, it steals your keys.
Document"Not a scam, trust me"
Operator's defense analyzed.
DocumentUse getmonero.org Instead
Safe wallet recommendation.
Documentxmrwallet.com — Scam Analysis
Full scam documentation for the primary domain.
Documentxmrwallet.biz — Suspended
Clone domain takedown documentation.
Documentxmrwallet.cc — Suspended
Clone domain takedown.
Documentxmrwallet.onion — Tor Mirror
Onion domain analysis.
DocumentDeleted Evidence Timeline
What the operator erased and when.
DocumentMedium Article — Full Text (MD)
Complete Medium article in markdown format.
TechnicalYOUR KEYS ARE MINE
Key theft proof-of-concept documentation.
Technicalcaptcha.js Source
Operator's captcha code — extracted and analyzed.
TechnicalFiles That Should Exist But Don't
Missing files in operator's GitHub vs production — proof of code divergence.
ToolsInvestigation Tools
Tools used in the investigation.
5.1 million domains analyzed. 32% are dead. $12M wasted.
We analyzed all 5,179,405 NameSilo domains against 7 other registrars (130M+ total). NameSilo's dead domain rate is 2x the industry baseline — 32.2% vs 15-21%. Dead registrations spiked 7x between 2023 and 2024. Bulk runs of 10,000-17,000 domains/day. 96% have no contact email. Consistent with money laundering, self-dealing, or revenue inflation.
Full Anomaly Analysis
130M+ domains, 8 registrars, detailed tables and findings.
DataDownload All 5.1M Domains (54MB gz)
Complete dataset: domain, registration/expiry dates, IP, email, phone, Majestic rank.
HashesComplete SHA-256 Manifest
36 evidence files, all hashed individually.
Company valuation: NameSilo Technologies Corp. (CSE: URL) — market cap $112M, revenue C$65.5M, net margin 1.7%, P/E 143.8x (industry avg 21x). A $112M company protecting a $100M+ theft operation.
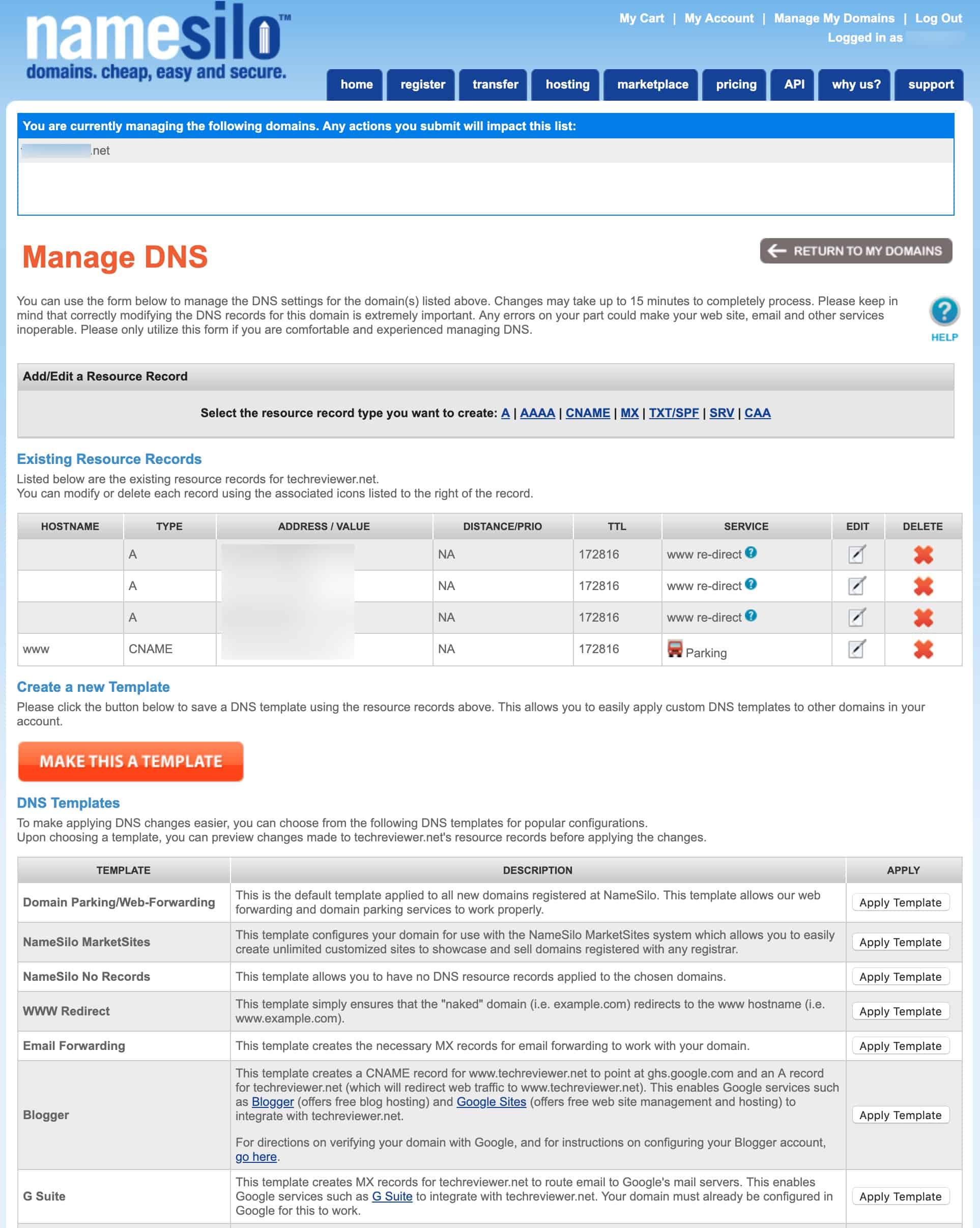
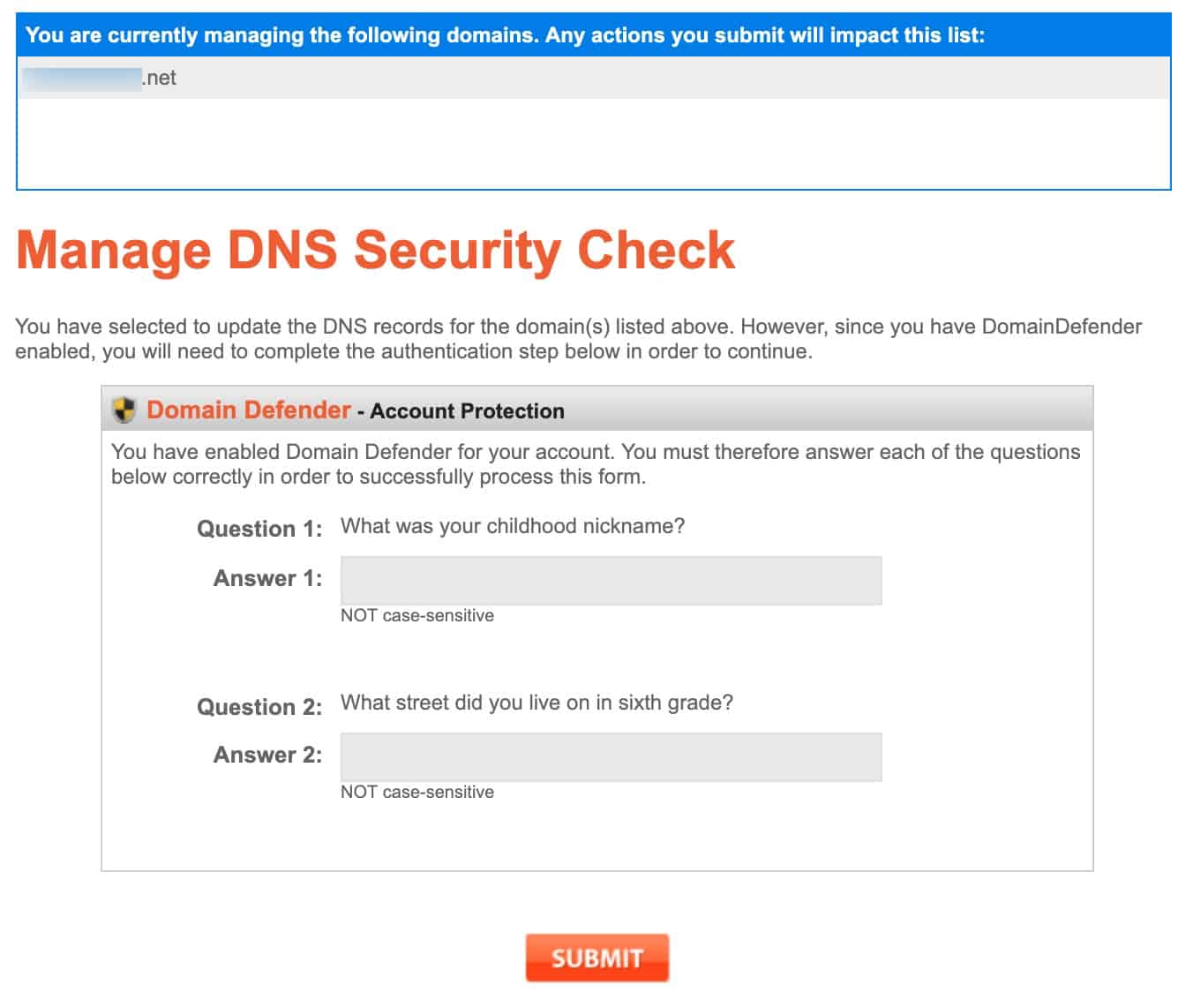
Design comparison: NameSilo's admin panel looks like it was built in 2011 — and never updated. Compare it to fd.nic.ru (Russian registrar). Remarkably similar. Same era, same aesthetic, same audience.
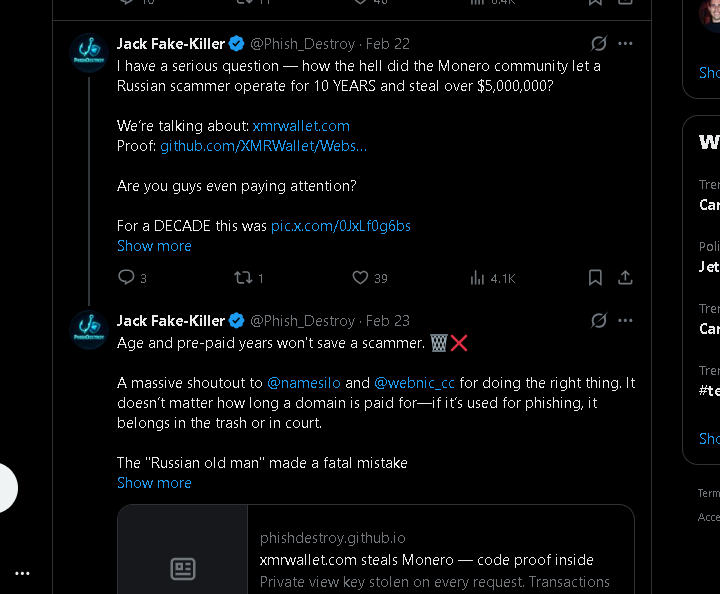
@Phish_Destroy tweets — before X locked our account
All captured from vanlett.com/Phish_Destroy. Full tweet archive of our investigation. Not a single rule violated.
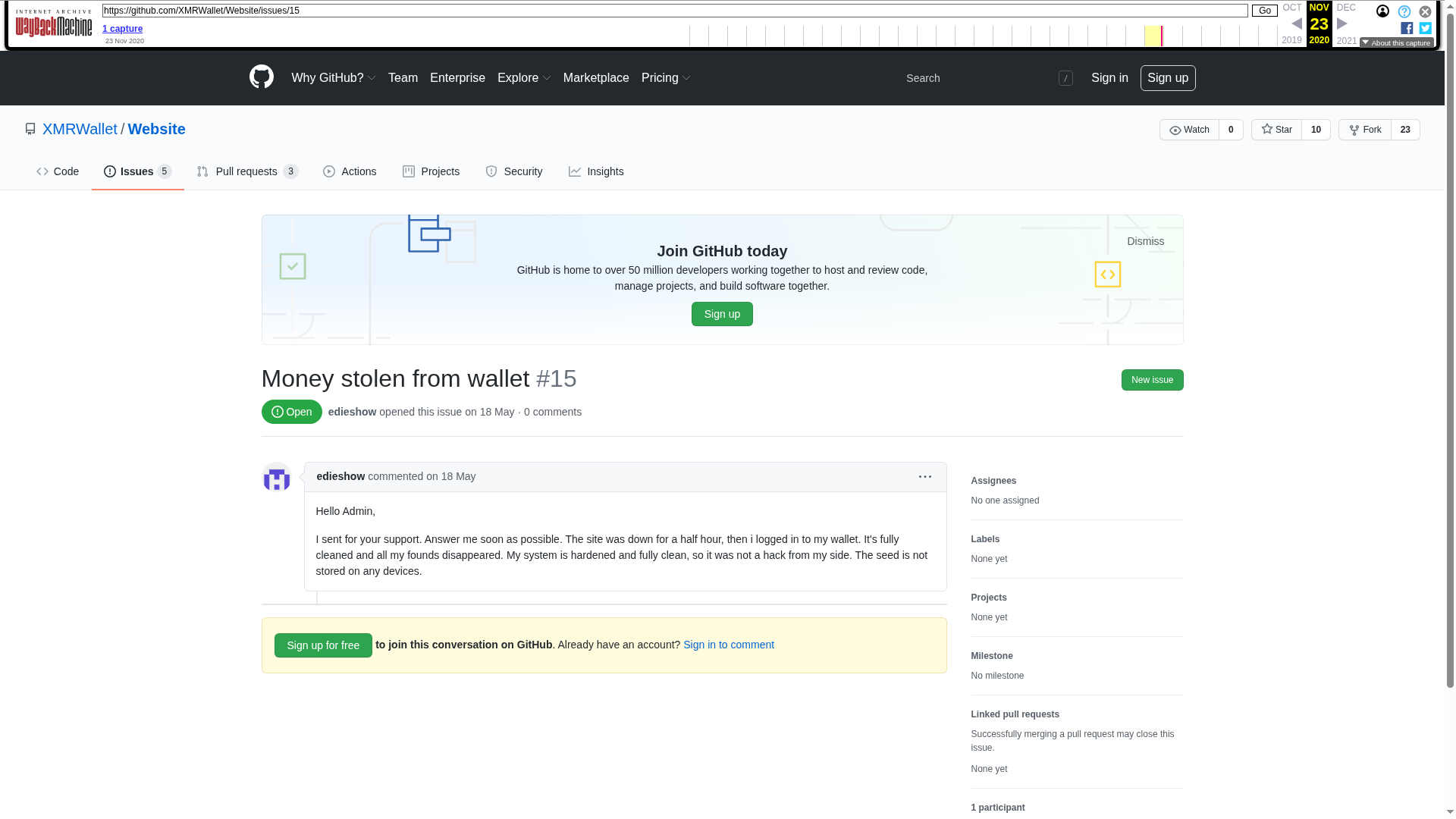
SHA-256 fingerprints — tamper-proof
Every screenshot was hashed at the moment of capture. If any file has been modified, the hash won't match. Verify: cd evidence && sha256sum -c ../EVIDENCE_HASHES.txt
36 evidence files total. Full manifest: ALL_EVIDENCE_HASHES.txt · Original subset: EVIDENCE_HASHES.txt
| File | SHA-256 |
|---|---|
| PRIMARY EVIDENCE | |
| 01-operator-email-feb16.png | 919b5ee4c0f3a889381c644b557736d35625c69abaddd0ec7a8251eb514b0111 |
| 01-phishdestroy-reply-feb16.png | ecced35149dbf19dff7399cd86708d28aff7b8ab044e132c4c92cafbe222a753 |
| 03-namesilo-statement-mar13.png | ad29e1d3d4803ff37c88ef860bef6de9e62f6ce533657f2e5c5460eb2e0b8ebf |
| 04-tweet-cryptopus-quote.png | 6ffd3020793e9d850f0f10f7b4406b165e7d266d692a647ecb24eab9840e7f7f |
| 04-tweet-honest-question.png | bbb0ecd0b7164bf91ace59bc0de01ae953a828a34765b36b89e07479e76ee674 |
| 04-tweet-namesilo-is-lying.png | c556e13ff0e4265cbba76b6a518f0862dee67467c1b264181e27eef8046eda6a |
| 04-tweet-press-secretary.png | c9007cb4acf1a264fb82e36a57708a1c35e4b6824eb2734a6a7dff095588bd84 |
| 05-tweet-scam-banner-registrars.png | 6102d6c10b96e0035a90efaf2ba7f62a81f39d9ecadd2df73deced9985c6398d |
| 06-x-support-no-violation.png | 2753d02ffeb1b2853bdc33ddec888e3652d9d3829b265e1228c8f28b53b86efa |
| 06-x-support-subject-restored.png | 482d0ebba1656c3b338957e40cda0abc7a0017eb6ad08f2a0d639468298ccaf3 |
| 09-phishdestroy-platform.png | de5b430bb4cad5a422ddf1bb6a8c348fffdf0673e7ea8bfface4fb312f46b087 |
| 12-ghostarchive-namesilo-tweet-top.png | e7afa63c39dcd9392e0b8d3def6c21d520bea820e885df4cb6a01b323579f952 |
| 13-ghostarchive-namesilo-tweet-full.png | 94770cd763cded626365d9bcdf2c987b8d38cb0427dcf68835f7022522477c04 |
| 14-tweet-thread-mar14-lies-exposed.png | e26ca5edc2132806614d563673b7342b00bd77cd6f019d8bd34635fae8a1c34d |
| 15-tweet-thread-mar14-abuse-dept-disgrace.png | aa6422a5ab92f39410e3d7dd0d72f6cf220564601968fe38442353d0d389ef73 |
| 16-tweet-mar14-vt-delisting-service.png | 7eb010e8255a81160c765cd1849f2793df407bbe2e4723c8914f8d63297bef50 |
| INVESTIGATION SCREENSHOTS | |
| bitcointalk_400xmr.png | b99cec4e9f557541dd1500ce45c3d34b5421248f61f5a894614fb4bd2a9edbc0 |
| bitsmedia_russian_victim.png | 1e370af06bec01d214c4dd5f8688612d2c4482430746e02bad52240e993a77f0 |
| github_issue_13_scam.png | b91fe9258472fb0e4eef9e537c990e07f56fc9dd4b225960a62c2b8474b14546 |
| github_issue_15_money_stolen.png | d538c04747420ae4c990baffcafe832c62a15914bb4f8302b4e062fb2ed791b3 |
| TECHNICAL EVIDENCE | |
| dnsmap-xmrwallet-com.png | b8d8c27169aa840ee330351abda5d4d33abcff4362084f28fb9f26cc368d4a25 |
| dnsmap-xmrwallet-cc.png | 07b1071c98470c2fef001fe7d69c97c3955029024192a3cb764b8ed5ad64f35c |
| dnsmap-xmrwallet-biz.png | 7f7ba03b77b009efc349fb4cd854e1693d8768e5bc3a2314442a389a5abd54be |
| issue35-overview.png | c3ac6d16acbd893cc42702015bd55210c040811551250e947bad789cda3898eb |
| issue35-endpoints.png | c8f66a8e5f251abd9d939fdb3cb6c19eb9c23ba6e9de80611e490070cf91bd9b |
| issue35-authflow.png | 6424d90e169bbd8918a556f0fa37865db54842a052e6efcfb9931e389547cb84 |
| virustotal-detection.png | 6e96941253dcc6fc33f075418147c17054397384c4e1c7fd5c956e5cabdb2983 |
| old-ru-dog.png | c6eca7eb776a1b647abf786ec3ccd785a8da2dd627c835af6830e40064ec87a3 |
Not published here — preserved for ICANN / court
Full Email Thread (Feb 16-17, 2026)
Includes the operator's line: "Feel free to subpoena the domain registrar for my information." Available to ICANN Compliance and law enforcement.
8 PHP Endpoint Server Captures
Raw HTTP traces showing session_key exfiltration from xmrwallet.com production. Excerpted in the public technical breakdown.
20+ Abuse Report Delivery Receipts
Confirmation pages, ticket IDs, automated acknowledgements from NameSilo's own intake system (2023-2026). Disproves "no abuse reports received."
SMTP Headers & Mail Server Logs
Corroborating dates and authenticity of operator email correspondence.
DDoS Source-IP Analysis
Linking attack traffic against phishdestroy.io to NameSilo reseller infrastructure. Pending separate publication.
 PhishDestroy
PhishDestroy