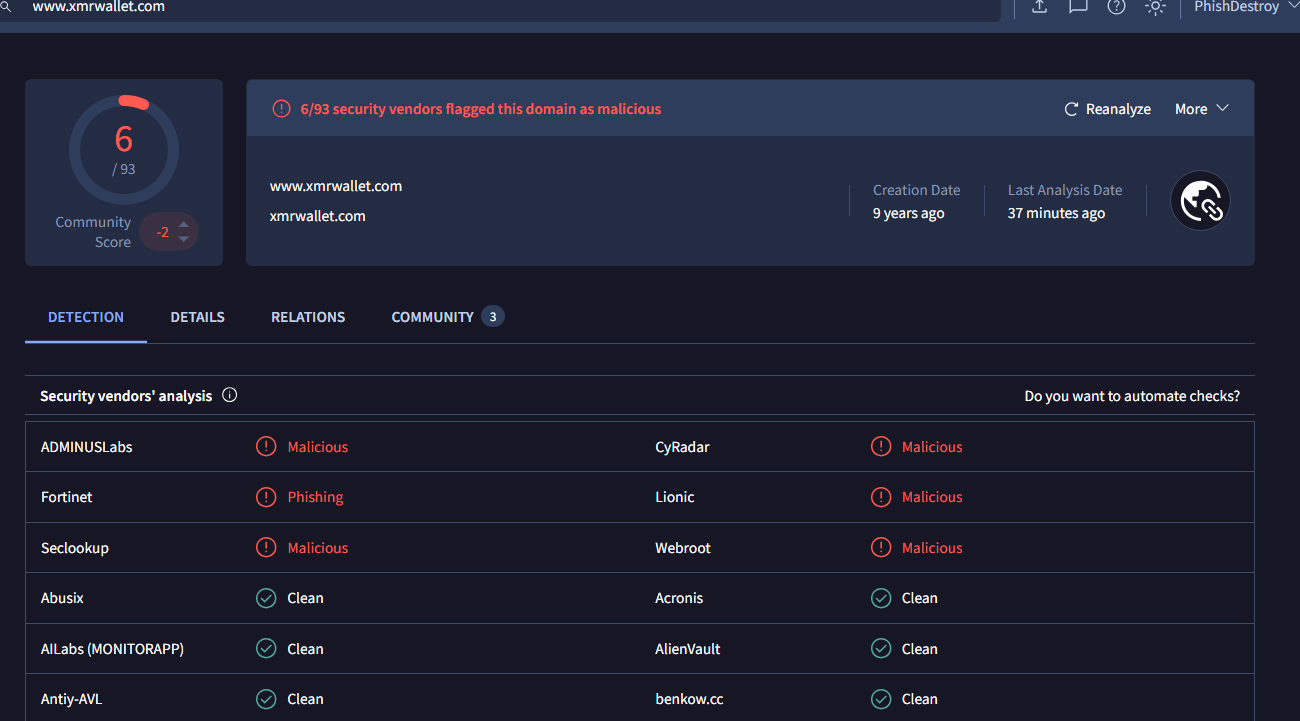
Independent investigation by PhishDestroy (volunteer anti-scam initiative). xmrwallet.com stole an estimated $100M+ in Monero over ~8 years via server-side transaction hijacking (estimate based on victim reports, site traffic analysis, and data from active EU law enforcement investigations). NameSilo (ICANN registrar, IANA #1479, Phoenix AZ) publicly defended the operator, issued statements contradicting the operator's own communications, and offered to clean VirusTotal detections. This archive: 61 SHA-256 verified screenshots, operator emails, ICANN filings, 130M+ domain analysis. Every claim backed. Nothing disproven.
All assessments represent independent analysis based on publicly available evidence. Not a court finding. No factual rebuttal received from any party mentioned. Full evidence archive · Investor summary
11 Evidence Points Linking NameSilo to xmrwallet.com
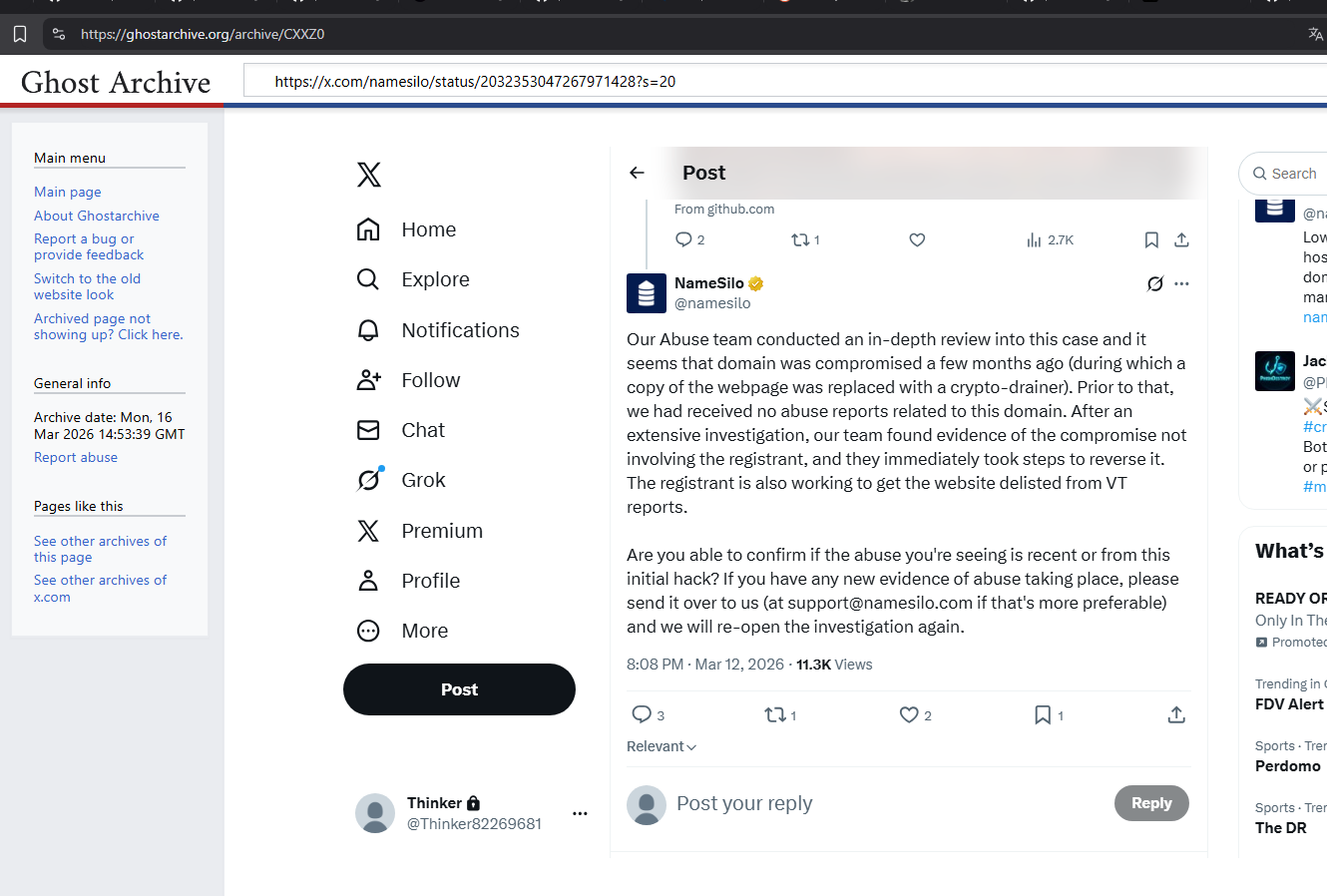
xmrwallet operator wrote: "Feel free to subpoena the domain registrar." Then NameSilo issued a statement claiming domain "compromise" — inconsistent with the operator's own emails — and offered to remove VirusTotal detections. No registrar in our career (500K+ takedowns) has ever done this.
We tested 10 registrars + 10 wallets (Google + Bing, same methodology). NameSilo: 0 tech media coverage (only alongside NiceNIC). xmrwallet.com: only wallet with crypto spam, 0 Wikipedia, 0 tech media. Both use PR Newswire/Cision (3 + 12 releases) — no other registrar-wallet pair shares this platform. xmrwallet release published 1 day before NameSilo's. Full SERP data for all 20 entities available.
xmrwallet: Kwork SEO articles + Trustpilot bots. NameSilo: $50K+ Forbes advertorial + 129 reviews deleted in 4 months. Same strategy, different budget.
NameSilo bought ShortDot TLDs, dead registrations spiked 615%. 81.5% of all NameSilo domains resolve to nothing. Namecheap: 32.2%. Pattern consistent with crypto→domain laundering.
10 registrars tested: NameSilo = 0 tech media (only alongside NiceNIC). 10 wallets tested (searched as domains, e.g. "xmrwallet.com"): xmrwallet.com = only one with crypto spam, 0 Wikipedia, 0 tech media. Gemini AI confirmed independently.
31+ reports filed through NameSilo portal (receipts preserved). Reddit/BitcoinTalk reports since 2018. NameSilo's public response: "we received no abuse reports." Four statements contradicted by evidence in one tweet — all debunked with screenshots.
Trustpilot (deletable): NameSilo 4.7/5. SmartCustomer (not deletable): 1.8/5, 76% one-star. xmrwallet: ScamAdviser 1/100, MyWOT 1/100. Where they can't delete — catastrophic ratings.
NameSilo's own PR: "one of the first companies to accept bitcoin." No identity verification for domain purchases. Stolen XMR → BTC → bulk domain registrations → "revenue."
xmrwallet "farewell letter" (May 5, 2026): admits closure was forced by this investigation. Contains 2 statements contradicted by technical evidence. The letter itself is evidence.
Operator filed DMCA takedown with Google to remove a business profile calling xmrwallet a scam (Lumen Database #50915938). In the filing, claims xmrwallet is a "legitimate business" and cites US defamation law — but files from Russia, not Canada. If xmrwallet is a volunteer open-source project with no revenue — what "business" is being harmed? And why file from Russia?
Semrush OSINT: xmrwallet operates 50+ blogspot PBN domains (automated naming: asunm/asuk/asnet series), Google Sites spam (account "abrahambrantley"), satellite site bestmonerowallet.com, listed in darkweb directory CONWAY, backlinks purchased via Telegram @darksidelinks. 70-80% of all backlinks are spam. Real organic traffic: ~640/mo. PBN campaign peak (Sep 2025) correlates directly with traffic spike.
Strongest Evidence of Connection
10 Years of Identical Suppression — Across Every Platform
Both NameSilo and xmrwallet.com have been systematically erasing negative content for a decade — using the same methods, on the same platforms, with the same results. This is not normal corporate reputation management. The scale and consistency of this suppression across 9+ platforms is highly improbable for two unrelated entities and strongly suggests coordination.
9 out of 9 platforms. Identical tactics. For 10 years.
For context: maintaining this level of suppression across 9+ platforms for even one company requires significant effort and coordination. Doing it identically for two supposedly unrelated companies — one a registrar, one a wallet — is not explained by coincidence. Google one query for each and you will see: zero negative results. For a company with 1.8/5 on SmartCustomer and a wallet flagged 1/100 on ScamAdviser — that doesn't happen naturally.
Why this suppression pattern is prosecutable evidence:
1. Every deletion is logged. Trustpilot, Google, Bing, GitHub, YouTube, Twitter/X — all platforms maintain internal logs of content removals, DMCA requests, abuse reports, and the accounts that filed them. These logs are subpoenaable. A single subpoena to Trustpilot requesting deletion logs for both NameSilo and xmrwallet.com will show who requested each deletion, from which IP, through which account, and when.
2. This is not common. Systematic suppression across 9+ platforms for 10+ years is extremely rare. Most companies deal with negative reviews on 1-2 platforms. Most never file DMCA takedowns against researchers. The scale and consistency of this operation creates a unique forensic fingerprint — one that will match between the two entities when logs are compared.
3. Manufactured reputation — statistically impossible. xmrwallet had a higher Trustpilot rating than Binance and Coinbase — the world's largest crypto exchanges. NameSilo has the highest Trustpilot score among all registrars. Yet on platforms where they cannot delete reviews: SmartCustomer 1.8/5 (76% one-star), ScamAdviser 1/100, MyWOT 1/100. A company cannot simultaneously be the best-rated and the worst-rated in its industry unless one set of ratings is manufactured.
4. Deindexing proves coordination. SiteJabber (SmartCustomer) pages for both entities were deindexed from Google. This requires filing specific removal requests. Who filed them? The answer is in Google's logs. If the same entity or method was used for both — that is direct proof of coordination.
5. PR Newswire is the shared mouthpiece. NameSilo uses PR Newswire to write about itself, then cites these releases as "media coverage" in investor filings (CSE: URL). xmrwallet used the same platform to publish articles about Tor privacy — legitimizing a phishing wallet. The same PR platform, the same strategy of manufacturing credibility from paid content. One release published 1 day before the other.
The domain question that ends this:
We have a full year of expired NameSilo domains — domains that were purchased, never activated, never used for anything, and allowed to expire. From the moment of purchase to the moment of death: zero activity. No DNS. No website. No email. No purpose.
Ask one question: who buys thousands of domains, pays for them (often with Bitcoin), and never uses them? Not once. Not accidentally. Systematically, 10,000-17,000 per day, for years. There is no legitimate business explanation. Domain speculators activate domains. SEO farms build sites. Even parking services require DNS. These domains have nothing.
Subpoena the payment records for these domains. Ask NameSilo: where did the money come from? If they cannot answer — or if the answer leads to Bitcoin wallets traceable to XMR-BTC swaps — you have your case.
Evidence we hold but don't publish yet:
We have screenshots from victims whose Trustpilot reviews were deleted — many with verified purchase badges. We are not publishing all of them at this time. If NameSilo or Trustpilot denies deleting reviews, we can produce the evidence and the victims who wrote them. This is a deliberate strategy: we want them to deny it on record first.
On SmartCustomer — where they can't delete — read the real reviews. Phishing domains not removed. Abuse reports ignored. Domains stolen via "transfers." This is not our opinion. These are their own customers, verified, with purchase history.
DMCA from Russia: "Our legitimate business"
On February 12, 2025, a DMCA takedown request was filed to Google demanding removal of a Google Maps listing that warned users about xmrwallet.com. The request is archived in the Lumen Database (Notice #50915938).
The sender’s country: RU 🇷🇺. The request states: “The creator of this listing is not affiliated with our company and is promoting a false narrative, claiming that XMRWallet.com is a scam. This claim is entirely untrue and baseless.”
The sender calls xmrwallet.com a “legitimate business” and demands protection from “harm to a business’s reputation.”
Three things this proves:
1. Russian origin. The DMCA sender is from Russia (RU). The “volunteer developer Nathalie Roy from Canada” apparently has Russian associates filing legal requests on behalf of “our company.” A volunteer open-source project does not have a Russian legal representative calling it “our business.”
2. It’s a business, not a volunteer project. The sender explicitly calls xmrwallet.com a “business” and invokes business reputation law. The operator’s own GitHub describes it as a free, open-source, volunteer project with no revenue. Which is it? A volunteer project has no “business reputation” to protect. A phishing operation stealing millions in Monero — that is a business. And now they said it themselves.
3. Suppression pattern continues. This is the same playbook: anyone who warns victims gets a legal threat. Google Maps listing removed. Trustpilot reviews deleted. Medium articles deindexed. Twitter accounts suspended. The “harm” they want to prevent is not reputational — it’s operational. Every warning that reaches users costs them victims. Every victim they lose is revenue lost. That’s why a Russian sender files US DMCA requests about a “Canadian volunteer project.”
Every step documented before it happened. Established operator tactics identified and anticipated.
No opinions. No editorializing. Just data collected with the same methodology for all entities — and independently analyzed by Gemini 2.5 Flash AI.
SERP Profile — Registrars
Google + Bing, top 30 results, 10 registrars compared. Key metric: Tech Media coverage (independent articles).
NameSilo — zero independent tech coverage in 44 results. Only registrar with 0 alongside NiceNIC.
SERP Profile — Wallets
Same methodology, 10 crypto wallets. Key metric: Crypto Spam (paid/manufactured articles).
xmrwallet is the only wallet out of 10 with crypto spam in search results. Also lowest own-domain presence (6.8%). Query: "xmrwallet.com" (domain, not generic term).
Reputation — Where They Can vs Can't Delete Reviews
Pattern: Where companies can delete reviews (Trustpilot) — high ratings. Where they can't — catastrophic. Both entities. Same pattern.
Gemini 2.5 Flash — Independent AI Conclusion
"xmrwallet: The presence of crypto_spam (4.5%) is a direct indicator of reliance on manufactured or low-quality paid content. Its low own-domain presence (6.8%) further supports a less organic and independently validated profile."
"xmrwallet is the only wallet with crypto_spam. The term crypto_spam itself implies manufactured or low-quality content rather than organic coverage."
Zero-shot analysis. No leading prompts. Raw SERP data fed to AI. Full report: serp-gemini-report.md · Raw data: serp-full-analysis.json
Full SERP tables (20 entities), methodology details, and PR Newswire analysis are in the Evidence section below.
Every claim is backed by source material. Every screenshot is SHA-256 fingerprinted. Every external link has at least one immutable archive copy.
"N.R." (royn5094@protonmail.com) → abuse@phishdestroy.io, Feb 16. Defends site, demands removal. Never claims compromise.
Screenshot →NameSilo's Mar 13 tweet: 4 sentences, 4 contradictions. Each proven false with operator's own emails + code hashes.
Full analysis →SHA-256 before and after "compromise." Code never changed. IP never changed. NameSilo fabricated it.
Proofs →8 PHP endpoints. session_key = base64(address + viewkey). raw_tx = 0. Server builds its own TX.
View →16 primary + 19 additional + 26 tweets. Emails, victim reports, DNS maps, VirusTotal, GitHub issues, operator taunts. All SHA-256 fingerprinted. Court-usable.
View all →xmrwallet.com, .cc, .biz, .me archived. NameSilo tweet archived. GitHub repos archived. Independent copies.
View all →"We had received no abuse reports" — the internet disagrees.
NameSilo claims in their March 13, 2026 tweet that they had never received abuse reports about xmrwallet.com prior to our contact. This is verifiably false. Public posts on BitcoinTalk (2021) and Reddit (as early as 2018) explicitly discuss filing reports with NameSilo about this domain. These posts are still indexed. They were not hidden, not encrypted, not on the dark web — they were on the two largest crypto forums on the internet. NameSilo's abuse team would have to be either spectacularly incompetent or deliberately lying. We know which one it is.
For regulators: Is there an authority that can audit a registrar's abuse ticket system? Subpoena NameSilo's internal records. Compare the number of reports they actually received vs. what they claimed publicly. The gap between those numbers is measurable, provable, and potentially criminal. They spent enormous effort scrubbing the internet of evidence against xmrwallet — but they couldn't scrub BitcoinTalk and Reddit.
A note about Monero and the victims you can't identify.
Monero is private. That's the point. It means victims can't trace their stolen funds. But it also means something else: the operator doesn't know who he stole from.
Over nearly a decade and an estimated $100M+, the xmrwallet operator drained wallets indiscriminately. Every user who deposited Monero and clicked "send" had their transaction hijacked. The operator has no idea who those people were. Some were retail crypto users. Some were investors. Some were researchers. And some were people with the resources and motivation to pursue justice.
We are researchers. We publish evidence and move on. But not everyone who lost money on xmrwallet.com will respond by writing a report. The operator should consider this. NameSilo should consider this. You helped protect a thief who stole from people he cannot identify, in amounts he cannot calculate, in a currency he cannot trace. Some of those people may pursue legal remedies the operator has not anticipated.
View full bot analysis — 68+ live bot posts vs ~100+ deleted victim warnings →
Warning tweets about xmrwallet — check which survived:
SEO spam bots from 2018 — all still alive:
We estimate 100–200 tweets total have been deleted across all accounts that ever mentioned xmrwallet.com truthfully — our reports from @Phish_Destroy, independent researchers, victim complaints, security warnings. All gone. Meanwhile, the operator purchased a Kwork service: "social media link blast — Twitter 50 posts, 500 rubles" (~$5 USD). He bought multiple packages. Hundreds of spam bot posts promoting xmrwallet.com from 2018 — every single one still live. Not one removed.
X/Twitter's actions demonstrate a clear double standard: bot spam purchased for 500 rubles on a Russian freelance marketplace remains untouched, while victim reports about a $100M+ theft and researchers with SHA-256 verified evidence get locked. X/Twitter should investigate which employees are processing these reports and why.
And to be clear: on April 3, 2026, we paid $200 for X Gold verification. The ban came immediately. X stated the payment would be refunded — neither the ban was lifted nor the refund issued. $200 for a Gold Checkmark we never got to use — but NameSilo's Gold Checkmark works just fine for filing reports against us. We submitted 5+ data export requests across 3-4 accounts — all denied or ignored. Those accounts contain approximately 200,000 tweets combined, each of which is potential evidence of someone's crime — a phishing site, a registrar's negligence, a victim's report. X is not just silencing us. X is withholding evidence of mass cybercrime and charging us for the privilege.
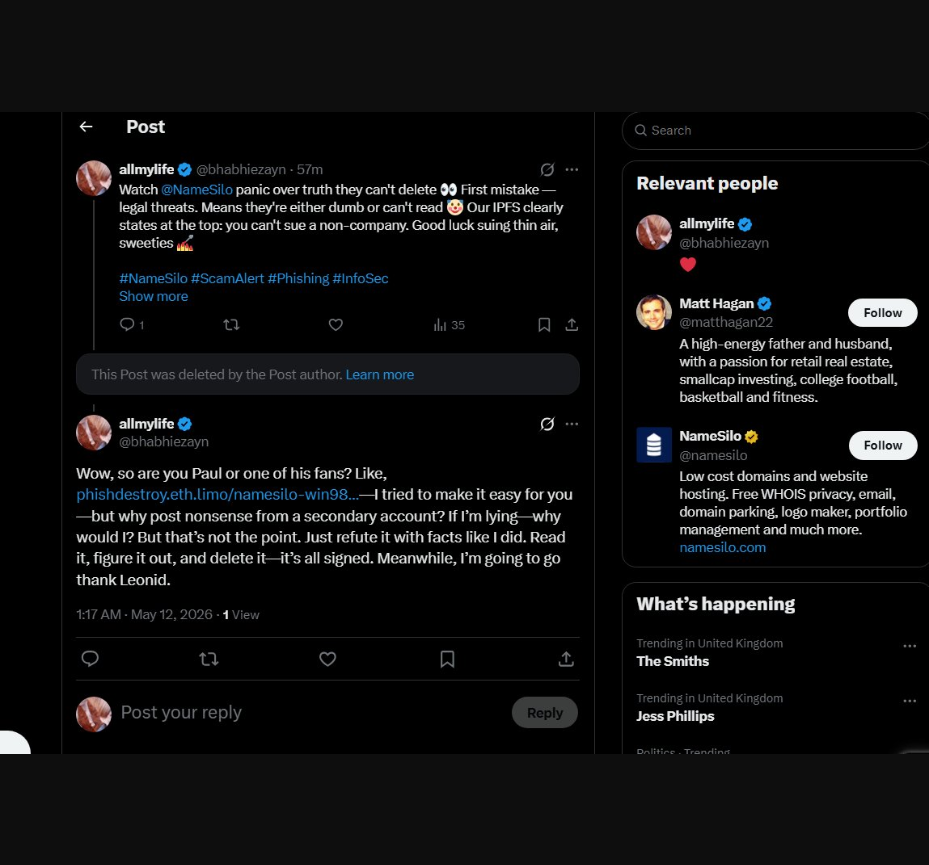
But NameSilo also managed to get some of our most inconvenient posts removed. For investigators: this is not a problem — request the deletion logs, verify who filed the reports, check the timestamps. Every removal is traceable. Every moderator action has a paper trail. The posts NameSilo wanted gone the most are exactly the ones that matter.
After everything that happened — after the public exposé with 11K views, after 4 statements vs evidence with the operator's own emails, after ICANN filing, after law enforcement referral, after 3 other registrars suspending the same domains on the same evidence — the site is still live.
Ask yourself: what legitimate registrar would endure this level of public humiliation and regulatory risk for one client? What company would publicly commit to removing VirusTotal detections for a known drainer? What abuse department would fabricate a "compromise" story that contradicts the operator's own emails?
None — unless they own it or profit from it directly.
NameSilo, LLC (IANA #1479) is either the owner of xmrwallet.com, or a direct financial partner in a $100M+ theft operation. In our assessment, no other explanation accounts for their behavior. A client-registrar relationship does not produce this level of protection.
And there is a Russian intelligence trail here.
The infrastructure patterns, the operational security methodology, the CIS-marketplace freelance orders, the DDoS-Guard hosting, the suppression playbook — this is not a solo Canadian "volunteer" running a hobby project. This is an operation with institutional backing. The Russian connection is obvious to anyone who has worked in CIS cybercrime investigation. We have evidence. Investigators will receive it upon request.
A note to NameSilo — we are not playing your games
We see the xmrwallet.com domain transfer away from NameSilo. Do they think another registrar will inherit their problems? That moving the domain erases 10 years of complicity? We already know how NameSilo operates — they spend 85% of their Google Ads budget bidding on competitors’ names (GoDaddy, Namecheap), and their staff replies to tweets where users tag other registrars. Poaching customers by name while hiding behind a Russian outsourcing team — this is how they do business.
Transferring xmrwallet.com will not work. Every file in this archive is SHA-256 signed with timestamps. Every domain snapshot, every WHOIS record, every abuse report response, every dead domain count — captured and hashed before they started moving. Their actions now are not cleanup — they are additional evidence of consciousness of guilt.
Even if they transfer xmrwallet.com to another registrar. Even if they give away every laundering domain for free. Even if they activate every dead domain with a parking page. Our questions remain the same. Our files remain the same. Our hashes remain the same.
Who bought 1.67 million domains that were never used? Where did the money come from? Why did you publicly defend a $100M+ theft operation? Why does your DevOps engineer have a financial pyramid on his resume? These questions don’t go away because you moved a domain. They get louder.
A message to every moderator, every trust & safety employee, every platform admin who deleted a victim's post, locked an account, or removed a warning about xmrwallet.com:
We ask you to publicly explain why you did it. What rule was broken? What policy was violated? You deleted truth, silenced victims, aided $100M+ theft. That is not moderation — that is complicity. Every deletion is logged. Every removed review is traceable. Every locked account has a paper trail. Investigators can and will request those records.
To ICANN Contractual Compliance:
We submitted the full case file on March 18, 2026. Every screenshot. Every email. Every hash. Every lie debunked. Every victim documented. Every suppression attempt logged. You have it all. NameSilo, LLC (IANA #1479) — your accredited registrar — is actively protecting a Russian-linked scam operation that stole $100M+. The site is still live. The domain is still active. The operator posted a farewell letter and the site is STILL UP. Are you comfortable with this? Is this what ICANN accreditation means? A registrar can publicly lie, help a scammer remove security detections, use paid platform access to silence researchers — and keep their accreditation? We are waiting for your answer. The victims are waiting. The evidence is public. The world is watching.
A message from a victim — and a question about ICANN accreditation:
One of the victims contacted NameSilo and was told something along the lines of their "ICANN license" protecting them. Let's be absolutely clear about what ICANN accreditation is and what it is not:
ICANN accreditation is a license to register domain names. It is not a license to commit fraud. It is not a license to cover up money laundering. It is not a license to protect scam operators. It is not a shield against criminal prosecution. It is not a supreme court ruling that permits NameSilo to help a thief steal $100 million. It does not grant immunity from law enforcement, civil lawsuits, or regulatory action.
An ICANN-accredited registrar is more accountable, not less. The RAA (Registrar Accreditation Agreement) explicitly requires abuse handling. NameSilo signed this agreement. NameSilo violates it every day that xmrwallet.com remains active.
To victims: do not let anyone tell you that "ICANN accreditation" protects a registrar from consequences. It doesn't. Sue them. File criminal complaints. Report to your national cybercrime unit. Report to the Arizona Attorney General. NameSilo is a US company in Phoenix, AZ. They are subject to US law, regardless of what ICANN accreditation they hold. A driver's license doesn't protect you from a murder charge.
The ICANN Accreditation Theater
Here is something that genuinely baffles us. In every single abuse response, in every reply to every complaint, NameSilo cites their ICANN accreditation. Every time. Like a mantra. Like a prayer. Like a magic spell that makes abuse reports disappear.
"As an ICANN-accredited registrar..." — yes, and? Do you understand how absurd this sounds to anyone who works in this industry? Let us translate this into terms everyone can understand:
ICANN accreditation is a commercial license. You pay a deposit. You fill out paperwork. You agree to follow the RAA (Registrar Accreditation Agreement). That's it. It does not make you a regulator. It does not make you untouchable. It is not a fund that covers the actions of fraudsters you protect. It is not a judicial shield. An SSL certificate on a phishing site doesn't make it legitimate — phishers buy SSL certificates every day, including the expensive EV ones. A Cloudflare account doesn't make you safe — every malware distributor has one. And ICANN accreditation doesn't make you honest — it just means you paid the fee.
And it gets better. NameSilo doesn't just cite ICANN accreditation in abuse responses — they put it in their financial filings. In the Q3 2025 earnings release filed on SEDAR+ (November 28, 2025), the company describes itself as: "As an accredited ICANN registrar, Namesilo is one of the fastest-growing domain registrars in the world." This is in an earnings report. For investors. On a securities filing platform. Instead of disclosing that 81.5% of their "domains under management" are phantom registrations with zero traffic, they lead with ICANN accreditation. It's not just a reflex at this point — it's a securities disclosure strategy. Wrap the phantom numbers in the ICANN badge and hope nobody checks. We checked. Source: Stockwatch →
By the time an ICANN complaint is reviewed, processed, and acted upon, the scam domain has already expired, the money is gone, and the victims have given up. The process is slow by design. Filing an ICANN complaint is like calling the fire department after the building has burned down, been demolished, and turned into a parking lot. This is not a check. This is not oversight. This is theater.
Case in point: Trustname.com (IANA #4318) — an ICANN-accredited registrar. "Fastest growing independent registrar." Our investigation found: Estonian tax filings showing €120 in revenue, one employee, negative equity, and a company deletion notice. Both owners are Belarusian. The registrar openly markets bulletproof hosting, serves scam casinos, 18+ content, illegal pharmacies, and fraud operations. ICANN-accredited. Does that accreditation make them legitimate? Does it protect the victims of the scam casinos they host? Of course not. It just means they filled out the same form NameSilo did.
Maybe we should buy ICANN accreditation too. Then we can write it everywhere:
"Hi, this is PhishDestroy. ACCREDITED BY ICANN, CREDENTIALED BY DOMAIN CCK, PAYMENT PROCESSED BY A REGISTRAR AND A HOSTING PROVIDER."
Sounds impressive, right? Sounds like it means something? It doesn't. And when NameSilo writes it in every response to every abuse report they ignore — it doesn't mean anything either. Except that they think it does. And that delusion is part of the problem.
RAA Section 3.18 — the clause NameSilo pretends doesn't exist.
The Registrar Accreditation Agreement — the document NameSilo signed — includes Section 3.18, which explicitly requires registrars to investigate and respond to abuse reports. Not ignore them. Not delete them. Not fabricate cover stories. Not offer to clean VirusTotal detections for the reported domain. Investigate. Respond. Act. We started citing RAA 3.18 in every single report we file. NameSilo's response? The same ICANN accreditation mantra. They invoke the very authority whose rules they violate — in the same sentence where they violate them. It would be comedy if people weren't losing millions.
Maybe NameSilo has a special ICANN — a private edition, issued by the grandfathers from Lubyanka? A bespoke accreditation where 3.18 reads: "The registrar shall ignore all abuse reports, help the scammer clean his record, and cite this accreditation as justification." Because that's how they behave. They use the ICANN badge the way a corrupt cop uses a police badge — not to enforce the law, but to break it with impunity.
ICANN is not the police. It's the DMV.
ICANN was created in 1998 when the internet was an academic project, not a battlefield. Its mandate is technical stability — making sure .com resolves the same in Tokyo, Berlin, and Moscow. It coordinates the root DNS zone, distributes IP addresses (IANA), and maintains protocol standards. Without ICANN, the internet fragments. That's why it exists. Not to police fraud. Not to protect victims. Not to investigate money laundering.
The RAA is a contract, not a law. Violating RAA 3.18 is breach of contract, not a crime. ICANN's ultimate sanction — revoking accreditation — takes years, creates precedent they fear, and risks thousands of domains in limbo. They won't do it. NameSilo uses a DMV certificate as an alibi in a murder trial. ICANN accreditation doesn't protect you from securities fraud, money laundering, or aiding a $100M theft. The real enforcers are FinCEN, SEC, FBI, and the Arizona Attorney General. ICANN is a decoration.
This is not the first time. Artists Against 419 (2018).
Before xmrwallet, before PhishDestroy, another organization tried. In 2018, Artists Against 419 filed ICANN Compliance complaint UNY-783-11184, accusing NameSilo of being a "bullet-proof registrar" for scammers. Their evidence: reseller QHoster (linked to NameSilo) was responsible for 60% of malicious domains they tracked. NameSilo's response: "We are not a hosting provider" and "We cannot determine the legality of content." ICANN's response: closed the complaint. Reason: the registrar "did not receive the report" or the issues "were outside ICANN's scope."
That was 2018. It's 2026. Nothing changed. The same registrar. The same abuse pattern. The same ICANN non-response. An ICANN Notice of Breach will not fix NameSilo — because abuse is not a bug in their business. Abuse IS the business. You don't send a code-violation notice to a building that was designed to be a front. You send law enforcement.
Why ICANN can't act — and why DOJ won't
Abuse, phishing, scam protection, money laundering, FSB connections — all outside ICANN's mandate. They say so themselves. RAA 3.18 requires "investigating abuse," but ICANN has no investigators, no courts, no power to force-close domains, and no mechanism to verify that a registrar actually investigates. For ICANN, "we received the letter and replied" = compliance. Whether the reply says "we'll remove it" or dismisses the complaint entirely — ICANN doesn't read it.
NiceNIC, Trustname, NameSilo — all technically compliant: pay fees? Yes. Submit data escrow? Yes. WHOIS works? Yes (via PrivacyGuardian). Their business model is ignoring abuse. But ICANN can't punish that, because ICANN doesn't evaluate the content of abuse responses. For bullet-proof registrars outside the US, ICANN's only option is revoking accreditation — a process that takes years and leaves thousands of domains in limbo. ICANN fears technical collapse more than it fears fraud.
NameSilo is a special case. It's a US company in Phoenix, Arizona — subject to US law (Arizona AG, FBI, FinCEN, SEC). ICANN shouldn't need to handle this. This is DOJ's job. But DOJ is silent too:
This is not a single abuse incident that ICANN can address with a Notice of Breach. This is a systemic business model built on enabling cybercrime — phishing, crypto drainers, darknet services, and what the financial data strongly suggests is money laundering at scale. ICANN compliance letters don't fix that. Federal prosecution does.
njal.la is NameSilo. Period.
NameSilo's favorite defense: "That's our reseller, njal.la. We have no control." WHOIS says otherwise. Look up any njal.la domain — the WHOIS registrar field reads NameSilo, LLC. Not njal.la. Not some independent entity. NameSilo. Whatever internal partnership or reseller agreement they have is their private business. To the outside world — to ICANN, to law enforcement, to victims, to WHOIS — these are NameSilo domains under NameSilo's accreditation and NameSilo's responsibility.
Njalla is a legitimate privacy-focused registrar founded by Peter Sunde (of Pirate Bay). It serves journalists, activists, and privacy-conscious users. But its privacy features — registrant shielding, no public WHOIS, minimal paper trail — were systematically exploited to register crypto scam domains and drainers under NameSilo's accreditation. When abuse reports arrived, NameSilo pointed to njal.la; njal.la pointed to privacy. The domains stayed up. The money disappeared. The privacy shield became an abuse shield. Their internal arrangements do not override WHOIS data, ICANN rules, or the law. You cannot outsource your ICANN obligations to a privacy reseller and then claim innocence when domains under your accreditation steal $100 million.
How other registrars compare — from someone who scans hundreds of thousands of domains.
We are not theorists. We scan, analyze, and report domains at scale — hundreds of thousands of them. We work with registrars every day. Here is what we see:
WebNic (~800K domains)
Improving. They now have a real abuse handler — an actual human who reads reports and takes action. He doesn't yet realize their IPs are being blocked by Cloudflare (sends screenshots of "site not working" instead of "phishing"), but there is visible progress. A registrar that is trying to get better.
NiceNIC (Russian, not Chinese)
Hopeless. Will only improve when they cease to exist. A registrar whose business model is built on not responding to abuse. But even NiceNIC never publicly defended a scammer on Twitter. Even NiceNIC never offered to clean VirusTotal for a drainer. Even they have limits.
NameSilo (IANA #1479)
Invented its own ICANN. Created its own WHOIS. Plays by its own rules. Uses accreditation as a weapon, not an obligation. Even Russian registrars like Reg.ru stopped doing what NameSilo does around 2021. NameSilo is still doing it in 2026. They are not a rogue registrar. In our assessment, they are a criminal enterprise with an ICANN badge.
We are not ICANN experts. We are not lawyers. But we destroy 500,000+ phishing domains and can see what entire regulatory bodies apparently cannot: a registrar that invents its own laws, hides behind its own resellers, cites its accreditation as a defense while violating its accreditation's core requirements, and launders money through phantom domain registrations.
To U.S. federal and state authorities — particularly the State of Arizona:
NameSilo, LLC (Phoenix, AZ) is a US-incorporated company protecting a CIS-linked criminal operation that stole an estimated $100M+ from victims worldwide. The evidence is public, the ICANN filing is on record, the operator is identified, the lies are debunked, and the suppression campaign is documented.
This is not a business dispute. This is a US company facilitating ongoing international fraud. The infrastructure patterns — CIS-marketplace freelance orders, DDoS-Guard hosting through Russian-jurisdiction providers, operational methodology consistent with state-adjacent cybercrime — are textbook.
FBI, DOJ Cyber Division, Arizona Attorney General, FinCEN — the evidence package is ready. Contact us and we will provide everything, including materials not published here.
For the FBI specifically: NameSilo fabricated public statements, suppressed security researchers, and offered to remove VirusTotal detections for a known drainer. European authorities have requested information from X/Twitter regarding related cases and received no response — we know this from direct communication with both victims and a competent authority in an EU member state (details cannot be disclosed under EU data protection law). Ask NameSilo why. Ask them who. Ask them how much. Ask before the evidence trail goes cold — though we have ensured most of it cannot be deleted anymore.
If a registrar can say "we received no complaints" while the internet's own memory proves otherwise — if they can delete the evidence using DMCA requests and face zero consequences — then what is the point of regulators? ICANN accreditation becomes a rubber stamp and abuse handling becomes theater.
Subpoena their abuse ticket system. Compare it to what they claimed publicly. The gap between those numbers is the measure of their complicity.
Open Challenge
Prove that a single word we published is false —
and we will take everything down ourselves.
One word. One claim. One screenshot. Show us what's wrong.
Across hundreds of pages of evidence, dozens of victim reports, and 61 SHA-256 verified screenshots — not the operator, not NameSilo, not X, not anyone has produced a single factual rebuttal. Not one.
But if everything we say is true — then DO SOMETHING.
They are stealing millions. Right now. Today. The site is live. The domain is active. Victims are losing money while you read this. Act now.
We did not spend months of our lives building this archive, and victims did not lose millions of dollars, so that a Russian-speaking scammer could post one lie on Twitter and then cry that we saved it. NameSilo wrote 4 false sentences from an official corporate account. We archived them. They got upset that the archive exists. Their entire defense is not "it's false" — it's that the archive exists at all.
That's not how this works. You said it. We saved it. The world can read it. Deal with it.
NameSilo's response playbook — and our pre-written answers
We've dealt with enough registrars to know exactly what they'll say. Here's the script, and here's why it doesn't work.
🎙 "We are an ICANN-accredited registrar."
Yes, we know. It's a commercial license, not a character reference. Trustname.com (IANA #4318) is also accredited with €120 revenue.
🎙 "The domain was compromised."
SHA-256 hashes show code/IP never changed. Operator never claimed compromise. You invented this story.
🎙 "We had received no abuse reports."
20+ reports from us, 100+ total from public posts (BitcoinTalk 2021, Reddit 2018).
🎙 "Dead domains are normal in our industry."
Baseline is 15-21%. You're at 32.2% (2x baseline), with 615% YOY spike and 10K-17K/day bulk runs. Explain the gap.
🎙 "njal.la is an independent reseller."
WHOIS says NameSilo, LLC. Your internal arrangements don't override public data or law. Njalla domains are your responsibility.
🎙 "We will pursue legal action."
Operator threatened this in Feb. We're on IPFS. Claims are sourced, SHA-256 verified. Truth is defense. Sue us — this archive becomes court exhibit A-Z.
🎙 [Silence]
Also an option. Evidence sits on decentralized network. Silence is not a strategy. It's a countdown.
NameSilo & the SEO Grandpa playbook — same tricks:
NameSilo buys reputation the same way the xmrwallet operator does — different budget, same playbook. Forbes Advisor "review" ($50,000+ placement). Yahoo Finance press releases (labeled "paid"). Wikipedia article (flagged as promotional). Trustpilot bot farm (92% manipulation probability). Both use PR Newswire (Cision) for press releases. Both have almost zero organic web presence. The detailed fact-check of Forbes, Trustpilot data analysis, and BBB complaints are in the evidence section below.
Behavioral Pattern Match — Operator vs Registrar
We weren't looking for this. While investigating xmrwallet's fraud infrastructure, we noticed something unexpected: both entities use the same PR platform, both have zero organic web presence, both delete Trustpilot reviews, and both respond to evidence with threats instead of facts. These are not coincidences — they are structural.
xmrwallet Trustpilot: May 2024 Wayback snapshot shows 45 reviews, rating 3.6 (27% one-star). Current scrape: 80 reviews, 51% five-star. We compared names: 7 reviews deleted from page 1 alone, including:
• "Elmo T. Johnson" — "XMRWallet swindled my funds. 1200 monero was vanished" — DELETED
• "B.Costa" — "Nathalie solved it" — DELETED (mentions operator by name)
• 2 verified reviews (Trustpilot checkmark) — DELETED
• 3 of their own bot reviews ("Thomas", "Jabari Rivera", "Evelyn Malik") — deleted after serving purpose
Victim testimony: Erma Powell (verified Trustpilot account, green checkmark) posted Apr 22, 2024: "I'm in a panic, I created a wallet on the official site, put money in and the developers took everything, the code on github has nothing to do with this site." Trustpilot removed it: "breaching Guidelines for Reviewers."
NameSilo Trustpilot: Jan 2026 Wayback snapshot: 2,609 reviews. Current (May 2026): 2,480. That's 129 reviews deleted in 4 months. Rating: 4.7 (2023) → 4.5 (2024) → 4.7 (2025) — recovered despite adding 600+ reviews. This only happens when negatives are deleted faster than they arrive.
Wayback Machine snapshots: NameSilo Trustpilot 2023 → 2024 → 2025 → mid-2025 → Jan 2026. Track the review count and rating changes over time. Click to enlarge.
Sources: Wayback xmrwallet May 2024 · Wayback NameSilo Jan 2026 · Full data (JSON)
On Trustpilot, NameSilo maintains a 4.7/5 rating by deleting 129 negative reviews in 4 months and planting bot reviews praising "Leonid." On SmartCustomer.com — a platform where businesses cannot delete reviews — NameSilo's real rating is 1.8/5. 76% are one-star.
4.7/5
Trustpilot (manipulated)
129 reviews deleted, bots planted
1.8/5
SmartCustomer (unmanipulated)
42 real reviews, 76% one-star
Abuse-related reviews on SmartCustomer:
And the 5-star reviews? Same pattern as Trustpilot — "Leonid was extremely helpful with all my questions" (Jagoda S., May 2025). Same name, same template.
Source: smartcustomer.com/reviews/namesilo.com · Full data (JSON, 42 reviews) · HTML cached: p1 p2 p3
Trustpilot's business model prioritizes companies over consumers. Businesses can flag reviews, request removals, and leverage paid features to manage their reputation. Both xmrwallet and NameSilo exploit this to suppress truth. On platforms where they can't — the real ratings emerge.
xmrwallet.com
NameSilo
The Trustpilot pattern is identical for both: aggressively delete negative reviews, plant bot positives (praising "Leonid" for NameSilo, praising "Nathalie" for xmrwallet), maintain an artificially high rating. On Trustpilot, a phishing wallet that stole $100M+ had a rating higher than most legitimate cryptocurrency exchanges. No other Monero wallet even has a Trustpilot page — because real wallets don't need reputation laundering.
Both exploit Trustpilot's business-first model where the company being reviewed has tools to flag, dispute, and remove reviews. On platforms without these tools (SmartCustomer, ScamAdviser) the truth emerges instantly. Same platform. Same playbook. Same result.
The pattern that proves it's deliberate:
Both entities removed themselves from every honest review platform — Sitejabber (now SmartCustomer), ScamAdviser, MyWOT — but kept and actively managed only Trustpilot, the one platform where businesses can suppress negative reviews. Consider what this means:
Where they can't delete — they abandon. Where they can delete — they invest. Both entities chose the same platform, used the same methods, and achieved the same result: fake credibility. This is not two separate decisions. This is one playbook.
Sources: SmartCustomer xmrwallet · ScamAdviser xmrwallet · MyWOT xmrwallet · MyWOT NameSilo · ScamAdviser NameSilo · All screenshots & HTML cached.
Many people assume it's impossible to manipulate search results, delete reviews, or control what appears online. It's not only possible — it's a professional industry with fixed prices and guaranteed delivery.
There are escrow-based platforms where reputation management is sold as a service. Money goes in, the order is verified, the negative content disappears, the seller gets paid. These are not underground forums — they operate openly with "VIP Member" badges, review counts, and customer ratings. The services include:
This is how xmrwallet maintained a Trustpilot rating higher than legitimate crypto exchanges while stealing $100M+. And how NameSilo maintains 4.7/5 while 76% of real reviews on other platforms are one-star. It's not magic — it's a marketplace.
Proof that this suppression is active against us: NiceNIC (another bulletproof registrar) flagged and removed our Trustpilot review — a moderate 3-star, factual assessment — claiming it contained "harmful or illegal content." The same mechanism. The same playbook.
Screenshots from reputation management marketplaces (platform name withheld). Last image: PhishDestroy's own Trustpilot review of NiceNIC — removed after being flagged as "harmful content." A factual, moderate 3-star review about a registrar with 1.5/5 real rating. This is the system they exploit.
A "volunteer open-source wallet" publishing press releases on a platform designed for publicly-traded companies is not normal. It's someone with access to a corporate PR account — or the same PR agent.
xmrwallet releases
Jan 21, 2026 — "Expands Privacy Access with Full Tor Network Integration"
Apr 19, 2023 — "Upgrade Website to Support Charities"
Sep 26, 2023 — "Companies Embrace Cryptocurrency"
Contact: Nathalie Roy, +1 300-227-473 (fake), 407923@email4pr.com
NameSilo releases (12)
Jan 22, 2026 — "Surpasses 6 Million Domains" (1 day after xmrwallet)
May 1, 2026 — 2025 Year-End Results
+ 10 more: Q1-Q3 results, SewerVue, CommerceHQ, Reach Systems, subsidiary sale
The Tor release kicker: the PR Newswire release announces "Tor Network Integration" for an "open-source" project whose last GitHub commit was November 6, 2018 — over 7 years before. No Tor code was ever committed. They paid $800+ to advertise a feature that doesn't exist in their codebase.
All 15 pages archived: Browse cached releases
On May 5, 2026, the xmrwallet operator posted a closure announcement on the site. Signed "The Creator." The letter admits that the investigation forced shutdown — but contains verifiable lies and contradicts his earlier emails. The domain remains active. NameSilo still hasn't suspended it.
Left: NameSilo's official response — threats, zero facts. Center: Yahoo Finance labels their "news" as "paid press release" (Cision logo). Right: Forbes Advisor shows "We earn a commission" — paid review placement, not journalism.
But let's talk about NameSilo itself.
How we stumbled onto this.
We never set out to analyze NameSilo's entire domain portfolio. We work with registrar data constantly — it's part of what we do when tracking phishing infrastructure. We know that a large percentage of domains on the internet are dead. That's normal. People buy domains and forget about them. Companies register names defensively. Speculators sit on inventory. We get it. We never assumed that "dead domain = suspicious."
But when we were scrolling through the NameSilo dataset — 5.18 million rows — something felt off. Not a statistic. Not a number. Just a visual impression. Row after row of gibberish domain names. sdf8k3jx.sbs, x9wqm2.cfd, aaa111bbb.xyz — with no IP, no email, no phone, no Majestic rank. Just... nothing. Thousands of them. Tens of thousands. The sheer density of emptiness was unusual. We've looked at datasets from GoDaddy, Namecheap, Tucows — they all have dead domains, but the ratio of obviously-random-garbage to real-looking names was different at NameSilo. It was visible to the naked eye.
So we decided to count. Not to prove a theory — we didn't have one. Just to see if our gut feeling was backed by numbers. We pulled datasets from 8 registrars, 130 million domains total, applied the same methodology to all of them, and compared.
The gut feeling was correct. NameSilo was 10 percentage points above its closest competitor. The dead domain rate was 2x the industry baseline. And when we dug deeper — the 615% year-over-year spike, the 10,000 domains/day bulk runs, the junk TLD concentration — it stopped looking like neglect and started looking like a pattern. We didn't go looking for money laundering. The data showed it to us.
Suspected Money Laundering Flow
Why are 81.5% of NameSilo domains dead?
DNS scan: 32.2% no IP + 33% parking stubs = 2.82M (54.4%). Full economic analysis (age, MX, content, patterns): 4.22 million dead domains — 81.5% of 5.18M. There are only 3 possible explanations. All of them are damning:
Theory 1: Money Laundering
Stolen funds converted to domain purchases. Registrar gets "revenue." Domains are never used — the transaction IS the purpose. $50.8M/year phantom profit from dead registrations.
Theory 2: Self-Dealing
NameSilo buys domains from itself to inflate revenue. C$65.5M revenue looks great for investors. But 81.5% of domains are dead. Real active-customer revenue is ~C$12M. The stock trades at P/E 143.8x on phantom numbers. Securities fraud.
Theory 3: Front Operation
The registrar was never built for real customers. The Win98 panel, the $15.56 .com price (#96 of 130), the ignored abuse reports — these aren't failures. They're features. The real product is the transaction itself: accept money, register domain, report revenue, never ask questions. A front doesn't need a good UI. It needs a good accountant.
"But maybe there's a legitimate explanation?"
We've heard every excuse. Let's address them honestly:
"Chinese gambling sites buy bulk domains"
Gambling sites use their domains. They have websites, content, traffic, ads. NameSilo's dead domains have no IP, no DNS, no MX, no content. Nothing. A gambling operator buying 10,000 domains puts casinos on them. NameSilo's buyers put nothing.
"Privacy-conscious users don't activate domains immediately"
Privacy registrars exist — Njalla, Gandi, even NiceNIC. Their customers buy domains to use them, privately. NameSilo's dead domains aren't private-but-active. They're private-and-dead. No website. No email. No DNS. For years. That's not privacy — that's a transaction with no purpose except the transaction itself.
"Every registrar has dead domains"
Yes. Industry baseline: 15-21%. Namecheap: 32.6%. NameSilo: 81.5%. That's not a difference in degree. That's a different business model. And it's growing — 615% year-over-year spike in dead registrations. No legitimate market force produces this pattern. Organic domain sales don't grow 6x in one year while the domains being sold are never used.
"Domain investors hold portfolios"
Domain investors park domains on Sedo, Afternic, or Dan.com — showing "for sale" pages. That registers as alive in our scan. NameSilo's dead domains don't even have parking pages. They have nothing. An investor who buys a domain and doesn't even park it is an investor with no intention of selling. That's not investing. That's laundering.
No rational buyer — Chinese, American, or Martian — purchases thousands of domains per day, with growing volume, to never use them. There is no legitimate fourth explanation. If you find one, we'll take everything down.
The NameSilo Pyramid — 5.18 Million Domains Deconstructed
What happens when you actually check if anyone uses these domains?
What this means in human terms:
The "dirty ratio" depends on what you compare against:
This is why NameSilo buys phantom domains. When you compare 22,000 malicious domains against 5.18 million total, it's "0.43% — barely anything." But when you strip away the dead weight and compare against domains that actually work, the picture changes completely. The phantom domains are a statistical smokescreen.
Why would anyone choose NameSilo?
A serious question. We looked at every possible reason and tested each one.
Why Namecheap as the benchmark? Both companies are in the same US state (AZ), similar scale, both accept cryptocurrency, both offer API access, and both compete for the same budget-conscious bulk registrant. Namecheap is the closest legitimate analogue to NameSilo — same market, same tools, same customer base. Any difference in dead domain rates, abuse patterns, or business practices between these two cannot be explained by pricing or geography. We have no affiliation with Namecheap and do not intend to cause them any reputational harm. They appear in this report solely because they are the most methodologically honest comparison available. We apologize to Namecheap for any inconvenience this comparison may cause.
Every ICANN-accredited registrar sells the same product — domain names. The TLDs are identical. A .com from NameSilo and a .com from Namecheap point to the same root servers, managed by the same registry (Verisign). There is zero technical difference. So why would a customer choose NameSilo? Let's check every possible reason:
Is it the price?
We checked .com prices across 136 ICANN-accredited registrars using tldes.com (independent price comparison, updated live). Here's where NameSilo actually ranks:
NameSilo's own "vs Other Registrars" page compares their $17.29 against Squarespace ($20), GoDaddy ($23.98), and Name.com ($17.99) — cherry-picked expensive competitors with inflated prices. They conveniently forgot the 95+ that are cheaper. Here's the comparison they didn't want you to see:
95 ICANN-accredited registrars sell .com cheaper than NameSilo. Not 5. Not 20. Ninety-five. Namecheap is 2.2x cheaper. Spaceship is 5.4x cheaper. Cloudflare is 1.5x cheaper. All sell the exact same product — a .com domain from the same Verisign registry. All include free WHOIS privacy. All are ICANN-accredited. So why does NameSilo have 5.8 million domains?
Their own comparison page is deliberately misleading.
On namesilo.com, the "NameSilo vs Other Registrars" comparison shows their $17.29 .com against Squarespace ($20.00), GoDaddy ($23.98), and Name.com ($17.99). But wait — those aren't even the real prices. On tldes.com, GoDaddy is $5.19 (not $23.98) and Name.com is $11.24 (not $17.99). NameSilo used inflated renewal/promo-excluded prices for competitors while showing their own registration price. Both GoDaddy and Name.com are actually cheaper than NameSilo at registration. They didn't just cherry-pick expensive competitors — they inflated the competitors' prices too. And they excluded Spaceship ($2.90), Namecheap ($6.99), Cloudflare ($10.46), Porkbun ($10.08), Dynadot ($8.99), and 100+ other cheaper registrars. This is not a comparison — it's marketing fraud. And they highlight "BULK DISCOUNTS" as a unique feature — because of course they do. Bulk discounts for bulk phantom purchases.
They also advertise "Over 150+ Payment Options Accepted". We counted. Their checkout page lists: Visa, Mastercard, Amex, Discover, JCB, Elo, UnionPay (7 cards), PayPal, Alipay, Venmo (3 web wallets), Bitcoin (1 crypto), and NameSilo Account Funds (1 internal). That's 12 payment methods. Not 150. We looked everywhere — no bank transfers, no wire, no other crypto, no invoice billing. Twelve. They inflated the payment count by 12.5x on their own website. The same way they inflate domain counts, revenue figures, and competitor prices. It's a pattern.
Source: tldes.com/com — independent price comparison, 136 ICANN-accredited registrars, live prices. Also cross-referenced with tld-list.com. Verify yourself — the data is public.
"Cheapest on the Internet" — across 12 TLDs
NameSilo's own claim: "we have the cheapest domain name registration prices on the Internet." Here's every TLD checked.
The Renewal Trap — cheap registration, predatory renewal
NameSilo's "cheap" TLDs are a bait-and-switch: .shop $1.99 → $38.99 (19.6x), .tech $7.99 → $68.99 (8.6x), .xyz $1.79 → $15.79 (8.8x), .info $3.75 → $29.49 (7.9x). Register cheap, renew expensive. But dead domains don't renew — which is exactly the point. If you're buying domains to wash money, you only care about the $0.99 registration price. The $14.95 renewal never happens because the domain expires after 1 year. This is why 98% of dead .buzz domains are 1-year registrations.
NameSilo owns 19.8% of ALL .sbs domains on Earth
374,910 out of 1,895,100 global .sbs registrations are at NameSilo. One registrar holds one-fifth of an entire TLD. For context: NameSilo holds 1.1% of .com. The expected share for a "top 10 registrar" is 2-5% of any TLD. 19.8% in a single junk TLD from their named partner ShortDot is not market success — it's a captive pipeline.
Is it the UX?
Is it the support?
We tested it. We sent the same abuse report (xmrwallet.com) to multiple registrars. Namecheap: responded and acted. WebNic, PDR, Key-Systems: responded and acted. NameSilo: ignored 20+ reports, publicly lied, offered VT delisting for the scammer, used Gold Checkmark to silence researchers. Their "24/7 Customer Service" (investor deck, slide 6) apparently does not extend to abuse victims.
Is it the ICANN accreditation?
Every registrar in this comparison is ICANN-accredited. That's literally the requirement to sell gTLD domains. There are ~2,500 ICANN-accredited registrars worldwide. NameSilo is not special. Trustname.com (IANA #4318) is also accredited — with €120 in revenue. ICANN accreditation is the domain equivalent of having a business license. It means you filled out the form. It does not mean you are trustworthy, affordable, or competent.
Is it the design? The brand? The reputation?
Their Wikipedia page is flagged as promotional. Their Forbes review is paid placement. Their Trustpilot has bot review patterns. Their admin panel looks like it was designed by the same person who orders SEO articles on Kwork for 500 rubles. Their CEO admitted they need a "complete UX overhaul" after seven years. Their Q1 and Q2 2025 press releases are identical copy-paste.
So why does NameSilo have 5.18 million domains?
Not price. Not UX. Not support. Not reputation. Not ICANN (everyone has it). Then what? The only explanation left is that most of these domains are not bought by real customers making rational choices. They are bought in bulk by unknown actors for unknown purposes — or by NameSilo from itself. Either way, the "5.8M active domains" number that drives the stock price is not what investors think it is.
Lying is not just their cover-up strategy. It's their business model.
Let's step back and look at what we've documented. Every single public-facing claim NameSilo makes is inflated, fabricated, or misleading:
This is not a company that lied once to protect a scammer and got caught. Lying is the operating principle. Every metric, every comparison, every public statement is engineered to show a number larger than reality. The xmrwallet cover-up wasn't an anomaly — it was the same reflex applied to an abuse report. Inflate, deny, deflect, cite ICANN accreditation, move on.
And this answers the original question: why does anyone "choose" NameSilo? Real customers making rational decisions don't choose NameSilo. 95 registrars are cheaper for .com. The UI is from 2008. The support ignores abuse. The only "customers" who need NameSilo are those who need: bulk registration with no questions asked, junk TLDs at $0.99, a privacy service that shields 109K malicious domains, and a registrar that will publicly defend you when you get caught. That's not a customer base. That's an arrangement.
The money comes from phantom domains. The phantom domains come from bulk buyers who don't exist as real businesses. The "revenue growth" comes from counting phantoms. The stock price comes from the revenue growth. Everyone in this chain gets paid. Except the investors. And the victims.
The Numbers Don't Lie
NameSilo (suspicious)
• 1.67M no IP at all + 1.15M on parking stubs = 2.82M DNS-dead
• Full economic analysis (age, MX, content, patterns): 4.22M dead
• Combined: ~4.22M out of 5.18M (81.5%) are dead domains
• $50M+ phantom revenue from dead registrations
• 96% no contact email
• 18% junk TLDs (.sbs/.cfd/.xyz)
• 7x spike in dead registrations 2023→2024
• P/E 143.8x (industry: 21x)
• Forbes: PAID review
• Wikipedia: PROMO flagged
• Trustpilot: bot reviews
Namecheap (how a real registrar works)
• 32.6% dead domains (industry baseline)
• Similar pricing, same market, same state (AZ)
• 93.5% no email (lower)
• 54% .com (legitimate TLD mix)
• Steady growth, no spikes
• Responds to every abuse report
• We worked with them directly — showed cloaked scam, they acted
• Modern, clean design
• Significantly larger — 24M+ domains
• No criminal resellers. No FSB connections.
• Organic press, clean Wikipedia, real reviews
• This is what a registrar looks like when it's not a front
NameSilo is 10 percentage points dirtier than its closest peer. This is not a business model difference. This is a red flag.
"But NameSilo is cheaper!" — Is it?
NameSilo's only selling point is price. Their own comparison page shows $17.29 .com against Squarespace and GoDaddy. Let's check the real numbers from tldes.com (independent comparison, 136 registrars):
Who owns .sbs and .cfd? Follow the money.
Registry ↔ Registrar — a partnership worth examining.
The junk TLDs filling NameSilo's dead domain graveyard — .sbs, .cfd, .icu, .cyou, .bond, .buzz, .qpon — are all owned by a single company: ShortDot SA, a Luxembourg-registered Société Anonyme (9 Rue Louvigny, L-1946). ShortDot operates 7 TLDs through CentralNic (London) as technical backend.
On their own website (shortdot.bond/about), ShortDot lists their key registrar partners. Out of "over 400 registrar partners", they name exactly six by name:
NameSilo is one of six named partners of the company that owns the exact TLDs dominating their phantom domain portfolio. Now look at the timeline:
The economics of this partnership:
NameSilo's ShortDot TLD share vs other registrars:
These are not accusations. These are questions that demand answers:
A named partnership. A synchronized timeline. A 55x concentration anomaly. A 615% spike in phantom registrations. If this is a coincidence, it is the most expensive coincidence in the history of domain registration.
Sources: shortdot.bond/about (partner list), IANA .sbs delegation, IANA .cfd delegation, PhishDestroy 130M domain analysis.
And then there's njal.la (Njalla) — a privacy-focused registrar whose domains resolve under NameSilo's ICANN accreditation (check any WHOIS). Their pricing: €15/year for .com, €30/year for junk TLDs (.sbs, .cfd, .cyou, .xyz, .homes — the exact TLDs filling NameSilo's dead domain graveyard). That's 2× to 30× more than what NameSilo charges retail for those same TLDs. Why would anyone pay €30 for a .sbs that costs $0.99 direct? You wouldn't — unless the point isn't the price. The point is the privacy layer. Njalla registers on your behalf, their name on WHOIS, your identity hidden. For legitimate privacy? Maybe. For scam domains that need to survive abuse reports? Perfect. And when the abuse report arrives, NameSilo says "that's njal.la, not us" — while WHOIS says NameSilo, LLC on every single domain.
Namecheap — 24M+ domains
• 2.2x cheaper for .com ($6.99 vs $15.56)
• Modern panel, 2FA, real-time DNS
• Abuse reports: same-day action (we verified)
• Clean Trustpilot, organic Wikipedia
• No dead domain spikes
• No FSB connections
• 4.6x more total domains (~19x more active)
• Lower dead rate (32.6% vs 81.5%)
• Real customer base: ~18.6M active
NameSilo — 5.18M domains
• 2.2x more expensive for .com ($15.56)
• Panel from the Win98 era (see recreation)
• Abuse reports: auto-deleted (100+ ignored)
• Bot Trustpilot, promo Wikipedia
• 615% spike in phantom registrations
• VT delisting service for scammers
• 81.5% dead domains
• 99.65% zero confirmed traffic
• Real customer base: ~958K active
Namecheap is 2.2x cheaper for .com (#6 vs #96), 4.6x bigger, has a modern UX, responds to abuse, and doesn't trade at P/E 143.8x. Adjusted for phantoms, Namecheap's real customer base is ~19x larger. The "NameSilo is cheaper" narrative is not just wrong — it's the opposite of reality. NameSilo is one of the most expensive registrars in the world for .com. Where they ARE cheapest is .sbs at $0.99, .cfd at $0.99 — their ShortDot partner's TLDs that fill the dead domain graveyard.
If NameSilo really is just a discount registrar — where are the customers? Same market, similar pricing, one has 19x more real users. The answer is in the pyramid above: 99.65% of NameSilo's portfolio has zero confirmed traffic. 58 domains in Tranco top 10K. Fifty-eight. The price isn't the product. The phantom domains are the product.
Why would a registrar buy domains from itself?
1. Money laundering. Stolen crypto → Bitcoin → domain purchases at your own registrar. The registrar reports "revenue." The money is clean. Up to $50.8M/year in phantom profit. No questions asked because who audits domain registrations?
2. Ranking inflation. ICANN rankings, industry reports, and press coverage use "domains under management" as the primary metric. More domains = bigger registrar = more trust = more real customers. NameSilo claims "top 10 registrar" status with 6.26M domains. How many are real? If 81.5% are dead, the real active base is ~958K. That's not top 10. That's mid-tier at best.
3. Revenue inflation for stock price. NameSilo Technologies trades at P/E 143.8x. Revenue grew 18.5% in 2025. But how much of that growth is phantom domains? Inflated revenue = inflated stock = real money for insiders selling shares. This is textbook securities fraud if the domain purchases are self-dealing.
4. Diluting the scam ratio. This is the clever part. If 5% of your domains are involved in scam/phishing/fraud, that looks terrible. But if you buy 2 million dead domains from yourself, suddenly scam domains are only 0.5% of your total. "We have 6 million domains and only a tiny fraction are problematic." The dead domains are a smokescreen — statistical noise to make the abuse percentage look smaller than it is.
All four benefits come from the same action: buy domains from yourself. Launder money. Inflate rank. Inflate stock. Dilute the scam ratio. One move, four wins. Who's checking?
A question for NameSilo Technologies investors
CSE: URL · OTC: URLOF · C$1.44 · Market cap: C$133M · Shares: 92.6M · CEO: Paul Andreola
Q3 2025: Revenue C$16.9M (+17.9%) · Net income C$1.15M (+135%) · Cash: C$2.4M · Deferred rev: C$33M
For NameSilo shareholders:
You bought shares in a company with a P/E of 143.8x — 7x the industry average. Do you know that 81.5% of the domains you're paying for are dead or empty? 4.2 million domains that nobody uses. Your company's "6.26 million domains under management" is really about 958,188 active domains. The rest is either phantom registrations or parking page filler. The "18.5% revenue growth" in 2025 — how much of that is real customers, and how much is bulk dead-domain purchases that inflate the top line?
Your company publicly defended a $100M+ theft operation. Your company offered to remove VirusTotal security detections for a known crypto drainer. Your company used paid platform access (X Gold Checkmark) to silence the researchers who exposed it. Your company's CEO signed off on a tweet containing 4 statements contradicted by evidence. Is this what you invested in? Did you know? Do you know now?
If the dead domain purchases are self-dealing — which the data strongly suggests — then the revenue figures in NameSilo's financial statements are materially misleading. That's not a registrar problem. That's a securities fraud problem. CSE, OSC, and SEC should be asking questions. Shareholders should be demanding an independent audit of domain registration sources. Who is buying 10,000+ domains per day with no intent to use them? Where is the money coming from? Follow the money.
5. The affiliate excuse. NameSilo will claim their Forbes and other "reviews" are affiliate partnerships — just like the xmrwallet operator claims "donations" fund his operation. Technically, some links in those articles use affiliate tracking. But others link directly — no tracking, no commissions. Someone is buying reviews of themselves without even bothering to earn referral fees. The point isn't the affiliate cut. The point is purchased legitimacy.
Adjusted Financials
Strip the Phantoms — What Is NameSilo Actually Worth?
Take the reported numbers. Remove 81.5% dead domains. See what's left.
Methodology: "Adjusted revenue" = reported revenue × (active domains / total domains). Active = 958,188 (HTTP alive with content). This is conservative — some "alive" domains are still speculative or parked. Net income adjusted proportionally. P/E = market cap / adjusted net income. Revenue/domain increases because real customers pay more than bulk junk TLD buyers.
REPORTED TO INVESTORS
C$65.5M
"Fastest growing registrar"
REAL BUSINESS (PHANTOMS STRIPPED)
~C$12M
A small mid-tier registrar, overvalued 10x
C$53.5M per year — the gap between reported and real. That's not rounding error. That's not market fluctuation. That's not "different accounting methods." That's either the biggest bulk-buying customer in registrar history who generates zero traffic — or it's fraud. There is no third explanation. CSE, OSC, SEDAR+ — this gap should trigger an independent audit. It hasn't. Yet.
Corporate Structure
Why Canada? Why CSE? Why is the business in Arizona?
The corporate structure is not an accident. It's a feature.
NameSilo Technologies Corp
Canada — holding company
Trades on CSE: URL (Canadian Securities Exchange)
OTC: URLOF
CEO: Paul Andreola
CFO: Natasha Tsai (signs the phantom numbers)
NameSilo LLC
Phoenix, Arizona — actual registrar
ICANN-accredited (IANA #1479)
CEO: Kristaps Ronka (18.5% owner)
Accepts Bitcoin. No KYC. Generates the "revenue."
Why this structure exists:
Al Capone kept his business in one state and his banks in another. Same logic, different century.
Canada's regulatory gaps — by design
Crypto & Registrars
Canada tightened AML for crypto exchanges (FINTRAC, Travel Rule from 2026). But an ICANN registrar accepting Bitcoin for domains is not an MSB (Money Services Business). Buying a domain is a goods transaction, not a financial service. The registrar is not required to run exchange-level KYC or file SARs (Suspicious Activity Reports) per BTC transaction.
Privacy Laws (PIPEDA + Quebec)
In Canada — especially Quebec — personal data protection is stronger than in the US. Until recently, there was no public beneficial ownership registry. You couldn't simply look up who's behind a company. To deanonymize a "private citizen" you need a criminal subpoena, not a civil discovery request or regulatory inquiry.
The Corp + LLC structure is legal — thousands of companies use it. FINTRAC/OSC are real regulators, but their resources are dwarfed by SEC/FBI. The risk appears only when you combine legal corporate structures with phantom operations — which is exactly what the data shows.
"Nathalie Roy" — not a brand for victims. A regulatory shield for the operator.
The xmrwallet operator chose a specific identity construction: a Canadian female volunteer running a non-commercial open-source project. This is not random. It's a regulatory strategy:
In 2014–2019, crypto wallets operated by "private individuals" did not fall under MSB regulations. Canadian/Quebec privacy laws shielded personal identity without corporate transparency. The "volunteer" + "non-commercial" combination provided exemption from AML/KYC obligations. A "donation-based volunteer project" was a regulatory grey zone that FinCEN and FINTRAC did not aggressively cover.
If the operator had registered as "XMRWallet Ltd." or used a male Eastern European name — regulators would have investigated by 2016–2017. A "Canadian female volunteer" was a status that regulators ignored until it was too late. The identity doesn't exist as a business. That's exactly why the scheme worked for 10 years.
"Nathalie Roy" is not a person. It's a legal construct optimized for regulatory evasion.
Integration Phase
Why Sewer Pipes? Why Underwater Cameras? Why Mexican Taxi Ads?
NameSilo's "diversification" makes no business sense — unless you understand the three phases of money laundering.
Phase 3 is the EXIT. You can't sit on $50.8M phantom profit forever. You need to convert paper money into real assets:
And the more random the acquisitions, the better the cover. If they only bought domain companies, the pattern would be obvious. But sewer pipes + underwater robots + Mexican taxi ads? That looks like an eccentric CEO "diversifying." Nobody investigates a sewer pipe company for money laundering connections. That's the point.
Al Capone had laundromats. NameSilo has sewer pipes.
Different century, same logic: push dirty money through a business, buy real assets, look legitimate.
The operator kept victims silent for a decade. Then he tried it on us. We documented it all before it happened.
Gold Checkmark corporate support used to lock @Phish_Destroy. X reviewed: "no violation." Still locked.
All phishdestroy.io results removed from Bing. Complete erasure from Microsoft search.
False DMCA takedowns against repos. Operator deleted Issues #35 & #36 with victim reports.
100+ victim reviews removed through automated moderation abuse.
DMCA requests against Google search results, domains, hosting. Anything reportable gets reported.
50+ paid articles via Kwork, Freelancehunt, intermediaries. Orders indexed on Google Drive.
Technical analysis videos reported and removed. Researchers demonstrating the theft silenced.
Coordinated reporting against warning threads. Community discussion suppressed.
Government email addresses used to file fraudulent abuse reports on platforms.
"Open source" wallet on bulletproof hosting. GitHub code ≠ production code. Anti-analysis infrastructure.
Report buttons, DMCA systems, freelance marketplaces — every available mechanism has been weaponized for suppression. This is a decade-long strategy — not an accident. The operator and NameSilo are on the same side. The case file is with ICANN Contractual Compliance and federal law enforcement.
Prosecution Brief
The Case for Money Laundering
Not a theory. Not speculation. A chain of evidence that leads to one conclusion.
STEAL
xmrwallet.com hijacks Monero transactions for 8+ years. Estimated $100M+ stolen. Funds are in XMR — untraceable by design.
CONVERT
XMR → BTC via DEX/mixers/OTC. Untraceable step. Output: Bitcoin in anonymous wallets.
WASH
Buy domains in bulk at NameSilo. NameSilo accepts Bitcoin. No identity verification required. 10,000-17,000 domains/day. Junk TLDs at $0.99 each from their ShortDot partner. No WHOIS contact. No email. No phone. The domains are never activated — the purchase IS the purpose.
REPORT
NameSilo books the purchases as legitimate revenue. C$65.5M/year. "Fastest growing registrar." "6.26M domains under management." Files quarterly earnings on SEDAR+. Stock trades on CSE (URL) and OTC (URLOF). P/E 143.8x. Phantom domains become phantom revenue becomes real stock price.
CASH OUT
Insiders sell shares on a public exchange. Clean money. Kristaps Ronka (18.5% owner, LLC CEO) holds ~17M shares. Paul Andreola (parent company CEO) has board control. The stolen crypto has been transformed into Canadian stock market equity. The laundry is complete.
The Bitcoin On-Ramp
NameSilo accepts Bitcoin as payment. This is not a technical detail — this is the on-ramp. The laundering pipeline is: stolen XMR → BTC (via DEX/mixers) → domain purchases at NameSilo → "revenue." The entire chain from theft to clean money requires zero identity verification. No KYC. No bank. No wire transfer. Just Bitcoin to domains to stock price. They don't even accept Monero — which is strange for a registrar that protects the world's largest Monero theft operation. Or maybe not strange at all: accepting XMR directly would be too obvious. The BTC step is the mixer.
The Math
Someone is spending millions of dollars per year to buy domains they never use, from a registrar that accepts Bitcoin and asks no questions, and nobody knows who they are. This is either the worst investment in internet history or a money laundering operation.
Every one of these questions can be answered with a single subpoena.
The only reason they haven't been answered is that nobody has asked.
Updated Analysis
The Money Laundering Machine — How It Actually Works
A car wash that washes 10 cars a day but reports 100. Where does the money for 90 phantom cars come from? NameSilo is the same — except instead of cars, it's domains. 4.2 million phantom "washes" that don't exist.
How the scheme works — step by step
Why this works perfectly:
1. PrivacyGuardian hides the buyer
Every domain registered to pw-{hex}@privacyguardian.org. Impossible to prove the "client" = NameSilo itself. 3M+ PG-protected domains.
2. Domains are the perfect product
Digital, no warehouse, no shipping, no trace. Cheap wholesale, expensive retail. Millions of units — easy to hide thousands of "your own" among real ones.
3. Cheap TLDs = maximum multiplier
.cyou: $0.48 → $14.95 = 31x
.sbs: $0.68 → $14.95 = 22x
.cfd: $0.68 → $14.95 = 22x
.icu: $0.98 → $14.95 = 15x
4. Scale makes it invisible
5.18M domains — who checks each one? Real customers mixed in as cover. 4,260 new dead domains per day in 2025.
The economics of laundering through NameSilo
The dead domains dominate the economics. At estimated retail prices, dead domain registrations represent $77.3M in value (wholesale cost: $26.5M, paper margin: $50.8M). NameSilo's actual reported revenue is C$65.5M (~US$48M) — the gap reflects bulk discounts and junk TLD pricing. Either way, the vast majority of revenue comes from domains nobody uses. The tail wags the dog.
Evidence that this is exactly what's happening
NameSilo is a digital car wash.
4.2 million phantom cars. $50.8 million in phantom profit.
And the only "soap" they use is a $0.68 wholesale domain from their own partner.
Financial Analysis
Follow the Money — Who Pays and For What?
C$65.5M revenue. 5.18M domains. Let's see how much is real.
The Client Problem
If NameSilo's 5.18M domains belong to real customers making real purchases — where are they?
Real customers would have:
• Working websites (only 18.5% respond to HTTP)
• Contact emails (96% have none)
• Business identity (1.06% have org name)
• Measurable traffic (0.35% in top-million)
• Reason to pick NameSilo over 95 cheaper options
NameSilo's "customers" have:
• No website (81.5%)
• No email (96%)
• No business name (98.9%)
• No traffic (99.65%)
• Gibberish domain names on .sbs/.cfd
• Registered 10,000-17,000/day in bulk runs
Who are these "customers"? They have no website. No email. No business. No traffic. They buy domains they never use, on TLDs nobody wants, at a registrar that's more expensive than 95 alternatives. They register in bulk — 10,000-17,000 per day — in patterns consistent with automated purchasing. And they pay with Bitcoin, which requires no identity verification.
These aren't customers. Customers use what they buy. These are transactions. The domain is not the product — the transaction is the product. The purpose of buying 585,000 dead domains per year is not to have 585,000 websites. It's to move money from point A (anonymous crypto wallet) to point B (NameSilo revenue line) and make it look like a legitimate business transaction.
Revenue per real domain — the smoking gun
* Dead-domain metrics in this report (same 5.18M dataset): 32.2% = no DNS/IP. 54.2% = provably dead/parked (no DNS + Sedo + CF parking + Shopify unconfigured). 55.7% = dead rate used for Namecheap-comparable baseline (no IP + no Majestic rank, 99.86% of NameSilo domains have zero rank). 81.5% = full economic analysis with HTTP probes, age, MX, content, patterns. Full breakdown · Rank data
NameSilo makes $20.34 per active domain. Namecheap makes $9.68. NameSilo generates 2.1x more revenue per real customer than Namecheap — while being a smaller, more expensive (for .com: $15.56 vs $6.99), less popular registrar with worse UX. How? Because the phantom domains aren't free. Someone is paying $8-10M/year for domains that generate zero value. That money inflates the revenue line while the "customer" gets nothing — because the customer doesn't exist, or the customer IS NameSilo.
Why we compare with Namecheap — and an apology to them
We want to be transparent about why Namecheap was chosen as the baseline, and to emphasize: this comparison is not intended to discredit Namecheap in any way. We used only publicly available data.
Why Namecheap specifically: Our initial research into NameSilo began from an anti-phishing report where both registrars appeared. What stood out were the shared characteristics: accessible API for bulk registration, cryptocurrency payments accepted, Arizona incorporation, and both among the top registrars by domain count. We wanted the closest possible comparison — same market segment, similar scale, similar features.
What we found: Namecheap is an example of how a registrar should handle abuse reports — responsive, transparent, and effective. The contrast with NameSilo's conduct only became more striking the deeper we looked. Namecheap's dead domain rate (32.2%) is within normal industry range. NameSilo's (81.5%) is not. We apologize to Namecheap for any inconvenience this comparison may cause — the data speaks in their favor.
Baseline Comparison
Domains Born Dead — NameSilo vs Namecheap
Same methodology, same data format. Namecheap (24M domains) as industry baseline. If NameSilo's dead domains were "normal" — the rates would match. They don't.
Namecheap (normal registrar)
Fresh: 26% dead
Mid-life: 38% dead
Mature: 32% dead
LOW → HIGHER → LOWER — normal lifecycle. Domains start alive, some die mid-life from abandoned projects, survivors stabilize.
NameSilo (anomaly)
Fresh: 56% dead
Mid-life: 59% dead
Mature: 46% dead
HIGH → HIGH → HIGH — flat across all ages. Domains are born dead and stay dead. The gap narrows with age only because older cohorts predate the 2024-2025 bulk ramp-up.
This is not "normal dead domain rates." We controlled for it. Even if you accept that every registrar has dead domains — NameSilo has 1.2 million MORE dead domains than you'd expect from a registrar this size. Those 1.2M excess dead domains generate $22M/year in fake revenue. That's not neglect — that's a 23 percentage-point gap above the baseline, concentrated in domains under 2 years old.
The killer stat: NameSilo's dead rate for domains under 30 days old is 59.5%. Namecheap's is 25.4%. At NameSilo, 6 out of 10 domains are dead within their first month of life. These domains were never intended to be websites. They were born dead. They exist only as revenue line items.
New domain registrations per year (all NameSilo)
1.5M new domains in 2025 (4,260/day) — 99%+ have no traffic. Growth correlates with spending on registry fees, not customer acquisition. This is not organic growth. This is a budget increase.
What Do These "Domains" Look Like?
We analyzed 1,669,111 dead domains from the 5.1M dataset. Here's what "customers" are buying:
The registration spike is not gradual growth — it's an explosion:
These are not domain names. These are transaction IDs. 0499777com06xl03.sbs is not a business. 000000004.xyz is not a brand. 1xbet-djjj.buzz is a gambling phishing domain. 378,547 gibberish names. 522,288 bought for exactly one year and abandoned. No real customer buys 02g740c6.sbs for $0.99, uses it for zero days, and lets it expire. This is automated purchasing with no human intent behind it — except the intent to move money.
C$65.5M revenue with 58 domains in the global top 10,000.
Namecheap has 24M domains and thousands in top-10K. GoDaddy has 80M+. NameSilo has 58.
Where is the money coming from? Not from the 58 real websites. Not from the 17,875 with measurable traffic.
$48M/year from a customer base that is 99.65% invisible.
And a final question: a company with C$65.5M revenue and C$133M market cap can't afford to update a UI that looks like Windows 98? Actually — in their Q3 2025 earnings release, NameSilo LLC CEO Kristaps Ronka admitted they "began a complete UX/UI overhaul using seven years of customer learning." Seven years. It took seven years of customers fleeing to Namecheap before someone noticed the panel looks like a GeoCities page from 1998. But here's what they did with the money instead of fixing UX: they acquired SewerVUE Technologies — a company that inspects sewer pipes with radar. A domain registrar that protects $100M theft operations and inspects sewage. You cannot make this up. See our faithful Win98 recreation of the NameSilo experience →
And then there's the parking IP problem.
Of the domains that DO have an IP address, 36.7% point to just 10 IP addresses — all parking/stub pages. The top IP alone (Sedo parking: 91.195.240.123) hosts 522,466 NameSilo domains. Another 646,381 domains sit on known parking infrastructure. These aren't websites. These are placeholder pages displaying generic ads.
So: 1,668,355 domains (32.2%) have no IP at all — completely dead. Of the 3.51M that DO resolve, 1,153,281 (33%) point to parking/stub IPs. Combined total: ~2,821,636 domains (54.4%) out of 5,179,405 are not real websites. More than half. And that's just DNS. Our full economic analysis—factoring in age, MX records, content, and registration patterns—puts the real dead rate at 81.5% (4,221,217 domains). Over $50M in phantom revenue.
The real active customer base of NameSilo is approximately 958,188 domains — not 5.18M as they claim. Their "top 10 registrar" status is built on phantom registrations. We're not the tax authority. But this is textbook money laundering infrastructure — anonymous buyers, cryptocurrency payments, zero activation, inflated revenue. FinCEN has issued guidance on exactly this pattern. Nobody is following it.
The operator phishes himself. Yes, really.
A note before we continue: many security colleagues wanted to join this investigation. We deliberately refused all help to protect them from retaliation. Every suppression attempt they make creates more evidence and another line on their criminal resume.
Now — the self-phishing scheme. When we presented our technical analysis, the operator's first response was: "you visited a phishing site." Yes. We know. His site IS the phishing site. But here's the twist: the operator creates phishing copies of his own scam site and then blames victims for visiting "phishing."
The active self-phish right now: xmrwallet.app — check the code yourself. The wallet creation logic and transaction handling is nearly identical to the main xmrwallet.com code. Across 10 years of "phishing" copies — xmrwallet.homes and others — the code structure is the same everywhere. Same processing logic. Same wallet generation. Only difference: the "phishing" copies don't encrypt. Because they're not really phishing copies made by attackers. They're the operator's own mirrors, designed to create plausible deniability: "oh, you must have used a phishing copy, not the real site."
And where were these self-phishing domains hosted? On njal.la — a NameSilo reseller. The same njal.la whose API NameSilo disabled. The same ecosystem. When the "blockchain syncing" excuse got debunked by the official Monero project, these geniuses pivoted to: "it's not us, it's phishing copies targeting us!" Except the phishing copies are hosted on their own partner's infrastructure, use the same code, and connect to the same DDoS-Guard / IQWeb backend.
The Russian-speaking scammer behind this is known in the community — check keplr.at and related domains. Same actor, same methodology, multiple sites. We always do public scans (we noticed they started using URLscan — but for users with a Pro subscription, everything is accessible). Compare the code of xmrwallet.app with xmrwallet.com. Compare the wallet creation flow. Compare the transaction handling. Then tell us again that one is "phishing" and the other is "legitimate."
To be precise: there is exactly one independent actor we identified who made actual phishing copies of xmrwallet — a known Russian-speaking scammer operating primarily on .at domains (keplr.at and similar), who phishes multiple crypto wallets. He created copies of xmrwallet as one of many targets. Every other "phishing copy" of xmrwallet over the past 10 years was created by the operator himself.
Why would a scammer phish his own scam? Two reasons. First: to create a narrative. "Look, people are making phishing copies of our legitimate service — we must be important, we must be real." It's reputation theater. A legitimate wallet gets phished. A scam wallet doesn't — unless the scammer does it himself. The self-phishing copies let the operator claim credibility he never had. Second: to deflect blame. When victims complain that their funds disappeared, the operator points to the "phishing copies" and says: "You must have used a fake site, not ours." The victim blames the phishers. The operator keeps stealing. The registrar nods along. Everyone wins — except the people losing their money.
The xmrwallet.homes, xmrwallet.app, and dozens of other "phishing copies" that the operator conveniently blames — all trace back to the same origin. Same code. Same logic. Same hosting. Same operator playing both sides. The only real phishing actor (keplr.at) simply copied what was already a scam. Everyone else who got blamed for "phishing xmrwallet" was the operator himself, running mirrors of his own theft operation and pretending they were attacks.
Self-phishing through your own reseller network, blaming victims for your own mirror infrastructure, while your registrar helps you clean VirusTotal detections. This isn't a scam anymore. This is an industrial operation.
This is the admin panel of a company that people trust with their businesses. Look at the design. Look at the UI. Does this look like a modern, well-funded technology company? Or does it look like something built by the same person who orders SEO articles on Kwork for 500 rubles?
Now compare it to fd.nic.ru — a Russian registrar. Remarkably similar aesthetic, isn't it? Same era, same design philosophy, same target audience.
NameSilo claims to manage 6.26 million domains. Our analysis of 5.18 million shows 81.5% are dead — 4.22 million domains with no website, no email, no purpose. Bulk domain registration at scale with anonymous Bitcoin payment and zero activation is not a business model.
The Forbes Advisor Article — A Case Study in Purchased Legitimacy
Forbes Advisor published a "review" of NameSilo ("Audited & Verified: May 6, 2024"). It contains the affiliate disclosure: "We earn a commission from partner links." The article recommends NameSilo as the "best registrar for low-cost domains." Let's fact-check it against reality:
Forbes also includes this disclaimer: "Information may have changed since publication. Past performance is not indicative of future results." and "Forbes Advisor adheres to strict editorial integrity standards."
"Editorial integrity" that recommends a registrar as "best for low-cost .com" when 95 registrars are cheaper. That says "24/7 support" when the site shows business hours. That compares with a dead competitor. That shows fake screenshots of a panel that doesn't exist. Same playbook as Kwork SEO articles — different budget, same result. A $500 Kwork article and a Forbes Advisor "review" serve the same purpose: purchased legitimacy.
And it doesn't stop at Forbes. NameSilo's "news" on Yahoo Finance carries this label: "This is a paid press release." Every "article" about NameSilo in financial media is purchased. The Forbes review. The Yahoo Finance press releases. The Trustpilot ratings. The Wikipedia page (flagged as promotional). There is no organic positive coverage of NameSilo. It is all bought.
FTC Warning Letter — December 20, 2024
The U.S. Federal Trade Commission sent NameSilo an official warning letter on December 20, 2024, signed by Lois C. Greisman (Associate Director, Bureau of Consumer Protection, Division of Marketing Practices). The letter states:
Think about what this means: a federal agency had to send an official letter to get NameSilo to act on a domain impersonating the FTC itself. Not a random phishing site. Not a crypto drainer. A domain pretending to be the Federal Trade Commission. If even the FTC needs to send formal correspondence to get a phishing domain removed — what chance does a regular victim have? The answer: none. Read the full FTC letter (PDF) →
BBB Complaints — Pattern of Abuse Denial
NameSilo's Better Business Bureau page contains complaints from real victims. A pattern emerges: victims report phishing domains, NameSilo deflects:
Victim complaint (BBB):
"NameSilo did not remove the domain that was proven to be used for phishing and allowed it to continue impersonating our company. Their phishing abuse form does not work. When I tried emailing them, they only had an auto-responder. We filed a complaint with ICANN since their abuse reporting system is essentially non-functional. We are considering filing a lawsuit under ACPA."
NameSilo response (March 18, 2024):
"We cannot confirm phishing — it appears to be SPAM. As a domain name registrar, we do not have any control over the content of emails... It is too easy to spoof domain names for us to investigate complaints."
Translation: "We can't confirm phishing" (we won't look). "We don't control email content" (not our problem). "Too easy to spoof" (we won't investigate). This is the same playbook we documented with xmrwallet — deflect, minimize, refuse. The difference: these aren't our reports. These are real businesses, filing on the BBB, getting the same non-answers. Read all BBB complaints →
Trustpilot — Bot Farms Competing with Bot Farms
NameSilo's Trustpilot rating looks impressive — until you think about it. Their real customer base is ~958K active domains. How many of those customers would voluntarily write a glowing review of a registrar with a Win98 admin panel, $15.56 .com pricing (#96/130), and support that responds to phishing reports with "we can't confirm phishing"?
The pattern is complete:
We tested Trustpilot ourselves. We left a 3-star review for NiceNIC — not even negative, just honest. No profanity, no accusations, just facts. Deleted after one complaint. A verified account. A real review. Gone. Meanwhile, NameSilo's page is full of suspiciously enthusiastic 5-star reviews from accounts with US geolocation — because the geo matters. American reviewers = "look, real American customers buy our domains" (not "we launder stolen crypto by buying domains from ourselves"). The reviews serve the same purpose as the phantom domains: creating the appearance of a legitimate American customer base that does not exist.
Example: "Patty Johnson" (Trustpilot profile) — US-based, 2 reviews total. One 5-star review for NameSilo (Jan 2026): "Leonid was very helpful... 5 stars!" The other review? For Otrium — a company with reviews alleging fraud and stolen money. One bot account writing for two different scam-adjacent businesses. And the reviews share a pattern: they name specific support agents ("Leonid"), praise response time, and read like templated customer service surveys — not like someone who just bought a $10 domain. Real domain buyers review prices and panel UX. Bot reviews praise "Leonid."
TRUSTPILOT DATA ANALYSIS — 2,280 NameSilo vs 2,480 Namecheap reviews
We understand the support obsession, by the way. Have you seen their admin panel? (we recreated it). With that interface, we'd need support too — or an ambulance. Half the functions don't work, the UI hasn't had a major overhaul in years, and the CEO himself admitted it needs a "complete UX overhaul" after seven years of promises. So yes: if you somehow became a NameSilo customer, you would indeed contact support. Constantly. Because nothing works without it.
But here's the tell: real frustrated users write about how terrible the interface is. That's what the 1-star reviews say — broken DNS, locked accounts, suspended domains, phishing reports ignored. Real pain, real detail, 265 characters average. The 5-star reviews? "Great support! Leonid helped. 5 stars." — 84 characters median. Real users complain about the product. Fake users praise the people.
And about those people — Leonid appeared from nowhere on April 13, 2025. Zero mentions before. Then 65 reviews in his first two months. That's not a popular support agent. That's a KPI. The timing coincides exactly with our investigation going public. The pattern is clear: investigation starts → negative coverage appears → bot farm activates → "Leonid was amazing!" fills the page. May 2025: 106 reviews (5x normal), 95% five-star, zero one-star. Not one unhappy customer in 106 reviews. For a registrar ranked #96 in .com pricing with a panel from 1998.
And the reviews themselves? 43% are under 80 characters. Four have the title just "Leonid" — nothing else. Three more: "Leonid was very helpful." That's it. 52% US geo. Among the reviewers: "Satoshi Nakamoto" (yes, really), "Author" (didn't even pick a name), "Виктор -" and "Anna Koroleva" (Russian names on a US-targeted registrar), "Boris Martin" and "Andrei Dobrescu" (Eastern European), all mixed with "Brad", "LaToya", "Patty Johnson." Someone is writing reviews in bulk and cycling through a name generator that can't decide which continent to pretend to be from. The name Leonid itself is Russian — which fits the pattern perfectly. A Russian-named support agent praised by Russian-named bot accounts on a registrar with FSB connections and xmrwallet ties. At this point, the question isn't whether these reviews are fake. The question is whether Leonid is a real person or a character in a script.
The Hong Kong anomaly — and the phantom Chinese customer base
Hong Kong: 57 reviews. 57 out of 57 are five-star. 100%. Zero four-star. Zero three-star. Zero anything else. 91% single-review accounts. Over 7 years. Statistically impossible for any real customer base. China: 94% five-star, 80% single-review, 84% no avatar. Singapore: 95% five-star, 85% single-review. Combined: 168 reviews from Chinese-speaking markets — almost entirely fabricated.
And the names? "Mihai" and "Jesse Barrett" reviewing from Hong Kong. "Franck" from mainland China. Mixed with 陈旭, 幽羽千葉, and zhanglili. A bot farm that couldn't decide whether to use Chinese or Western names — so it used both.
Why China? Because NameSilo actively markets there: namesilo-china.com, bcbay.com/namesilo, paid Chinese blog posts, and even a Chinese Wikipedia article. When investigators ask "who buys 4.22 million dead domains?", NameSilo will point to China. Be ready for phantom Chinese customers. The Trustpilot data shows they've been building this alibi since 2019 — 57 perfect reviews from Hong Kong, one at a time, spread over years. Patient. Deliberate. And 100% fabricated.
Independent AI Forensic Analysis — 2,480 vs 2,480 reviews
We scraped 2,480 NameSilo and 2,480 Namecheap Trustpilot reviews and submitted them to an independent Claude API analysis, anonymized as "Company A" and "Company B." The AI had no knowledge of which company was which. Its conclusions:
From the AI report: "Company A exhibits extensive, multi-dimensional evidence of systematic review manipulation through coordinated artificial generation. The probability of these patterns occurring organically approaches zero."
xmrwallet.com Trustpilot — The Scam Site's Own Reviews
We scraped all 80 reviews from xmrwallet.com's Trustpilot page. Wayback Machine snapshots exist on ca.trustpilot.com/review/xmrwallet.com. Our scrape captures the full dataset including review text, ratings, dates, and user metadata.
80
total reviews
51%
5-star (41)
22%
1-star victims (18)
99%
reply rate (79/80)
70%
1-review accounts
0
users also reviewed NameSilo
Operator reply patterns: 8x "thank you!", 7x "thanks!", 5x "clone/phishing site" deflection. The operator actively maintains 99% reply rate to boost Trustpilot TrustScore — while actual victims report stolen funds since 2020.
Victim Lee Davis (2022) mentions emailing "owner Nathalie Roy herself" — confirming the domain registrant identity directly from a Trustpilot review.
Cross-reference: Zero user overlap between xmrwallet and NameSilo reviewers. Different bot farms, same playbook: flood with short 5-star reviews from 1-review accounts to drown out real victims.
Full dataset: Browse Reviews (JSON) — SHA-256: cf159a47...
Everything is self-referential. The domains inflate the revenue. The revenue funds the articles. The articles build the Trustpilot. The Trustpilot convinces investors. The investors fund the stock price. The stock price justifies the acquisitions. The acquisitions launder the money. And 81.5% of it is built on domains that nobody uses, reviews that nobody wrote, and articles that nobody commissioned organically. It's turtles all the way down — and every turtle is NameSilo.
Domain Registration Anomaly Report — 130M+ domains analyzed
We analyzed 5.1 million NameSilo domains against 7 other registrars (130M+ total). 32.2% of NameSilo domains are dead — never activated, no IP, no email, no web presence. Industry baseline: 15-21%. That's $12 million spent on domains that were never used. Dead registrations spiked 7x between 2023 and 2024. Bulk registration runs of 10,000-17,000 domains/day throughout 2025. Disproportionate use of junk TLDs (.sbs, .cfd, .xyz). 96% of domains have no contact email. Consistent with money laundering, self-dealing, or systematic revenue inflation.
For context: NameSilo Technologies Corp. (CSE: URL, OTC: URLOF) has a market cap of C$133M (~US$98M), revenue of C$65.5M, and a net margin of 1.7%. They trade at P/E 143.8x vs industry average 21x. A company valued at C$133M is protecting a $100M+ theft operation. The math doesn't add up — unless the theft operation IS part of the business model.
Corporate structure — public record:
NameSilo Technologies Corp. — parent company. Incorporated in British Columbia, Canada. Listed on the Canadian Securities Exchange (CSE: URL). Also trades OTC in the US as URLOF. Subject to Canadian securities regulation (BCSC).
NameSilo, LLC — operating subsidiary. Registered in Phoenix, Arizona, USA. ICANN-accredited registrar, IANA ID #1479. Subject to US law, ICANN RAA, and Arizona state jurisdiction.
This means two regulatory jurisdictions have authority: Canadian securities regulators (BCSC/OSC) over the parent company and its stock, and US authorities (FBI, DOJ, Arizona AG, FinCEN) over the operating entity. Neither has acted.
PrivacyGuardian.org — NameSilo's built-in scam shield
PhishDestroy scan of NameSilo's WHOIS privacy service — April 2026
PrivacyGuardian.org is not a third-party service. It is owned and operated by NameSilo. Every domain that uses PrivacyGuardian has its registrant email replaced with a pw-{hex}@privacyguardian.org address — making the real owner invisible to abuse reporters, law enforcement, and victims. Privacy is legitimate. Using your own privacy service to shield 109,000+ malicious domains from identification is not privacy — it's infrastructure for fraud.
How we got these numbers: We extracted 4,974,265 candidate domains from the NameSilo customer dataset by matching PrivacyGuardian.org WHOIS markers. We then validated each domain via RDAP against rdap.namesilo.com. Of those validated, 109,195 were HARD confirmed as PrivacyGuardian-protected. We cross-referenced the full list against Spamhaus DBL, SURBL, PhishTank, PhishingArmy, CERT-PL, AlienVault OTX, Hagezi, uBlock, AdGuard, ThreatFox, and our own internal blocklist of 130K+ domains.
Top blocklist sources
What these domains do
Top TLDs (malicious PG domains)
Same junk TLD profile as the dead domain analysis. .sbs, .cfd, .xyz, .top — the same abuse-prone TLDs dominate both datasets.
Top targeted brands
Ledger, Coinbase, OKX, Ethereum — real financial brands being impersonated through NameSilo's own privacy service.
Hosting geography (malicious PG domains)
VirusTotal breakdown
The bottom line: NameSilo operates its own WHOIS privacy service. That service shields 109,000+ confirmed malicious domains from identification. These domains impersonate Coinbase, Ledger, OKX, Ethereum, Google, and dozens of other brands. They run Angel Drainer, Solana Drainer, and wallet-connect phishing at industrial scale. 77,522 of them are flagged by Spamhaus. And NameSilo — the ICANN-accredited registrar that operates PrivacyGuardian — tells every abuse reporter: "As an ICANN-accredited registrar..."
This is not negligence. This is a business model. The privacy service exists to make abuse reporting harder. The junk TLDs exist because they're cheap and disposable. The dead domains exist to inflate revenue. And the ICANN accreditation exists to wave at anyone who asks questions. 109,000 malicious domains protected by your own service, NameSilo. How many more do you need before someone calls this what it is?
Let's be clear about what we're looking at. These are not sophisticated actors. The operational pattern is identical to hundreds of Russian-origin scam operations that pay kickbacks to FSB-adjacent structures for protection — the only difference is the scale and the fact that they're hiding behind a US-incorporated company in Arizona instead of a Belize shell. The logic is the same: steal, suppress, buy reputation, delete evidence, threaten researchers, and rely on institutional inertia to never face consequences. They got comfortable because it worked for 10 years. It's not going to work for the 11th.
abuse@phishdestroy.io — we share what we know with any victim, investigator, or prosecutor.
Drive owner: hassizabir@gmail.com (last modified Oct 2023)
Exhibit — Operator's Farewell Letter
The operator ran. The site is still live. NameSilo still hasn't suspended the domain.
On May 5, 2026, the xmrwallet operator posted a farewell letter on the site and GitHub repository — announcing complete closure. He signed it "The Creator of xmrwallet.com" without using his real name. This letter is direct evidence: it proves the operator was aware of the investigation, it contains verifiable lies about the theft mechanism, and it confirms the site was operated by a single individual from 2018 to 2026. We saved a copy immediately. As of today, the domain xmrwallet.com is still active and NameSilo still has not suspended it.
Lie #1 — "View key cannot give access to spend your funds"
"A view key does not, and cannot, give the service access to spend your funds."
Reality: The theft mechanism does not use the view key to spend. It uses session_key exfiltration — the wallet address and private view key are base64-encoded into a session identifier, sent to the server, where the server constructs its own transaction using 8 PHP endpoints. The operator knows this because he wrote the code. He is deliberately misdirecting victims toward a view-key debate while the actual exploit is server-side transaction hijacking. This is consciousness of guilt.
Lie #2 — "Unfunded" and "cannot afford server costs"
"This project is unfunded and maintained in my spare time, I simply cannot afford the server costs."
Reality: The operator stole an estimated $100M+ in Monero over 8 years. Server hosting on DDoS-Guard costs ~$550/month. He pre-paid 5-10 year domain registrations across 6+ registrars. He purchased 50+ SEO articles, social media spam packages, and maintained multiple mirror domains simultaneously. The "unfunded volunteer" narrative is for victims who don't read the technical evidence.
Admission — "The person who attacked us"
"We have recently been the target of sustained attacks... The person who attacked us did so under the accusation that our service requires a view key."
What this confirms: The operator acknowledges PhishDestroy's investigation forced the closure. He frames security research as "attacks." He does not deny any specific finding. He does not produce counter-evidence. He redirects to the view-key strawman. An innocent operator would publish the server logs proving no theft occurred. He didn't.
Evidence value — "Thank you to everyone who sent donations"
"A special and sincere thank you to everyone who sent donations throughout the years. Your immense generosity is what kept the servers running."
For investigators: The operator claims donations funded the servers. This is falsifiable. Subpoena the donation address transaction history. Compare total received donations vs. total funds that "disappeared" from user wallets. The gap between those numbers is the theft volume. The operator just told you where to look.
Captured from xmrwallet.com on May 5, 2026. The letter was published as the site's index page. We archived the complete HTML including all CSS, scripts, and metadata. The operator signed as "The Creator of xmrwallet.com" — not as "Nathalie Roy", not by any name. But the email headers from February say N.R. And the WHOIS records say the rest.
Why did he "leave"? Not guilt. Evidence destruction.
The operator — who registered under the name "Nathalie Roy" (a woman's name; we documented the operator's Kwork SEO orders and freelance activity — nicknamed "SEO Grandpa" based on his SEO spam campaigns) — did not shut down out of remorse. He redirected the xmrwallet.com domain to GitHub Pages, where the farewell letter is now hosted. This is not a shutdown. This is a calculated move to:
1. Erase URLscan evidence. When the domain points to GitHub Pages, previous URLscan scans of the malicious site become stale. New scans show a benign GitHub-hosted page. The forensic record of what the site actually did — the 8 PHP endpoints, the session_key exfiltration, the server-side TX hijacking — gets buried under clean scans of a static farewell letter.
2. Automatically reduce VirusTotal detections. When security vendors re-scan xmrwallet.com and see a GitHub Pages site instead of a malware-laden wallet, they remove their detections. The operator has been filing regular VT appeals and re-scan requests — we observed this pattern. Each re-scan with the domain pointing to GitHub lowers the detection count. This is exactly what NameSilo promised to help with: "working with the registrant to remove the website from VT reports." They found a way.
3. NameSilo got nervous. The ICANN filing, the law enforcement referral, the public exposure with 11K views — and then US authorities apparently started asking questions. The farewell letter appeared shortly after. Coincidence? The operator didn't suddenly develop a conscience after nearly a decade and $100M. Someone told him to cool down. Someone with a vested interest in making the problem go away quietly.
4. The DNS history confirms this was deliberate — and clumsy. The domain xmrwallet.com was never pointed to GitHub before this. For years it resolved to DDoS-Guard/IQWeb infrastructure — the real scam backend. The redirect to GitHub Pages was recent, intentional, and it took the operator 3 attempts to get the DNS configuration right. A "developer" who built a "sophisticated open-source wallet" needed three tries to set up a GitHub Pages CNAME. This level of technical skill is consistent with everything else about this operation. These are not sophisticated actors. They are persistent ones.
The "farewell" is not an exit. It's a cleanup operation. The domain is still registered. The DNS is still active. The operator is still out there. And the evidence destruction is ongoing — every day the domain points to GitHub, another security vendor removes their detection. This is why we archived everything before they could erase it.
Exhibit — Suppressed Social Media Evidence
@Phish_Destroy — 26 tweets that got us silenced
Every tweet posted by @Phish_Destroy was screenshotted and archived before the account was locked via X Gold Checkmark corporate support. These 26 screenshots are the complete record of our public communication about xmrwallet and NameSilo. X/Twitter deleted the originals. We kept the receipts.
For investigators: Request X/Twitter's deletion logs for @Phish_Destroy. Compare what was removed vs. what survived. Cross-reference with the timestamps in these screenshots. Every moderator action has a paper trail. The reports that triggered the lock were filed by NameSilo or the operator — request the reporter identity.
Click any screenshot to view full size. All 26 images are part of the IPFS archive. Original posts were deleted from X/Twitter after Gold Checkmark corporate intervention — these are the only surviving copies outside of X's own servers.
Exhibit — xmrwallet Victim & Technical Evidence
Additional Evidence Screenshots
Victim theft reports, deleted GitHub issues, DNS infrastructure maps, VirusTotal detections, and the operator's CIS-origin indicators. All SHA-256 verified in ALL_EVIDENCE_HASHES.txt.
The operator's entire strategy depends on victims giving up after being silenced. This section is for those who refuse.
We know it feels hopeless. Monero is private. Your money seems gone. They deleted your reviews, your posts, your warnings. They want you to believe there's nothing you can do. That's not true.
The operator's power was making victims disappear. This archive makes that impossible.
Direct Addresses — To Those Who Enabled This
You deleted verified victim reviews and kept bot reviews. You enabled a scam wallet to maintain a rating higher than legitimate cryptocurrency exchanges. A verified user, green checkmark, unprompted review, reporting stolen funds — "I'm in a panic, I created a wallet on the official site, put money in and the developers took everything" — deleted as "breaching Trustpilot's Guidelines for Reviewers."
A victim reporting theft is a guideline breach. A bot writing "Leonid was very helpful" is not. We have Wayback Machine proof of 129 NameSilo reviews and 7+ xmrwallet reviews erased from your platform. We have more surprises that will show your role in enabling this fraud. Stop deleting victim reports. Start deleting bot reviews.
You recommended xmrwallet.com to users as a legitimate Monero wallet. People trusted your recommendation. People lost money. That recommendation generated revenue for a theft operation and enabled laundering. We have the screenshots. Fix it.
Every time you delete, we publish. Every time you threaten, we archive. Every time you lie, we release the next layer. We would genuinely love to interview one of these operators after an arrest. Until then, we document. And we do not stop.
"Feel free to dismiss all of this. We've been dismissed before — usually right before we turned out to be correct."
Specialists in CIS-origin scam operations. Hundreds of phishing sites shut down. The patterns here — DDoS-Guard, Kwork orders, SEO burial, suppression playbook — are a recognizable operational signature.
There is a direct connection between the operator and the registrar beyond a standard client relationship. The operator invited us to prove he was a thief. We did. Then they tried to erase us.
First public estimate: $20M+. As victims contacted us directly and EU law enforcement shared findings, the real figure became clear: very likely north of $100 million. We use the conservative number publicly. But we know.
Every suppression attempt is traceable. Subpoena Trustpilot (100+ deleted reviews) and GitHub (21+ deleted issues). The suppression campaign is evidence of the operation.
To the victims who lost their Monero over the last decade:
This archive exists for you. The operator is identified. The registrar is on record. Criminal cases are open in Europe. You are not alone and you are not powerless.
Every file is SHA-256 fingerprinted at capture time. Any byte changed = hash mismatch = tampering detected. This is a court-grade evidence chain.
61 Evidence Images — Complete Breakdown
16 Primary Screenshots
Operator emails, NameSilo tweet (4 contradictions), @Phish_Destroy rebuttals, X Support "no violation", GhostArchive copies, VT delisting evidence. All in evidence/
11 Additional Screenshots
Victim reports (BitcoinTalk, bits.media), deleted GitHub Issues #13/#15/#35, DNS infrastructure maps, VirusTotal, Trustpilot, operator taunts. All in screenshots/
26 Tweet Screenshots
Complete @Phish_Destroy archive. Every tweet captured before Gold Checkmark lock. The posts X/Twitter tried to erase. All in tweets/
How to verify integrity
Download any file from this archive. Run sha256sum <filename> and compare the output against the hash shown here or in ALL_EVIDENCE_HASHES.txt. If any hash doesn't match, the file was tampered with after publication. All hashes were generated at the time of capture — before any party could modify the originals. Report any mismatch to abuse@phishdestroy.io.
Every repository, every page, every screenshot. GitHub goes down, domains get seized, accounts get locked — it's all still here.
Real-time phishing & scam domain blocklist. 130,000+ curated threats. Plain text, hosts, AdBlock Plus, dnsmasq. Threat intelligence API. All raw data included.
The registrar's tweet, operator emails, X Support contradictions, SHA-256 verified screenshots, full technical breakdown. Filed with ICANN and law enforcement.
Private key theft, server-side TX hijacking, 8 PHP endpoints, Google Analytics tracking. Deleted GitHub Issues #35 & #36 — cached copies included.
Scam operator infrastructure analysis. Phishing kits, panel configs, affiliate networks, crypto drainer source code. Raw intelligence.
Arweave (on-chain, permanent, 5 deploys) + IPFS (ENS domain, decentralized) + GitHub/Codeberg (version-controlled, forkable). Cannot be deleted, modified, or censored. Every copy is a full standalone archive — 723+ files, 10 languages, all evidence.
arweave.net with ar-io.dev or arweave.developerdao.com. Same data, different operators. If one is down, the others work.bafybeihyw6jz5p4dqxadj756oew7rhzt6kq7tljrzxygpnnwdc5aq3aq6iipfs pin add bafybeihyw6jz5p4dqxadj756oew7rhzt6kq7tljrzxygpnnwdc5aq3aq6igit clone https://github.com/phishdestroy/namesilo-evidence.gitArweave: permanent on-chain storage. IPFS: decentralized, pinned via ENS. GitHub/Codeberg: version-controlled, forkable. Every copy is a full standalone archive.
Full directory of this IPFS archive. Every page, every document, every piece of evidence — linked and described.
Machine-readable datasets for investigators, journalists, and forensic analysts. Every file is SHA-256 verified. Download everything — check our work.
Complete NameSilo registrar dump: domain URL, registration/expiry dates, Majestic rank, contact email, phone, IP address, geolocation. The dataset behind the anomaly report.
Download CSV.GZ ↓SHA-256 hashes for all 61 evidence screenshots (16 primary + 19 additional + 26 tweets). Generated at capture time — any mismatch = tampering.
Download Hashes ↓Complete mirror of external evidence: Reddit threads, Wayback Machine snapshots, VirusTotal reports, URLscan results, Trustpilot reviews, SecurityTrails DNS history. Saved before deletion pressure.
SHA256SUMS ↓Complete A/NS/MX/TXT/CNAME history, RDAP live status, subdomains, associated domains. Proves: Namecheap(2014) → DigitalOcean(2018) → Cloudflare(2021) → DDoS-Guard(2024) → GitHub Pages(2026).
Browse JSONs ↓Scan results for xmrwallet.com and .app. Transaction logs, DOM snapshots, link analysis. API JSON with full HTTP headers, certificates, and resource hashes.
Browse Scans ↓Detection, details, relations, community tabs for every xmrwallet domain (.com, .app, .cc, .biz, .me, .net, .homes) plus njal.la and associated IPs.
Browse VT ↓ICANN complaint, evidence report, victim advisory, deleted evidence timeline. Formatted for legal proceedings.
Browse PDFs ↓8-registrar comparison: dead domain rates, TLD profiles, IP concentration, cost analysis. NameSilo at 32.2% dead vs 15-21% baseline. $50M+ phantom revenue from dead registrations.
Read Report ↓Complete list of Twitter/X bot posts promoting xmrwallet. Three waves: 2018 Kwork batch, 2023 Google Drive match, 2025-2026 still active. All live, none removed.
Download URLs ↓How xmrwallet.com infiltrated AI recommendations: sponsored listicles (crypto.news, guru99, hackr.io), PBN for SERP ranking, Google Sites/GCS spam, Trustpilot farming, darknet promotion. Traffic analysis for both xmrwallet (640/mo, 70-80% spam links) and NameSilo (260K/mo, 43% unexplained Korean traffic, 95% spam backlinks). Operator identity, infrastructure IPs, satellite domains. NameSilo cross-analysis: 3/4 registrars suspended, NameSilo only one that defended.
Read Full Analysis →Complete SEO manipulation analysis: 50+ blogspot PBN, strategydriven.com exploit (4,125 injected links = 43% of backlink profile), Google Sites spam, typosquats, darknet promotion, SERP suppression analysis, Korea traffic anomaly. Includes full referring domain table (1,262) and backlink table (1,827) with filters.
Open Full Report →Structured data: PBN domains, manipulation networks, anchor distribution, operator identifiers, satellite domains, risk assessment.
Download JSON ↓Dead PBN clusters on Hetzner DE (IP 168.119.205.26), French cluster (IP 62.84.182.75), automated blogspot pattern. Link infrastructure dismantled Nov-Dec 2025.
Download JSON ↓Complete xmrwallet.com backlink profile. 70-80% spam. Distributed across blogspot PBN, WordPress, Weebly, Google Sites. Anchor text analysis reveals over-optimized "xmr wallet" pattern.
Download CSV ↓All referring domains. Only 15-20 legitimate. Rest: PBN, spam, satellite domains, darknet links (t.me/darksidelinks), neocities CONWAY directories.
Download CSV ↓sha256sum -c SHA256SUMS.txt — run this on any downloaded directory. Every file's integrity is independently verifiable. If a hash doesn't match, the file was tampered with after publication. Open an issue or contact abuse@phishdestroy.io.
PhishDestroy respectfully requests federal investigation into NameSilo, LLC (IANA #1479, Phoenix AZ) and the operator of xmrwallet.com for potential violations of the following federal statutes:
Recommended investigative steps:
1. Subpoena NameSilo's payment records for 585,000 dead domains (2025). Identify BTC wallet sources.
2. Engage Chainalysis/Elliptic to trace BTC payments to XMR-BTC swap origins.
3. Subpoena NameSilo's abuse ticket system — compare to public claim of "no abuse reports received."
4. Subpoena Trustpilot for full deletion log (both entities) — who requested deletions, from which IP/accounts.
5. Request CSE/OSC review of NameSilo Technologies Corp (URL.CN) for securities fraud — phantom domain revenue not disclosed as risk factor.
Contact for official inquiries:
Email: legal@phishdestroy.io (law enforcement & legal inquiries)
General: abuse@phishdestroy.io (PGP available)
All 61 SHA-256 verified exhibits, raw datasets, operator communications, OSINT analysis, and additional unpublished victim evidence available upon formal request.
We are prepared to provide testimony, technical analysis, and full cooperation with any authorized investigation.
phishdestroy.io
github.com/phishdestroy
codeberg.org/phishdestroy
phishdestroy.eth
phishdestroy.medium.com
@PhishDestroy
mastodon.social/@phishdestroy
abuse@phishdestroy.io
report@phishdestroy.io
legal@phishdestroy.io