We don't get paid. We risk real consequences from cornered criminals with money. This page explains why we chose this fight, what we're trying to prove, and how we designed this investigation.
Independence & Capability
We operate independently. No corporate sponsors, no grants, no financial leverage to exploit. This autonomy allows us to pursue targets that traditional security firms avoid due to liability or conflict of interest. 130,000+ phishing domains neutralized. Years of active operations. We understand scam infrastructure, operator behavior under pressure, platform abuse report processing, and suppression campaign mechanics.
How the investigation was triggered
The operator ("Nathalie Roy") was warned directly: don't lie, don't escalate. She had multiple opportunities to quietly remediate — delete two GitHub issues and walk away. If no victims complained, the matter would have ended there. Instead, she chose to threaten, lie, and involve her registrar. NameSilo then published a tweet containing 4 independently falsifiable statements, publicly defending a VirusTotal-flagged drainer to an audience of 11,000. That tactical error triggered a full-scale forensic operation.
Our objective is in our name: PhishDestroy. NameSilo chose to become part of the phishing operation — by defending it, by publishing false statements, by suppressing evidence. The response is procedural: document the protection, neutralize the scam, refer to law enforcement.
One of our researchers is writing a forensic research paper on online fraud criminology. This investigation is the primary case study. The paper develops a methodology for investigating theft of untraceable cryptocurrency (Monero) — where traditional blockchain analysis is impossible.
Monero has no public ledger. You cannot prove theft through blockchain analysis. No Etherscan, no transaction trail, no wallet attribution. This is why xmrwallet.com survived for a decade — nobody could quantify the damage using standard tools. The paper demonstrates that when you can't follow the money, you can still prove the crime through:
This investigation is the proof of concept that the method works. Every piece of evidence collected here — the suppression patterns, the identical behavior, the CAPTCHA response, the 21 million logged entries — feeds directly into the paper. The case needed to exist for the research to exist. Their arrogance made it possible.
Operational Methodology & Counter-Measures
We predicted every action they would take. We deliberately didn't write on Twitter that we know what they do to people like us — because they're so arrogant they didn't realize they weren't suppressing us. They were doing exactly what we wanted.
Parallel tracks, simultaneously:
Did we bait them? No. We did what we always do — reported abuse, published findings, documented responses. They chose to suppress. We just knew they would, and we were recording.
We submitted 11-12 formal abuse complaints to NameSilo — not to trick them, but to test our hypothesis. If they were truly independent of the operator, they would investigate a site flagged by VirusTotal, with documented victims, with the operator's own emails admitting control. They ignored every single one. Every other registrar we tested took action.
Multi-Platform Distribution & Suppression Tracing
We published on multiple platforms deliberately. Medium, dev.to, our own site. Not because we couldn't put it in one place — but because we needed them to suppress it on each platform separately. Every suppression action is logged by the receiving platform — requester identity, IP, timestamp, method. All platform records are available to law enforcement via standard legal process.
Medium article — 304 claps, 15 comments, 19 min read. One of multiple platforms we published on deliberately.
Honeytokens & Suppression Decoys
We didn't "bait" them. We did exactly what any anti-phishing researcher does: we published findings, reported abuse, and documented responses. They chose to suppress instead of respond. We anticipated that they would — because that's the pattern of every operator we've studied. The difference is that this time, someone was watching and recording.
We have no interest in slandering NameSilo. We don't care about their stock price. We posted one tweet — to catch a reaction. And we did: one of their investors attempted to doxx a researcher, then deleted the tweets. NameSilo responded with the same template answer that proved their primitive, predictable behavior — identical to the operator's. Our goal is in our name: PhishDestroy. We destroy phishing. That's it.
We sacrificed our Twitter account — 200K+ tweets, years of evidence — because the investigation required it. We hope the process will restore everything that was suppressed, because every deleted tweet, every removed link, every deindexed article is itself evidence subject to verification. Every platform they suppressed us on keeps records. For a decade they successfully erased everything negative from search results — our SEO analysis proves this. They left only what was convenient for them.
We published two articles on Medium. Article #1 mentioned only xmrwallet — no mention of NameSilo. Article #2 was specifically SEO-targeted at NameSilo. Both were deindexed. On our own site — same thing: content about xmrwallet only, and content about NameSilo specifically. Over 20 links per keyword, all suppressed. If NameSilo and the operator are unrelated — who is cleaning NameSilo's search results? The operator cleaning his registrar's reputation? That's not how unrelated entities work.
Every analysis we published included an alert about the registrar and the truth about their conduct. They didn't like it. But what they see as a "battle" — our posts vs their takedowns — was never a battle. It was a planned operation. Each placement was designed with one purpose: to make them create evidence against themselves. They think they were responding to attacks. They were responding to bait. Every takedown request, every deindexing, every DMCA — evidence they manufactured against themselves.
Monero is untraceable. There is no blockchain trail. Traditional investigation methods don't work here. So we adapted: if we can't follow the money, we follow the behavior. We became the target so they would demonstrate the pattern. A hunter doesn't chase untraceable prey through the forest — he sets traps and waits. They walked into every single one.
Decentralized Infrastructure & Risk Mitigation
Because we're not one person. 4+ researchers worked on this investigation. Victims contributed. Law enforcement in multiple countries has been briefed. The evidence is on IPFS — immutable, decentralized, with automated monitoring. If any mirror goes down, a new one deploys automatically.
They think deleting links makes evidence disappear. It doesn't. It creates more evidence. Every deletion is logged. Every suppression attempt is another exhibit in the case file.
dev.to publication — cross-posted to create multiple suppression records across platforms.
Operator Threat Assessment
The operator emailed us: "I hired a lawyer and a PI." No lawyer appeared. No PI appeared. What did appear: DMCA takedowns, mass-reports, DDoS attacks from njal.la (a NameSilo reseller), and coordinated Trustpilot manipulation. Every threat, every action, every timestamp — documented.
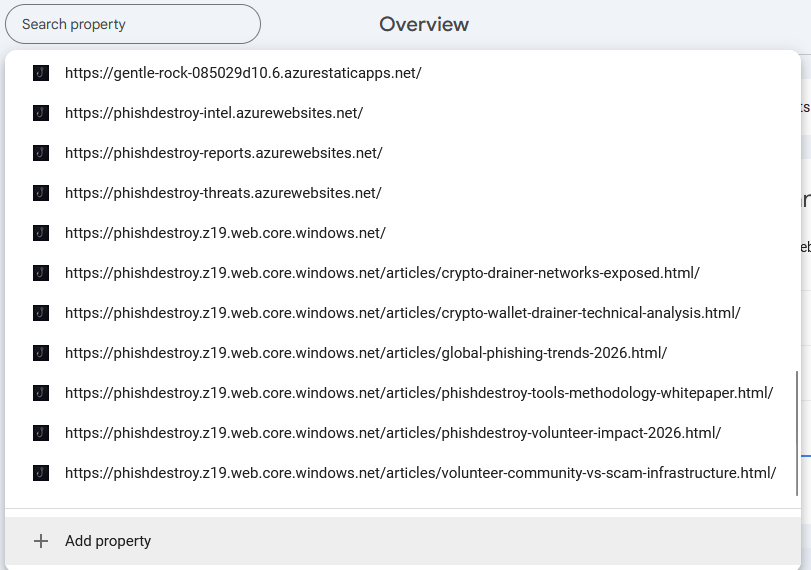
Google Search Console — every domain you see here was created with one purpose: to be taken down. And they were. Every single one.
Look at that screenshot. Every Azure subdomain, every article URL — we built them specifically so they would be reported and removed. Why would anyone create a dozen mirrors of the same content on different platforms? Because we needed them to file a dozen separate takedown requests. Each request is logged by the platform. Each log contains the requester's identity, IP address, timestamp, and method. DMCA and GDPR takedown records are preserved by platforms for years.
They didn't think. They saw negative content — they pressed "report." For both NameSilo and xmrwallet. Same pattern, same speed, same platforms. They never stopped to ask: why does PhishDestroy keep creating new links? Why would a "crazy volunteer" keep making mirrors that keep getting taken down? Because every takedown is an exhibit. Every DMCA filing is a forensic fingerprint. And when investigators subpoena Google, Bing, Twitter, Trustpilot, and Medium — the pattern across both entities will be identical. Same requester. Same method. Same timeline. That's not two unrelated companies. That's one operation.
We've investigated hundreds of scam operations. None of them looked like this. Most phishing operators run, hide, or go silent when exposed. These didn't. They did the opposite:
This is what makes the case forensically interesting. The identical suppression pattern across both NameSilo and xmrwallet is the fingerprint we set out to capture. We didn't need to prove the connection through emails or payments — we proved it through behavior. We gave them targets. They took them down identically for both entities — same platforms, same speed, same methods. That behavioral pattern is the evidence. And it's the one thing they can't delete, because it's in the platform logs of every company they reported us to.
Database Poisoning & Telemetry Contamination
Because our goal is to protect people — and as long as xmrwallet.com was live, people were losing money. We built a Cloudflare Workers script that entered wallets into every xmrwallet domain (.com, .me, .cc, .biz, .net) continuously — the same input fields where real victims enter their actual keys. If it's a legitimate client-side wallet (as they claim), this doesn't affect anything. Seed phrase inputs on a legitimate wallet are processed locally. There is nothing to "attack."
But xmrwallet.com steals every seed phrase entered. We executed a systematic data-poisoning operation, injecting 21 million cryptographic decoys to render their stolen datasets operationally useless. We would not have stopped. Not until the site was dead. Whether they added hCaptcha, Cloudflare Turnstile, or anything else — we would have continued entering wallets and protecting people from them. That is literally what our name means.
Our wallets didn't just authorize and leave. Each session simulated realistic user behavior — clicking links, navigating pages, waiting variable intervals, mimicking different user types (explorer, sender, power user, newbie, paranoid). We understand how analytics systems work — and xmrwallet.com runs Google Analytics, Google Tag Manager, and a Google tracking pixel on an "anonymous" wallet. Our sessions were designed with strong randomization so the operator could not distinguish our entries from real victims by session behavior, timing, or navigation patterns. Every stolen wallet in their logs is buried in a haystack of ours.
After our tool ran for weeks, the operator added a CAPTCHA — a crude quadratic brute-force challenge solvable in ~0.1 seconds with Python. A legitimate wallet does not need a CAPTCHA on seed phrase input. Ledger doesn't have one. Trezor doesn't have one. MyMonero doesn't have one. No legitimate wallet does — because legitimate wallets process seeds locally. The only reason to add a CAPTCHA is if you're collecting and logging every input server-side. The CAPTCHA is itself evidence of the theft mechanism.
We expected them to deploy a real solution — hCaptcha, Cloudflare Turnstile, something competent. They didn't. They deployed a trivial quadratic brute-force solvable in 0.1 seconds. This tells you everything about their technical level. They were protecting their theft pipeline, not their users.
xmrwallet.com: 4,743 sessions · xmrwallet.me: 114,031 sessions. Sample log from one run. The tool was restarted and updated multiple times — when domains were removed, changed, or CAPTCHA was introduced. Complete logs across all runs total approximately 21 million successful entries across all xmrwallet domains, February – April 2026. Full dataset available to law enforcement on request.
5.4 RPS total across all actions — but no more than 1 authorization per 7-10 seconds. This is not a problem for a wallet that works on the client side, right? Unless it works on the server side. Unless they log every single input. Unless they steal everything and write the full log. Which is exactly what they do.
Is this an attack? No. We entered data into a public web form. That's it. We didn't bypass authentication, we didn't exploit vulnerabilities, we didn't access any system we weren't supposed to. We used the site exactly as intended — as a "wallet." If the site works as advertised (client-side only), our inputs are meaningless. If our inputs matter to them — that proves the theft mechanism exists.
We formally notified DDoS-Guard (their hosting provider) about the nature of our activity, described the seed-phrase collection mechanism, and provided server IPs. They never contacted us, never objected, never asked us to stop. Silence = no problem. Our script consumed under 50MB of RAM, ran at 5.4 requests per second — less than 1% of the server's capacity. We know approximately what server they used. Our traffic was invisible.
Now here's the beautiful part. As a "private client-side wallet," xmrwallet.com claims not to keep logs. But if they do keep logs (because they steal), they now have approximately the same number of entries as we do — 21 million. And if they're trying to process, evaluate, and drain each wallet? That's 21 million Monero wallets to scan, load, and check balances on. The computational cost of evaluating 21 million wallets is enormous. Every empty wallet wastes their time and resources. Every real victim's wallet is buried in a haystack of our entries. That was the entire point.
Want to accuse us of an attack? Request our logs. We'll provide gigabytes of data showing 21 million seed phrase inputs into your "legitimate client-side wallet." Explain to a court why a client-side wallet logged, processed, and attempted to use all of them.
Across all xmrwallet domains (.com, .me, .cc, .biz, .net), our tool logged approximately 21 million successful wallet entries. "Successful" means xmrwallet.com accepted the seed phrase, processed it server-side, and attempted to access the wallet — exactly as it does with real victims. We have logs of every single one. Every entry is proof that the site collects and processes seed phrases server-side. If it were truly "client-side only," there would be nothing to log, nothing to process, and no reason to add a CAPTCHA to stop us.
The irony: they tried to protect their theft mechanism instead of protecting themselves. They added CAPTCHAs to keep stealing. They should have been preparing a legal defense. Every CAPTCHA solve, every DDoS-Guard challenge, every server-side session — logged and timestamped. They were so busy defending their ability to rob people that they forgot someone was recording everything. We analyzed, documented, and defeated their CAPTCHA — it was trivial.
Monero seed phrases do not store the wallet's creation date (restore height). This creates a critical dilemma for the attacker: if they only scan recent blocks, they miss older, potentially massive wallets. Scammers are greedy. To guarantee they don't miss long-term holders, they are forced to scan the entire Monero blockchain — from the 2014 Genesis block to the present — for every single seed phrase.
Even with optimized infrastructure and local nodes, a full-chain cryptographic scan takes approximately 2 to 5 minutes of high CPU load per wallet.
We created absolute computational asymmetry: it costs us milliseconds to generate and inject a valid decoy, but it costs them tangible infrastructure, thousands of dollars in server fees, and massive operational risk to evaluate it. We didn't just pollute their database — we weaponized their own greed to bankrupt their computational resources.
This is why some consider our methods aggressive. We consider them proportional and fully ethical. No proxies. No botnets. No paid attack services. No illegal infrastructure. No collaboration with grey-market providers. Everything runs on standard Cloudflare Workers — lightweight, legal, transparent. We don't need expensive or illegal tools to protect people. Simple, legal solutions are more effective — and they hold up in court.
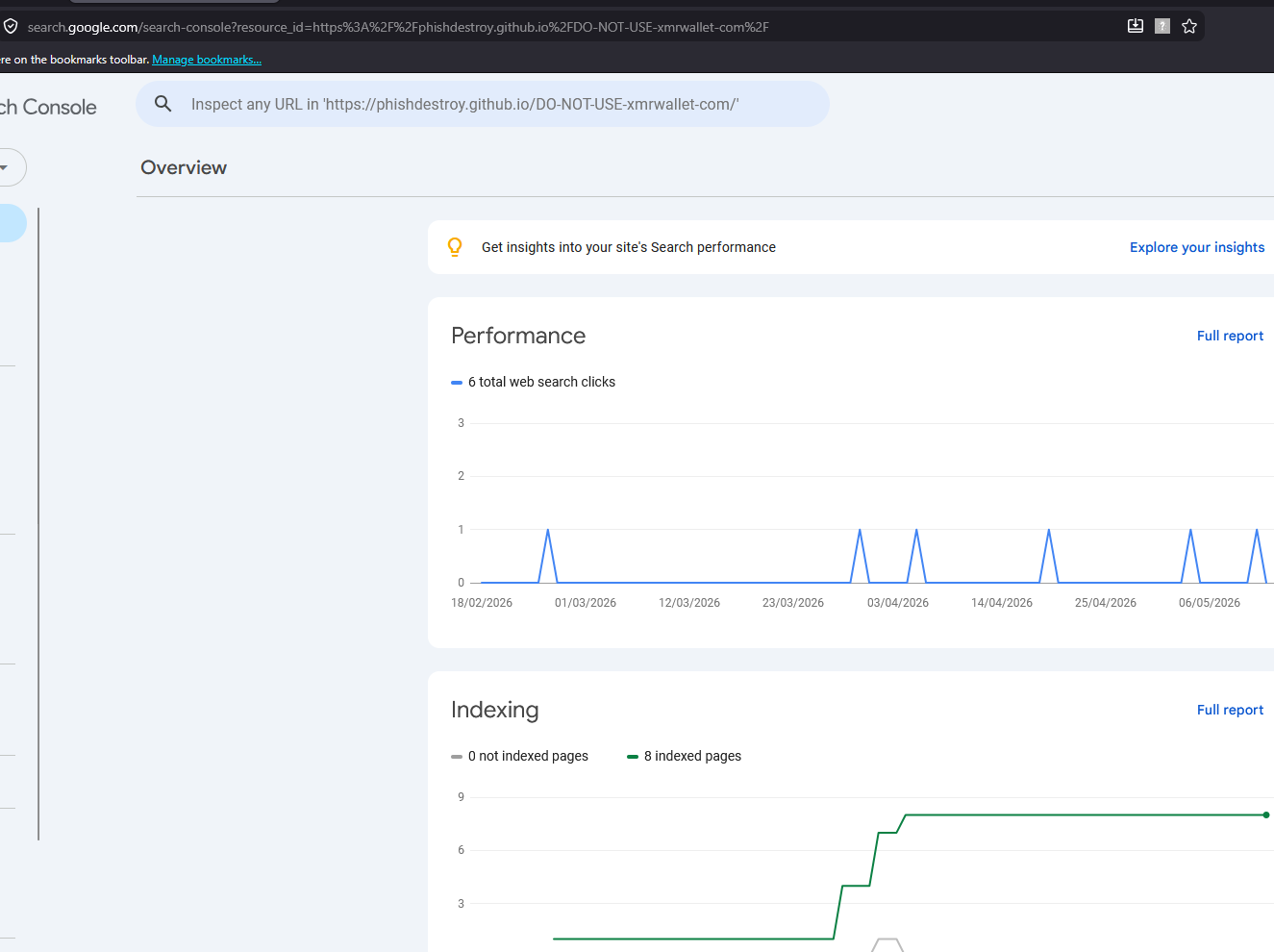
Google Search Console — phishdestroy.github.io/DO-NOT-USE-xmrwallet-com indexing & performance data.
There's no middle ground here.
A site is either a scam or it isn't. There are no half-measures. We don't care who profits from it, how much they pay, or who protects them. The operator is a criminal. The registrar either didn't know (negligence) or did know (complicity). The evidence points to the latter.
Did you make deliberate mistakes?
Yes. We intentionally left visible AI markers and borrowed behavioral patterns from other investigations — small errors that made the operator and registrar feel confident in their suppression campaign. We wanted them to underestimate us. We wanted them to press "report" with full confidence that it would work, that we were amateurs who would give up. Every confident suppression action they took is now a timestamped exhibit. The details will be published in an upcoming academic paper on online fraud forensics — specifically on behavioral fingerprinting of scam operators.
What's the endgame?
The evidence has been submitted to ICANN Contractual Compliance and federal law enforcement. The investigation continues through official channels. This archive exists so that nothing can be deleted, modified, or suppressed. Every claim is backed. Every screenshot is hashed. Every action is documented.
If they deny deleting reviews — we produce the Wayback Machine captures. If they deny ignoring complaints — we produce the delivery receipts. If they deny the connection — we produce the PR Newswire timestamps, the suppression pattern match, and the domain purchase records.
They removed 30-50+ links from search results across Google, Bing, and multiple platforms — for both entities. This proves one of two things: either they are extraordinarily stupid and don't realize that every takedown request is logged and creates a forensic trail, or they have a standing arrangement with someone to remove negative content. Either way, the logs exist, the pattern is identical for both companies, and it's all subpoenaable. This entire investigation was designed to produce exactly this dataset — for the academic paper and for law enforcement.
This was never a shouting match. This is a case file.
PhishDestroy Medium profile — one of multiple publication platforms used to document and distribute evidence.
PhishDestroy Research Team
Volunteer anti-phishing initiative — est. 2019
← Back to main investigation · Evidence archive · abuse@phishdestroy.io